- SpringBoot2ë¡œ Rest api 만들기(1) – Intellij Community 프로ì 트ìƒì„±
- SpringBoot2로 Rest api 만들기(2) – HelloWorld
- SpringBoot2ë¡œ Rest api 만들기(3) – H2 Database ì—°ë™
- SpringBoot2ë¡œ Rest api 만들기(4) – Swagger API 문서 ìžë™í™”
- SpringBoot2ë¡œ Rest api 만들기(5) – API ì¸í„°íŽ˜ì´ìŠ¤ ë° ê²°ê³¼ ë°ì´í„° 구조 설계
- SpringBoot2ë¡œ Rest api 만들기(6) – ControllerAdvice를 ì´ìš©í•œ Exception처리
- SpringBoot2ë¡œ Rest api 만들기(7) – MessageSource를 ì´ìš©í•œ Exception 처리
- SpringBoot2ë¡œ Rest api 만들기(8) – SpringSecurity 를 ì´ìš©í•œ ì¸ì¦ ë° ê¶Œí•œë¶€ì—¬
- SpringBoot2로 Rest api 만들기(9) – Spring Starter Unit Test
- SpringBoot2로 Rest api 만들기(10) – Social Login kakao
- SpringBoot2ë¡œ Rest api 만들기(11) – profileì„ ì´ìš©í•œ 환경별 ì„¤ì • 분리
- SpringBoot2ë¡œ Rest api 만들기(12) – Deploy & Nginx ì—°ë™ & 무중단 ë°°í¬ í•˜ê¸°
- SpringBoot2ë¡œ Rest api 만들기(13) – Jenkins ë°°í¬(Deploy) + Git Tag Rollback
- SpringBoot2ë¡œ Rest api 만들기(14) – 간단한 JPA 게시íŒ(board) 만들기
- SpringBoot2ë¡œ Rest api 만들기(15) – Redisë¡œ api ê²°ê³¼ ìºì‹±(Caching)처리
- SpringBoot2ë¡œ Rest api 만들기(16) – AOP와 Custom Annotationì„ ì´ìš©í•œ 금칙어(Forbidden Word) 처리
ì´ë²ˆ 시간ì—는 SpringSecurity를 ì´ìš©í•˜ì—¬ api ì„œë²„ì˜ ì‚¬ìš© ê¶Œí•œì„ ì œí•œí•˜ëŠ” ë°©ë²•ì— ëŒ€í•´ 알아보ë„ë¡ í•˜ê² ìŠµë‹ˆë‹¤. 지금까지 개발한 api는 권한 부여 ê¸°ëŠ¥ì´ ì—†ì–´ 누구나 íšŒì› ì •ë³´ë¥¼ 조회, ìƒì„± ë° ìˆ˜ì •, ì‚ì œë¥¼ í• ìˆ˜ 있었습니다. ì´ ìƒíƒœë¡œ api를 ì„œë¹„ìŠ¤ì— ë‚´ë³´ë‚¸ë‹¤ë©´ ë§Žì€ ë¬¸ì œê°€ ë°œìƒí• ê²ƒì€ ë¶ˆì„ ë³´ë“¯ 뻔한 ì¼ìž…니다. ì´ëŸ¬í•œ ë¬¸ì œë¥¼ 해결하기 위해 ì¸ì¦í•œ 회ì›ë§Œ api를 ì‚¬ìš©í• ìˆ˜ 있ë„ë¡ ê°œì„ í•´ ë³´ê² ìŠµë‹ˆë‹¤.
SpringSecurity
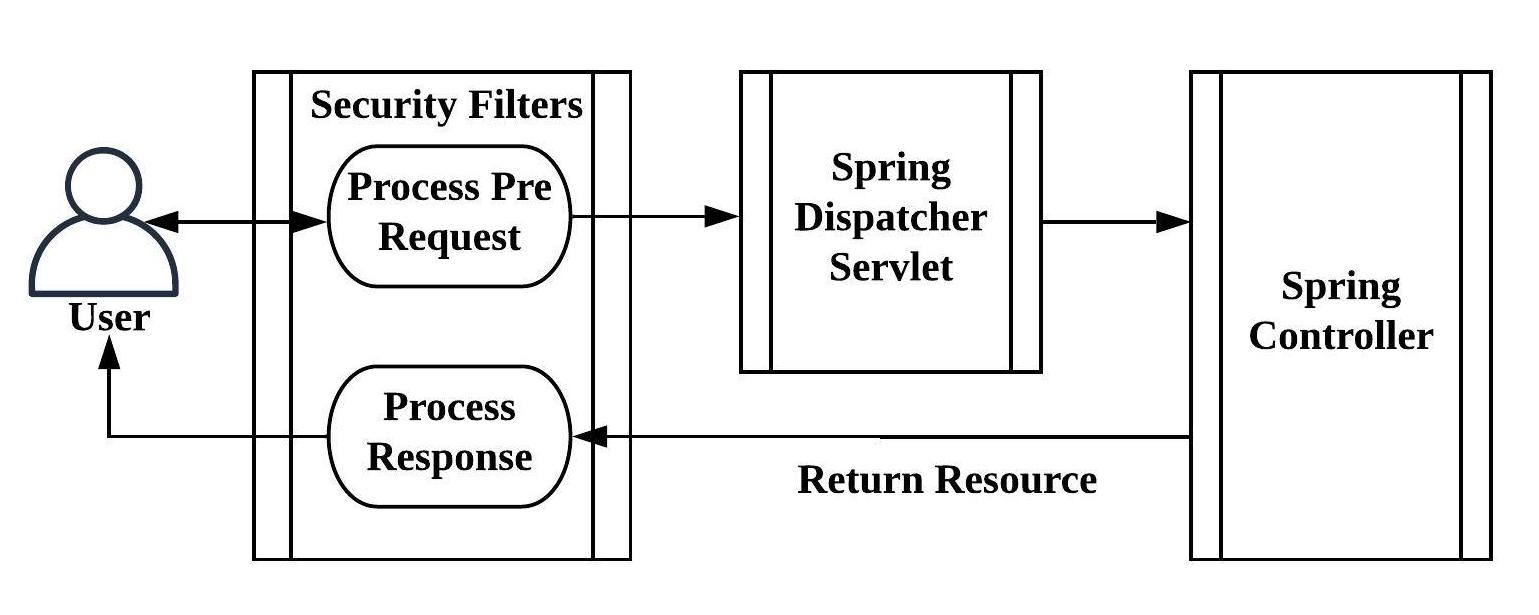
스프ë§ì—서는 ì¸ì¦ ë° ê¶Œí•œ 부여를 통해 ë¦¬ì†ŒìŠ¤ì˜ ì‚¬ìš©ì„ ì‰½ê²Œ ì»¨íŠ¸ë¡¤í• ìˆ˜ 있는 SpringSecurity framework를 ì œê³µí•˜ê³ ìžˆìŠµë‹ˆë‹¤. Spring bootê¸°ë°˜ì˜ í”„ë¡œì íŠ¸ì— SpringSecurity를 ì 용하면 보안 ê´€ë ¨ 처리를 ìžì²´ì 으로 êµ¬í˜„í• í•„ìš” ì—†ì´ ì‰½ê²Œ 필요한 ê¸°ëŠ¥ì„ êµ¬í˜„í• ìˆ˜ 있습니다. 간략하게 ì•„ëž˜ì˜ ê·¸ë¦¼ì²˜ëŸ¼ SpringSecurity는 Springì˜ DispatcherServlet ì•žë‹¨ì— Filter를 등ë¡ì‹œì¼œ ìš”ì²ì„ 가로챕니다. í´ë¼ì´ì–¸íŠ¸ì—게 리소스 ì ‘ê·¼ ê¶Œí•œì´ ì—†ì„ ê²½ìš°ì—” ì¸ì¦(ex:로그ì¸) 화면으로 ìžë™ìœ¼ë¡œ 리다ì´ë ‰íŠ¸ 합니다.
SpringSecurity Filter
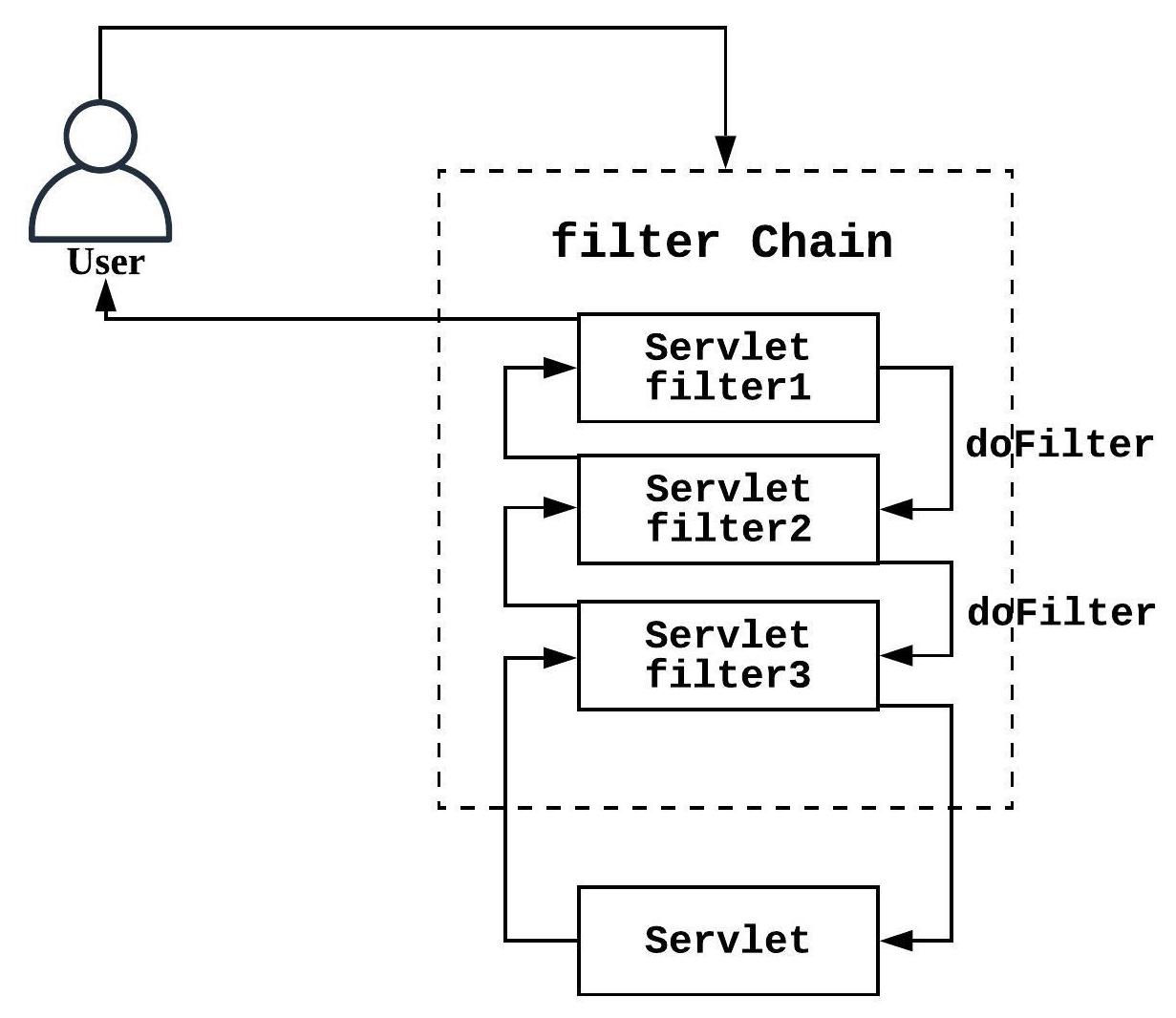
SpringSecurity는 기능별 í•„í„°ì˜ ì§‘í•©ìœ¼ë¡œ ë˜ì–´ìžˆê³ í•„í„°ì˜ ì²˜ë¦¬ 순서는 아래와 같습니다. 종류가 매우 많지만 여기서 중요한 ê²ƒì€ í•„í„°ì˜ ì²˜ë¦¬ 순서입니다. í´ë¼ì´ì–¸íŠ¸ê°€ 리소스를 ìš”ì²í• ë•Œ ì ‘ê·¼ ê¶Œí•œì´ ì—†ëŠ” 경우 기본ì 으로 ë¡œê·¸ì¸ í¼ìœ¼ë¡œ 보내게 ë˜ëŠ”ë° ê·¸ ì—í• ì„ í•˜ëŠ” 필터는 UsernamePasswordAuthenticationFilter입니다.
Rest Apiì—서는 ë¡œê·¸ì¸ í¼ì´ ë”°ë¡œ 없으므로 ì¸ì¦ ê¶Œí•œì´ ì—†ë‹¤ëŠ” 오류 Jsonì„ ë‚´ë ¤ì¤˜ì•¼ 하므로
UsernamePasswordAuthenticationFilter ì „ì— ê´€ë ¨ 처리를 넣어야 í•¨ì„ ì•Œ 수 있습니다.
- ChannelProcessingFilter
- SecurityContextPersistenceFilter
- ConcurrentSessionFilter
- HeaderWriterFilter
- CsrfFilter
- LogoutFilter
- X509AuthenticationFilter
- AbstractPreAuthenticatedProcessingFilter
- CasAuthenticationFilter
- UsernamePasswordAuthenticationFilter
- BasicAuthenticationFilter
- SecurityContextHolderAwareRequestFilter
- JaasApiIntegrationFilter
- RememberMeAuthenticationFilter
- AnonymousAuthenticationFilter
- SessionManagementFilter
- ExceptionTranslationFilter
- FilterSecurityInterceptor
- SwitchUserFilter
API ì¸ì¦ ë° ê¶Œí•œ 부여, ì œí•œëœ ë¦¬ì†ŒìŠ¤ì˜ ìš”ì²
- ì¸ì¦ì„ 위해 가입(Signup)ë° ë¡œê·¸ì¸(Signin) api를 구현합니다.
- 가입 ì‹œ ì œí•œëœ ë¦¬ì†ŒìŠ¤ì— ì ‘ê·¼í• ìˆ˜ 있는 ROLE_USER ê¶Œí•œì„ íšŒì›ì—게 부여합니다.
- SpringSecurity ì„¤ì •ì—는 ì ‘ê·¼ ì œí•œì´ í•„ìš”í•œ ë¦¬ì†ŒìŠ¤ì— ëŒ€í•´ì„œ ROLE_USER ê¶Œí•œì„ ê°€ì ¸ì•¼ ì ‘ê·¼ 가능하ë„ë¡ ì„¸íŒ…í•©ë‹ˆë‹¤.
- ê¶Œí•œì„ ê°€ì§„ 회ì›ì´ ë¡œê·¸ì¸ ì„±ê³µ 시엔 ë¦¬ì†ŒìŠ¤ì— ì ‘ê·¼í• ìˆ˜ 있는 Jwt 보안 í† í°ì„ 발급합니다.
- Jwt 보안 í† í°ìœ¼ë¡œ 회ì›ì€ ê¶Œí•œì´ í•„ìš”í•œ api 리소스를 ìš”ì²í•˜ì—¬ 사용합니다.
JWT 란?
JSON Web Token (JWT)ì€ JSON ê°ì²´ë¡œì„œ 당사ìžê°„ì— ì•ˆì „í•˜ê²Œ ì •ë³´ë¥¼ ì „ì†¡í• ìˆ˜ 있는 ìž‘ê³ ë…립ì ì¸ ë°©ë²•ì„ ì •ì˜í•˜ëŠ” 공개 표준 (RFC 7519)입니다. ìžì„¸í•œ ë‚´ìš©ì€ ì•„ëž˜ ë§í¬ì—ì„œ 확ì¸í• 수 있습니다.
https://jwt.io/introduction/
Jwt는 JSON ê°ì²´ë¥¼ 암호화하여 ë§Œë“ String값으로 기본ì 으로 암호화ë˜ì–´ìžˆì–´ 변조하기가 ì–´ë ¤ìš´ ì •ë³´ìž…ë‹ˆë‹¤. ë˜í•œ 다른 í† í°ê³¼ 달리 í† í° ìžì²´ì— ë°ì´í„°ë¥¼ ê°€ì§€ê³ ìžˆìŠµë‹ˆë‹¤. api 서버ì—서는 로그ì¸ì´ ì™„ë£Œëœ í´ë¼ì´ì–¸íŠ¸ì—게 회ì›ì„ êµ¬ë¶„í• ìˆ˜ 있는 ê°’ì„ ë„£ì€ Jwt í† í°ì„ ìƒì„±í•˜ì—¬ ë°œê¸‰í•˜ê³ , í´ë¼ì´ì–¸íŠ¸ëŠ” ì´ Jwt í† í°ì„ ì´ìš©í•˜ì—¬ ê¶Œí•œì´ í•„ìš”í•œ 리소스를 ì„œë²„ì— ìš”ì²í•˜ëŠ” ë° ì‚¬ìš©í• ìˆ˜ 있습니다. api서버는 í´ë¼ì´ì–¸íŠ¸ì—게서 ì „ë‹¬ë°›ì€ Jwt í† í°ì´ ìœ íš¨í•œì§€ 확ì¸í•˜ê³ 담겨있는 íšŒì› ì •ë³´ë¥¼ 확ì¸í•˜ì—¬ ì œí•œëœ ë¦¬ì†ŒìŠ¤ë¥¼ ì œê³µí•˜ëŠ”ë° ì´ìš©í• 수 있습니다.
build.gradleì— library 추가
SpringSecurity ë° Jwtê´€ë ¨ ë¼ì´ë¸ŒëŸ¬ë¦¬ë¥¼ build.gradleì— ì¶”ê°€í•©ë‹ˆë‹¤.
implementation 'org.springframework.boot:spring-boot-starter-security' implementation 'io.jsonwebtoken:jjwt:0.9.1'
JwtTokenProvider ìƒì„±
Jwt í† í° ìƒì„± ë° ìœ íš¨ì„± ê²€ì¦ì„ 하는 ì»´í¬ë„ŒíŠ¸ìž…니다. Jwt는 여러 가지 암호화 ì•Œê³ ë¦¬ì¦˜ì„ ì œê³µí•˜ë©° ì•Œê³ ë¦¬ì¦˜(SignatureAlgorithm.XXXXX)ê³¼ 비밀키(secretKey)를 ê°€ì§€ê³ í† í°ì„ ìƒì„±í•˜ê²Œ ë©ë‹ˆë‹¤. ì´ë•Œ claimì •ë³´ì—는 í† í°ì— 부가ì 으로 실어 보낼 ì •ë³´ë¥¼ ì„¸íŒ…í• ìˆ˜ 있습니다. claim ì •ë³´ì— íšŒì›ì„ êµ¬ë¶„í• ìˆ˜ 있는 ê°’ì„ ì„¸íŒ…í•˜ì˜€ë‹¤ê°€ í† í°ì´ 들어오면 해당 값으로 회ì›ì„ 구분하여 리소스를 ì œê³µí•˜ë©´ ë©ë‹ˆë‹¤. ê·¸ë¦¬ê³ Jwtí† í°ì—는 expire ì‹œê°„ì„ ì„¸íŒ…í• ìˆ˜ 있습니다. í† í° ë°œê¸‰ 후 ì¼ì • 시간 ì´í›„ì—는 í† í°ì„ 만료시키는 ë° ì‚¬ìš©í• ìˆ˜ 있습니다. resolveToken 메서드는 Http request headerì— ì„¸íŒ…ëœ í† í° ê°’ì„ ê°€ì ¸ì™€ ìœ íš¨ì„±ì„ ì²´í¬í•©ë‹ˆë‹¤. ì œí•œëœ ë¦¬ì†ŒìŠ¤ë¥¼ ìš”ì²í• ë•Œ Http headerì— í† í°ì„ 세팅하여 호출하면 ìœ íš¨ì„±ì„ ê²€ì¦í•˜ì—¬ ì‚¬ìš©ìž ì¸ì¦ì„ í• ìˆ˜ 있습니다.
package com.rest.api.config.security;
// import ìƒëžµ
@RequiredArgsConstructor
@Component
public class JwtTokenProvider { // JWT í† í°ì„ ìƒì„± ë° ê²€ì¦ ëª¨ë“ˆ
@Value("spring.jwt.secret")
private String secretKey;
private long tokenValidMilisecond = 1000L * 60 * 60; // 1시간만 í† í° ìœ íš¨
private final UserDetailsService userDetailsService;
@PostConstruct
protected void init() {
secretKey = Base64.getEncoder().encodeToString(secretKey.getBytes());
}
// Jwt í† í° ìƒì„±
public String createToken(String userPk, List<String> roles) {
Claims claims = Jwts.claims().setSubject(userPk);
claims.put("roles", roles);
Date now = new Date();
return Jwts.builder()
.setClaims(claims) // ë°ì´í„°
.setIssuedAt(now) // í† í° ë°œí–‰ì¼ìž
.setExpiration(new Date(now.getTime() + tokenValidMilisecond)) // set Expire Time
.signWith(SignatureAlgorithm.HS256, secretKey) // 암호화 ì•Œê³ ë¦¬ì¦˜, secretê°’ 세팅
.compact();
}
// Jwt í† í°ìœ¼ë¡œ ì¸ì¦ ì •ë³´ë¥¼ 조회
public Authentication getAuthentication(String token) {
UserDetails userDetails = userDetailsService.loadUserByUsername(this.getUserPk(token));
return new UsernamePasswordAuthenticationToken(userDetails, "", userDetails.getAuthorities());
}
// Jwt í† í°ì—ì„œ íšŒì› êµ¬ë³„ ì •ë³´ 추출
public String getUserPk(String token) {
return Jwts.parser().setSigningKey(secretKey).parseClaimsJws(token).getBody().getSubject();
}
// Requestì˜ Headerì—ì„œ token 파싱 : "X-AUTH-TOKEN: jwtí† í°"
public String resolveToken(HttpServletRequest req) {
return req.getHeader("X-AUTH-TOKEN");
}
// Jwt í† í°ì˜ ìœ íš¨ì„± + 만료ì¼ìž 확ì¸
public boolean validateToken(String jwtToken) {
try {
Jws<Claims> claims = Jwts.parser().setSigningKey(secretKey).parseClaimsJws(jwtToken);
return !claims.getBody().getExpiration().before(new Date());
} catch (Exception e) {
return false;
}
}
}
spring:
datasource:
url: jdbc:h2:tcp://localhost/~/test
driver-class-name: org.h2.Driver
username: sa
jpa:
database-platform: org.hibernate.dialect.H2Dialect
properties.hibernate.hbm2ddl.auto: update
showSql: true
messages:
basename: i18n/exception
encoding: UTF-8
jwt:
secret: govlepel@$&
JwtAuthenticationFilter ìƒì„±
Jwtê°€ ìœ íš¨í•œ í† í°ì¸ì§€ ì¸ì¦í•˜ê¸° 위한 Filter입니다. com.rest.api.config.security í•˜ìœ„ì— Class를 ìƒì„±í•©ë‹ˆë‹¤. ì´ í•„í„°ëŠ” Security ì„¤ì • ì‹œ UsernamePasswordAuthenticationFilterì•žì— ì„¸íŒ…í• ê²ƒìž…ë‹ˆë‹¤.
package com.rest.api.config.security;
// import ìƒëžµ
public class JwtAuthenticationFilter extends GenericFilterBean {
private JwtTokenProvider jwtTokenProvider;
// Jwt Provier 주입
public JwtAuthenticationFilter(JwtTokenProvider jwtTokenProvider) {
this.jwtTokenProvider = jwtTokenProvider;
}
// Requestë¡œ 들어오는 Jwt Tokenì˜ ìœ íš¨ì„±ì„ ê²€ì¦(jwtTokenProvider.validateToken)하는 filter를 filterChainì— ë“±ë¡í•©ë‹ˆë‹¤.
@Override
public void doFilter(ServletRequest request, ServletResponse response, FilterChain filterChain) throws IOException, ServletException {
String token = jwtTokenProvider.resolveToken((HttpServletRequest) request);
if (token != null && jwtTokenProvider.validateToken(token)) {
Authentication auth = jwtTokenProvider.getAuthentication(token);
SecurityContextHolder.getContext().setAuthentication(auth);
}
filterChain.doFilter(request, response);
}
}
SpringSecurity Configuration
ì„œë²„ì— ë³´ì•ˆ ì„¤ì •ì„ ì 용합니다. com.rest.api.config.security í•˜ìœ„ì— ë‹¤ìŒ Class를 작성합니다. 아무나 ì ‘ê·¼ 가능한 리소스는 permitAll()ë¡œ ì„¸íŒ…í•˜ê³ ë‚˜ë¨¸ì§€ 리소스는 다ìŒê³¼ ê°™ì´ ‘ROLE_USER’ ê¶Œí•œì´ í•„ìš”í•¨ìœ¼ë¡œ 명시합니다. anyRequest().hasRole(“USER”) ë˜ëŠ” anyRequest().authenticated()는 ë™ì¼í•œ ë™ìž‘ì„ í•©ë‹ˆë‹¤.
위ì—ì„œ ì„¤ëª…í–ˆë“¯ì´ í•´ë‹¹ filter는 UsernamePasswordAuthenticationFilter ì•žì— ì„¤ì •í•´ì•¼ 합니다. SpringSecurity ì ìš© 후ì—는 ëª¨ë“ ë¦¬ì†ŒìŠ¤ì— ëŒ€í•œ ì ‘ê·¼ì´ ì œí•œë˜ë¯€ë¡œ. Swagger 페ì´ì§€ì— 대해서는 예외를 ì 용해야 페ì´ì§€ì— ì ‘ê·¼í• ìˆ˜ 있습니다. 리소스 ì ‘ê·¼ ì œí•œ 표현ì‹ì€ 여러 가지가 있으며 다ìŒê³¼ 같습니다.
hasIpAddress(ip) – ì ‘ê·¼ìžì˜ IP주소가 ë§¤ì¹ í•˜ëŠ”ì§€ 확ì¸í•©ë‹ˆë‹¤.
hasRole(role) – ì—í• ì´ ë¶€ì—¬ëœ ê¶Œí•œ(Granted Authority)ê³¼ ì¼ì¹˜í•˜ëŠ”지 확ì¸í•©ë‹ˆë‹¤.
hasAnyRole(role) – ë¶€ì—¬ëœ ì—í• ì¤‘ ì¼ì¹˜í•˜ëŠ” í•ëª©ì´ 있는지 확ì¸í•©ë‹ˆë‹¤.
ex) access = “hasAnyRole(‘ROLE_USER’,’ROLE_ADMIN’)”
permitAll – ëª¨ë“ ì ‘ê·¼ìžë¥¼ í•ìƒ 승ì¸í•©ë‹ˆë‹¤.
denyAll – ëª¨ë“ ì‚¬ìš©ìžì˜ ì ‘ê·¼ì„ ê±°ë¶€í•©ë‹ˆë‹¤.
anonymous – 사용ìžê°€ ìµëª… 사용ìžì¸ì§€ 확ì¸í•©ë‹ˆë‹¤.
authenticated – ì¸ì¦ëœ 사용ìžì¸ì§€ 확ì¸í•©ë‹ˆë‹¤.
rememberMe – 사용ìžê°€ remember me를 사용해 ì¸ì¦í–ˆëŠ”지 확ì¸í•©ë‹ˆë‹¤.
fullyAuthenticated – 사용ìžê°€ ëª¨ë“ í¬ë¦¬ë´ì…œì„ 갖춘 ìƒíƒœì—ì„œ ì¸ì¦í–ˆëŠ”지 확ì¸í•©ë‹ˆë‹¤.
package com.rest.api.config.security;
// import ìƒëžµ
@RequiredArgsConstructor
@Configuration
public class SecurityConfiguration extends WebSecurityConfigurerAdapter {
private final JwtTokenProvider jwtTokenProvider;
@Bean
@Override
public AuthenticationManager authenticationManagerBean() throws Exception {
return super.authenticationManagerBean();
}
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.httpBasic().disable() // rest api ì´ë¯€ë¡œ ê¸°ë³¸ì„¤ì • 사용안함. ê¸°ë³¸ì„¤ì •ì€ ë¹„ì¸ì¦ì‹œ 로그ì¸í¼ 화면으로 리다ì´ë ‰íŠ¸ ëœë‹¤.
.csrf().disable() // rest apiì´ë¯€ë¡œ csrf ë³´ì•ˆì´ í•„ìš”ì—†ìœ¼ë¯€ë¡œ disable처리.
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS) // jwt token으로 ì¸ì¦í•˜ë¯€ë¡œ ì„¸ì…˜ì€ í•„ìš”ì—†ìœ¼ë¯€ë¡œ ìƒì„±ì•ˆí•¨.
.and()
.authorizeRequests() // ë‹¤ìŒ ë¦¬í€˜ìŠ¤íŠ¸ì— ëŒ€í•œ 사용권한 ì²´í¬
.antMatchers("/*/signin", "/*/signup").permitAll() // 가입 ë° ì¸ì¦ 주소는 누구나 ì ‘ê·¼ê°€ëŠ¥
.antMatchers(HttpMethod.GET, "helloworld/**").permitAll() // hellowworldë¡œ 시작하는 GETìš”ì² ë¦¬ì†ŒìŠ¤ëŠ” 누구나 ì ‘ê·¼ê°€ëŠ¥
.anyRequest().hasRole("USER") // 그외 나머지 ìš”ì²ì€ ëª¨ë‘ ì¸ì¦ëœ 회ì›ë§Œ ì ‘ê·¼ 가능
.and()
.addFilterBefore(new JwtAuthenticationFilter(jwtTokenProvider), UsernamePasswordAuthenticationFilter.class); // jwt token 필터를 id/password ì¸ì¦ í•„í„° ì „ì— ë„£ëŠ”ë‹¤
}
@Override // ignore check swagger resource
public void configure(WebSecurity web) {
web.ignoring().antMatchers("/v2/api-docs", "/swagger-resources/**",
"/swagger-ui.html", "/webjars/**", "/swagger/**");
}
}
Custom UserDetailsService ì •ì˜
í† í°ì— ì„¸íŒ…ëœ ìœ ì € ì •ë³´ë¡œ 회ì›ì •ë³´ë¥¼ 조회하는 UserDetailsService를 ìž¬ì •ì˜ í•©ë‹ˆë‹¤.
@RequiredArgsConstructor
@Service
public class CustomUserDetailService implements UserDetailsService {
private final UserJpaRepo userJpaRepo;
public UserDetails loadUserByUsername(String userPk) {
return userJpaRepo.findById(Long.valueOf(userPk)).orElseThrow(CUserNotFoundException::new);
}
}
User Entity ìˆ˜ì •
SpringSecurityì˜ ë³´ì•ˆì„ ì 용하기 위해 User entityì— UserDetails Class를 ìƒì†ë°›ì•„ 추가 ì •ë³´ë¥¼ ìž¬ì •ì˜ í•©ë‹ˆë‹¤. roles는 회ì›ì´ ê°€ì§€ê³ ìžˆëŠ” 권한 ì •ë³´ì´ê³ , ê°€ìž…í–ˆì„ ë•ŒëŠ” 기본 “ROLE_USER”ê°€ 세팅ë©ë‹ˆë‹¤. ê¶Œí•œì€ íšŒì›ë‹¹ 여러 개가 세팅ë 수 있으므로 Collection으로 ì„ ì–¸í•©ë‹ˆë‹¤.
getUsernameì€ securityì—ì„œ 사용하는 íšŒì› êµ¬ë¶„ id입니다. ì—¬ê¸°ì„ uidë¡œ 변경합니다.
ë‹¤ìŒ ê°’ë“¤ì€ Securityì—ì„œ 사용하는 íšŒì› ìƒíƒœ 값입니다. ì—¬ê¸°ì„ ëª¨ë‘ ì‚¬ìš© 안 하므로 trueë¡œ ì„¤ì •í•©ë‹ˆë‹¤.
Json결과로 ì¶œë ¥ 안 í• ë°ì´í„°ëŠ” @JsonProperty(access = JsonProperty.Access.WRITE_ONLY) 어노테ì´ì…˜ì„ ì„ ì–¸í•´ì¤ë‹ˆë‹¤.
isAccountNonExpired – ê³„ì •ì´ ë§Œë£Œê°€ 안ë˜ì—ˆëŠ”지
isAccountNonLocked – ê³„ì •ì´ ìž ê¸°ì§€ 않았는지
isCredentialsNonExpired – ê³„ì • 패스워드가 만료 안ë¬ëŠ”지
isEnabled – ê³„ì •ì´ ì‚¬ìš© 가능한지
@Builder // builder를 ì‚¬ìš©í• ìˆ˜ 있게 합니다.
@Entity // jpa entityìž„ì„ ì•Œë¦½ë‹ˆë‹¤.
@Getter // user í•„ë“œê°’ì˜ getter를 ìžë™ìœ¼ë¡œ ìƒì„±í•©ë‹ˆë‹¤.
@NoArgsConstructor // ì¸ìžì—†ëŠ” ìƒì„±ìžë¥¼ ìžë™ìœ¼ë¡œ ìƒì„±í•©ë‹ˆë‹¤.
@AllArgsConstructor // ì¸ìžë¥¼ ëª¨ë‘ ê°–ì¶˜ ìƒì„±ìžë¥¼ ìžë™ìœ¼ë¡œ ìƒì„±í•©ë‹ˆë‹¤.
@Table(name = "user") // 'user' í…Œì´ë¸”ê³¼ 매핑ë¨ì„ 명시
public class User implements UserDetails {
@Id // pk
@GeneratedValue(strategy = GenerationType.IDENTITY)
private long msrl;
@Column(nullable = false, unique = true, length = 30)
private String uid;
@JsonProperty(access = JsonProperty.Access.WRITE_ONLY)
@Column(nullable = false, length = 100)
private String password;
@Column(nullable = false, length = 100)
private String name;
@ElementCollection(fetch = FetchType.EAGER)
@Builder.Default
private List<String> roles = new ArrayList<>();
@Override
public Collection<? extends GrantedAuthority> getAuthorities() {
return this.roles.stream().map(SimpleGrantedAuthority::new).collect(Collectors.toList());
}
@JsonProperty(access = JsonProperty.Access.WRITE_ONLY)
@Override
public String getUsername() {
return this.uid;
}
@JsonProperty(access = JsonProperty.Access.WRITE_ONLY)
@Override
public boolean isAccountNonExpired() {
return true;
}
@JsonProperty(access = JsonProperty.Access.WRITE_ONLY)
@Override
public boolean isAccountNonLocked() {
return true;
}
@JsonProperty(access = JsonProperty.Access.WRITE_ONLY)
@Override
public boolean isCredentialsNonExpired() {
return true;
}
@JsonProperty(access = JsonProperty.Access.WRITE_ONLY)
@Override
public boolean isEnabled() {
return true;
}
}
UserJpaRepoì— findByUid추가
íšŒì› ê°€ìž… ì‹œ 가입한 ì´ë©”ì¼ ì¡°íšŒë¥¼ 위해 ë‹¤ìŒ ë©”ì„œë“œë¥¼ ì„ ì–¸í•©ë‹ˆë‹¤.
public interface UserJpaRepo extends JpaRepository<User, Integer> {
Optional<User> findByUid(String email);
}
ë¡œê·¸ì¸ ì˜ˆì™¸ 추가
CEmailSigninFailedException ìƒì„±
public class CEmailSigninFailedException extends RuntimeException {
public CEmailSigninFailedException(String msg, Throwable t) {
super(msg, t);
}
public CEmailSigninFailedException(String msg) {
super(msg);
}
public CEmailSigninFailedException() {
super();
}
}
# exception_en.yml emailSigninFailed: code: "-1001" msg: "Your account does not exist or your email or password is incorrect." # exception_ko.yml emailSigninFailed: code: "-1001" msg: "ê³„ì •ì´ ì¡´ìž¬í•˜ì§€ 않거나 ì´ë©”ì¼ ë˜ëŠ” 비밀번호가 ì •í™•í•˜ì§€ 않습니다."
# ExceptionAdvice
@ExceptionHandler(CEmailSigninFailedException.class)
@ResponseStatus(HttpStatus.INTERNAL_SERVER_ERROR)
protected CommonResult emailSigninFailed(HttpServletRequest request, CEmailSigninFailedException e) {
return responseService.getFailResult(Integer.valueOf(getMessage("emailSigninFailed.code")), getMessage("emailSigninFailed.msg"));
}
가입 / ë¡œê·¸ì¸ Controller 추가
ë¡œê·¸ì¸ ì„±ê³µ ì‹œì—는 결과로 Jwtí† í°ì„ 발급합니다.
가입 ì‹œì—는 패스워드 ì¸ì½”ë”©ì„ ìœ„í•´ passwordEncoderì„¤ì •ì„ í•©ë‹ˆë‹¤. 기본 ì„¤ì •ì€ bcrypt encodingì´ ì‚¬ìš©ë©ë‹ˆë‹¤.
@Api(tags = {"1. Sign"})
@RequiredArgsConstructor
@RestController
@RequestMapping(value = "/v1")
public class SignController {
private final UserJpaRepo userJpaRepo;
private final JwtTokenProvider jwtTokenProvider;
private final ResponseService responseService;
private final PasswordEncoder passwordEncoder;
@ApiOperation(value = "로그ì¸", notes = "ì´ë©”ì¼ íšŒì› ë¡œê·¸ì¸ì„ 한다.")
@PostMapping(value = "/signin")
public SingleResult<String> signin(@ApiParam(value = "회ì›ID : ì´ë©”ì¼", required = true) @RequestParam String id,
@ApiParam(value = "비밀번호", required = true) @RequestParam String password) {
User user = userJpaRepo.findByUid(id).orElseThrow(CEmailSigninFailedException::new);
if (!passwordEncoder.matches(password, user.getPassword()))
throw new CEmailSigninFailedException();
return responseService.getSingleResult(jwtTokenProvider.createToken(String.valueOf(user.getMsrl()), user.getRoles()));
}
@ApiOperation(value = "가입", notes = "회ì›ê°€ìž…ì„ í•œë‹¤.")
@PostMapping(value = "/signup")
public CommonResult signin(@ApiParam(value = "회ì›ID : ì´ë©”ì¼", required = true) @RequestParam String id,
@ApiParam(value = "비밀번호", required = true) @RequestParam String password,
@ApiParam(value = "ì´ë¦„", required = true) @RequestParam String name) {
userJpaRepo.save(User.builder()
.uid(id)
.password(passwordEncoder.encode(password))
.name(name)
.roles(Collections.singletonList("ROLE_USER"))
.build());
return responseService.getSuccessResult();
}
}
SpringRestApiApplicationì— passwordEncoder bean 추가
@SpringBootApplication
public class SpringRestApiApplication {
public static void main(String[] args) {
SpringApplication.run(SpringRestApiApplication.class, args);
}
@Bean
public PasswordEncoder passwordEncoder() {
return PasswordEncoderFactories.createDelegatingPasswordEncoder();
}
}
UserController ìˆ˜ì •
ìœ íš¨í•œ Jwtí† í°ì„ ì„¤ì •í•´ì•¼ë§Œ User 리소스를 ì‚¬ìš©í• ìˆ˜ 있ë„ë¡ Headerì— X-AUTH-TOKENì„ ì¸ìžë¡œ ë°›ë„ë¡ ì„ ì–¸í•©ë‹ˆë‹¤.
@Api(tags = {"2. User"})
@RequiredArgsConstructor
@RestController
@RequestMapping(value = "/v1")
public class UserController {
private final UserJpaRepo userJpaRepo;
private final ResponseService responseService; // 결과를 ì²˜ë¦¬í• Service
@ApiImplicitParams({
@ApiImplicitParam(name = "X-AUTH-TOKEN", value = "ë¡œê·¸ì¸ ì„±ê³µ 후 access_token", required = true, dataType = "String", paramType = "header")
})
@ApiOperation(value = "íšŒì› ë¦¬ìŠ¤íŠ¸ 조회", notes = "ëª¨ë“ íšŒì›ì„ 조회한다")
@GetMapping(value = "/users")
public ListResult<User> findAllUser() {
// ê²°ê³¼ë°ì´í„°ê°€ 여러건ì¸ê²½ìš° getListResult를 ì´ìš©í•´ì„œ 결과를 ì¶œë ¥í•œë‹¤.
return responseService.getListResult(userJpaRepo.findAll());
}
@ApiImplicitParams({
@ApiImplicitParam(name = "X-AUTH-TOKEN", value = "ë¡œê·¸ì¸ ì„±ê³µ 후 access_token", required = false, dataType = "String", paramType = "header")
})
@ApiOperation(value = "íšŒì› ë‹¨ê±´ 조회", notes = "회ì›ë²ˆí˜¸(msrl)ë¡œ 회ì›ì„ 조회한다")
@GetMapping(value = "/user")
public SingleResult<User> findUserById(@ApiParam(value = "언어", defaultValue = "ko") @RequestParam String lang) {
// SecurityContextì—ì„œ ì¸ì¦ë°›ì€ 회ì›ì˜ ì •ë³´ë¥¼ 얻어온다.
Authentication authentication = SecurityContextHolder.getContext().getAuthentication();
String id = authentication.getName();
// ê²°ê³¼ë°ì´í„°ê°€ 단ì¼ê±´ì¸ê²½ìš° getSingleResult를 ì´ìš©í•´ì„œ 결과를 ì¶œë ¥í•œë‹¤.
return responseService.getSingleResult(userJpaRepo.findByUid(id).orElseThrow(CUserNotFoundException::new));
}
@ApiImplicitParams({
@ApiImplicitParam(name = "X-AUTH-TOKEN", value = "ë¡œê·¸ì¸ ì„±ê³µ 후 access_token", required = true, dataType = "String", paramType = "header")
})
@ApiOperation(value = "íšŒì› ìˆ˜ì •", notes = "회ì›ì •ë³´ë¥¼ ìˆ˜ì •í•œë‹¤")
@PutMapping(value = "/user")
public SingleResult<User> modify(
@ApiParam(value = "회ì›ë²ˆí˜¸", required = true) @RequestParam int msrl,
@ApiParam(value = "회ì›ì´ë¦„", required = true) @RequestParam String name) {
User user = User.builder()
.msrl(msrl)
.name(name)
.build();
return responseService.getSingleResult(userJpaRepo.save(user));
}
@ApiImplicitParams({
@ApiImplicitParam(name = "X-AUTH-TOKEN", value = "ë¡œê·¸ì¸ ì„±ê³µ 후 access_token", required = true, dataType = "String", paramType = "header")
})
@ApiOperation(value = "íšŒì› ì‚ì œ", notes = "userIdë¡œ 회ì›ì •ë³´ë¥¼ ì‚ì œí•œë‹¤")
@DeleteMapping(value = "/user/{msrl}")
public CommonResult delete(
@ApiParam(value = "회ì›ë²ˆí˜¸", required = true) @PathVariable int msrl) {
userJpaRepo.deleteById(msrl);
// 성공 ê²°ê³¼ ì •ë³´ë§Œ 필요한경우 getSuccessResult()를 ì´ìš©í•˜ì—¬ 결과를 ì¶œë ¥í•œë‹¤.
return responseService.getSuccessResult();
}
}
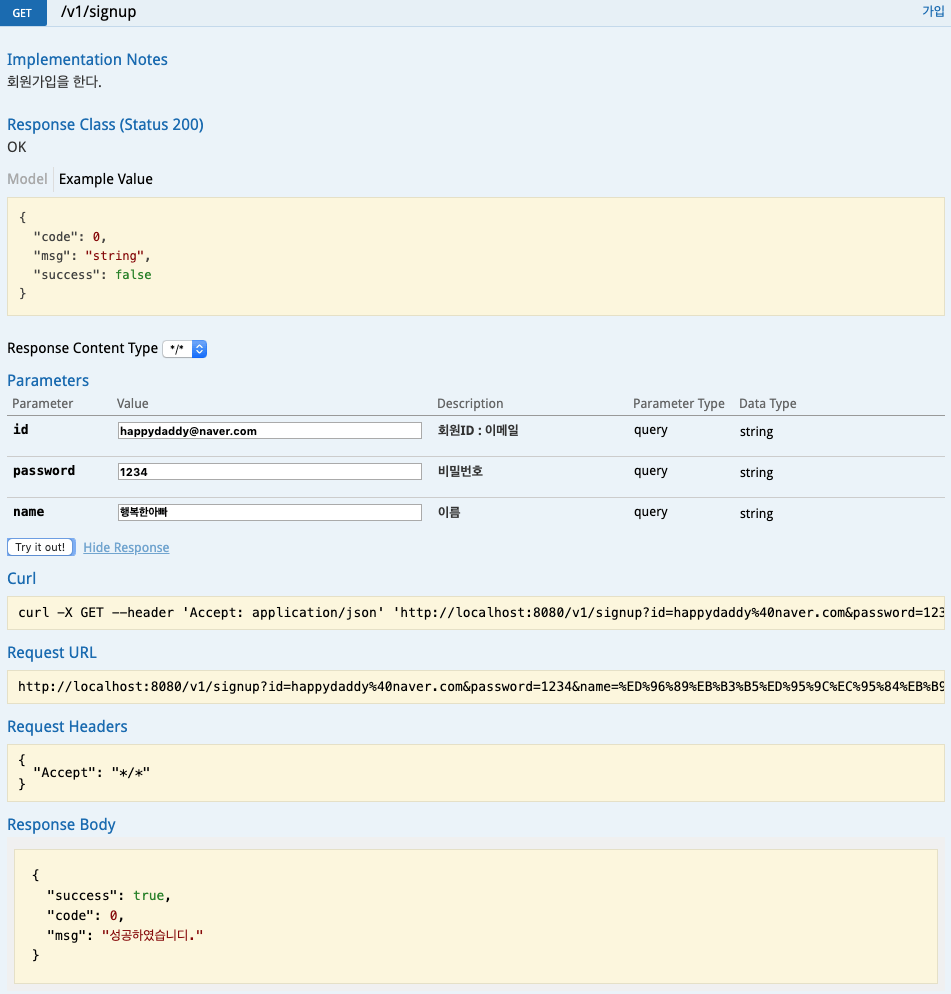
Test Swagger
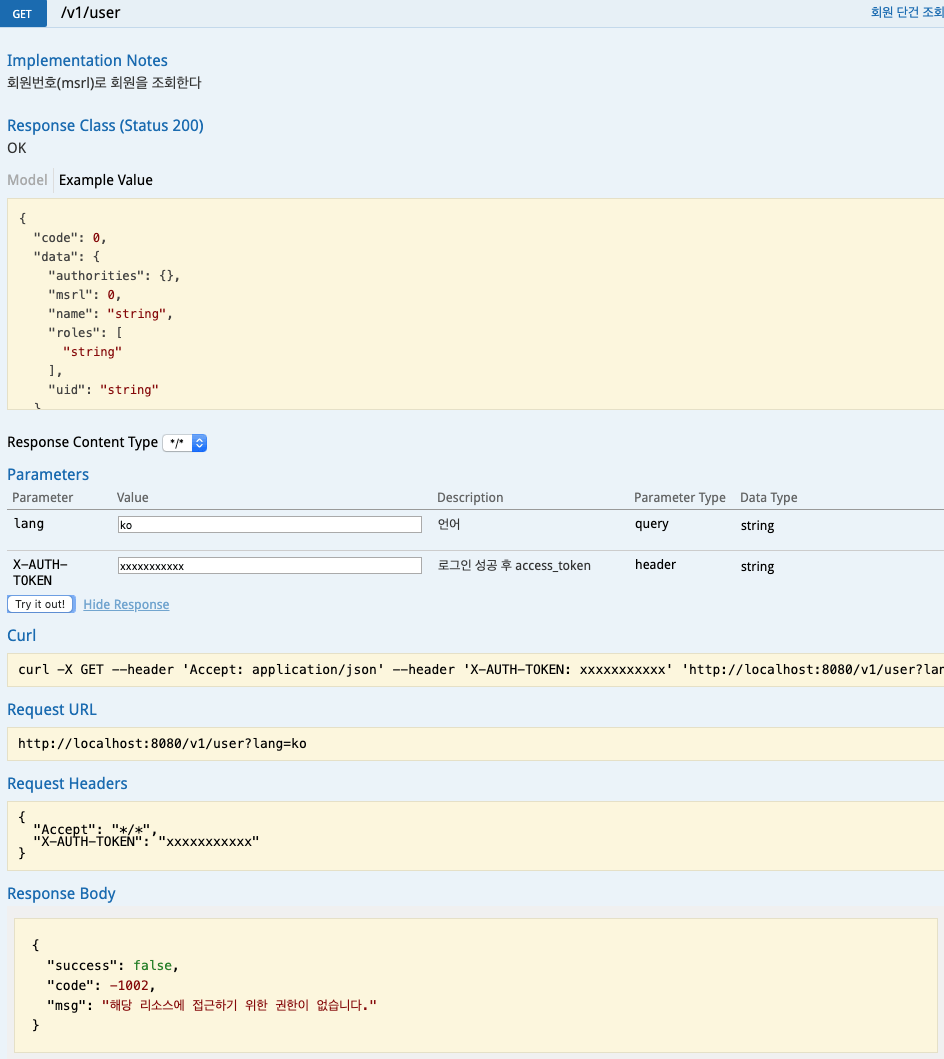
회ì›ê°€ìž… -> ë¡œê·¸ì¸ -> í† í°ì„ ì´ìš©í•œ 회ì›ì •ë³´ 조회순으로 Test를 진행합니다.

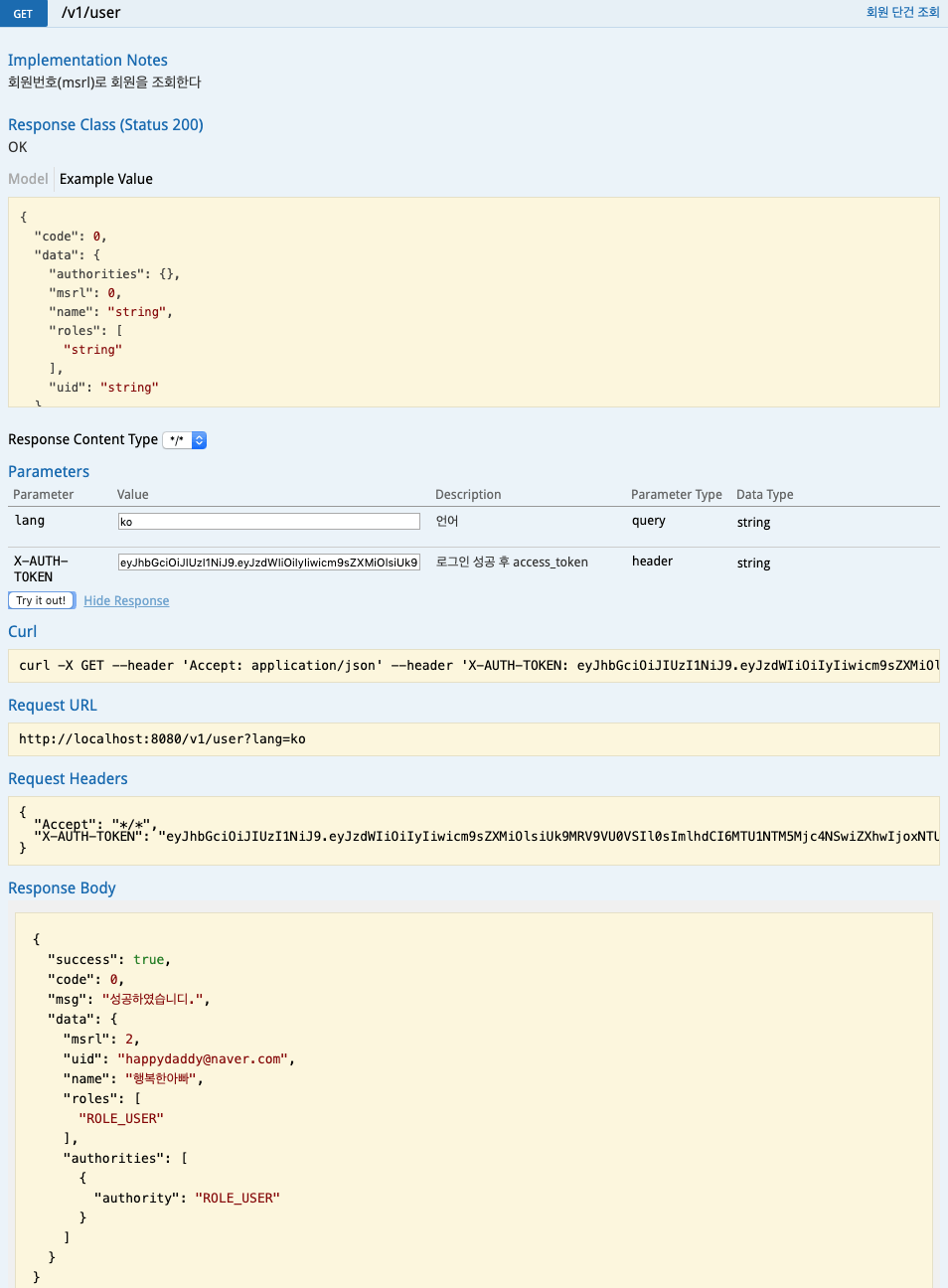
ì¸ì¦ í† í°ì„ 발급받아 ì œí•œëœ ë¦¬ì†ŒìŠ¤ì— ì ‘ê·¼í•˜ëŠ” ê²ƒì— ëŒ€í•œ 테스트가 완료ë˜ì—ˆìŠµë‹ˆë‹¤.
예외 처리 보완
다ìŒê³¼ ê°™ì€ ìƒí™©ì„ 예측해 ë³¼ 수 있습니다.
- Jwtí† í° ì—†ì´ api를 í˜¸ì¶œí•˜ì˜€ì„ ê²½ìš°
- 형ì‹ì— 맞지 않거나 ë§Œë£Œëœ Jwtí† í°ìœ¼ë¡œ api를 호출한 경우
- Jwtí† í°ìœ¼ë¡œ api를 호출하였으나 해당 ë¦¬ì†ŒìŠ¤ì— ëŒ€í•œ ê¶Œí•œì´ ì—†ëŠ” 경우
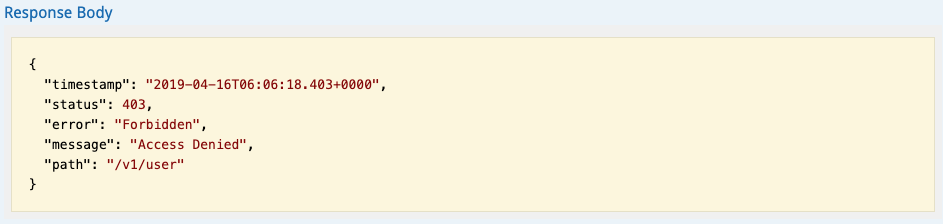
1,2 ë²ˆì€ ë‹¤ìŒê³¼ ê°™ì€ ì˜¤ë¥˜ê°€ ë°œìƒí•©ë‹ˆë‹¤.
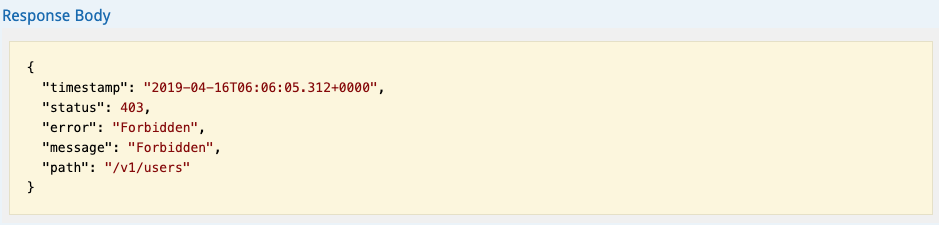
3ë²ˆì€ ë‹¤ìŒê³¼ ê°™ì€ ì˜¤ë¥˜ê°€ ë°œìƒí•©ë‹ˆë‹¤.
커스텀 예외 처리가 ì ìš©ì´ ì•ˆë˜ëŠ” ì´ìœ
ìœ„ì˜ ìƒí™©ì—ì„œ 커스텀으로 ì ìš©í•œ 예외 처리가 ì ìš©ì´ ì•ˆ ë˜ëŠ” ì´ìœ 는 í•„í„°ë§ì˜ 순서 때문입니다. 지금까지 ì ìš©í•œ 커스텀 예외처리는 ControllerAdvice 즉 Springì´ ì²˜ë¦¬ 가능한 ì˜ì—까지 리퀘스트가 ë„달해야 ì²˜ë¦¬í• ìˆ˜ 있습니다. 그러나 SpringSecurity는 Spring 앞단ì—ì„œ í•„í„°ë§ì„ 하기 때문ì—, 해당 ìƒí™©ì˜ exeptionì´ Springì˜ DispatcherServlet까지 ë„달하지 않게 ë©ë‹ˆë‹¤.
1,2 ë²ˆì— ëŒ€í•œ í•´ê²°ì±…
ì˜¨ì „í•œ Jwtê°€ ì „ë‹¬ì´ ì•ˆë 경우는 í† í° ì¸ì¦ 처리 ìžì²´ê°€ 불가능하기 때문ì—, í† í° ê²€ì¦ ë‹¨ì—ì„œ 프로세스가 ë나버리게 ë©ë‹ˆë‹¤. 해당 예외를 ìž¡ì•„ë‚´ë ¤ë©´ SpringSecurityì—ì„œ ì œê³µí•˜ëŠ” AuthenticationEntryPoint를 ìƒì†ë°›ì•„ ìž¬ì •ì˜ í•´ì•¼ 합니다. 예외가 ë°œìƒí• 경우 아래ì—서는 /exception/entrypointë¡œ í¬ì›Œë”©ë˜ë„ë¡ ì²˜ë¦¬í•˜ì˜€ìŠµë‹ˆë‹¤.
CustomAuthenticationEntryPoint 작성
package com.rest.api.config.security;
import lombok.extern.slf4j.Slf4j;
import org.springframework.security.core.AuthenticationException;
import org.springframework.security.web.AuthenticationEntryPoint;
import org.springframework.stereotype.Component;
import javax.servlet.RequestDispatcher;
import javax.servlet.ServletException;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
@Slf4j
@Component
public class CustomAuthenticationEntryPoint implements AuthenticationEntryPoint {
@Override
public void commence(HttpServletRequest request, HttpServletResponse response, AuthenticationException ex) throws IOException,
ServletException {
response.sendRedirect("/exception/entrypoint");
}
}
ExceptionController 작성
controller packageí•˜ìœ„ì— exception package를 ìƒì„±í•˜ê³ ExceptionController를 작성합니다. ë‚´ìš©ì€ /exception/entrypointë¡œ 주소가 들어오면 CAuthenticationEntryPointExceptionì„ ë°œìƒì‹œí‚¤ë¼ëŠ” 것입니다.
package com.rest.api.controller.exception;
// import ìƒëžµ
@RequiredArgsConstructor
@RestController
@RequestMapping(value = "/exception")
public class ExceptionController {
@GetMapping(value = "/entrypoint")
public CommonResult entrypointException() {
throw new CAuthenticationEntryPointException();
}
}
CAuthenticationEntryPointException ìƒì„±
package com.rest.api.advice.exception;
public class CAuthenticationEntryPointException extends RuntimeException {
public CAuthenticationEntryPointException(String msg, Throwable t) {
super(msg, t);
}
public CAuthenticationEntryPointException(String msg) {
super(msg);
}
public CAuthenticationEntryPointException() {
super();
}
}
Message 내용 추가
// exception_ko.yml entryPointException: code: "-1002" msg: "해당 ë¦¬ì†ŒìŠ¤ì— ì ‘ê·¼í•˜ê¸° 위한 ê¶Œí•œì´ ì—†ìŠµë‹ˆë‹¤." // exception_en.yml entryPointException: code: "-1002" msg: "You do not have permission to access this resource.
ExceptionAdvice 내용 추가
@ExceptionHandler(CAuthenticationEntryPointException.class)
public CommonResult authenticationEntryPointException(HttpServletRequest request, CAuthenticationEntryPointException e) {
return responseService.getFailResult(Integer.valueOf(getMessage("entryPointException.code")), getMessage("entryPointException.msg"));
}
SpringSecurityConfigurationì— CustomAuthenticationEntryPoint ì„¤ì • 추가
.exceptionHandling().authenticationEntryPoint(new CustomAuthenticationEntryPoint())를 ì¶”ê°€í•˜ê³ /exception주소를 PermitAll()ì— ì¶”ê°€í•œë‹¤.
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.httpBasic().disable() // rest api ì´ë¯€ë¡œ ê¸°ë³¸ì„¤ì • 사용안함. ê¸°ë³¸ì„¤ì •ì€ ë¹„ì¸ì¦ì‹œ 로그ì¸í¼ 화면으로 리다ì´ë ‰íŠ¸ ëœë‹¤.
.csrf().disable() // rest apiì´ë¯€ë¡œ csrf ë³´ì•ˆì´ í•„ìš”ì—†ìœ¼ë¯€ë¡œ disable처리.
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS) // jwt token으로 ì¸ì¦í• 것ì´ë¯€ë¡œ 세션필요없으므로 ìƒì„±ì•ˆí•¨.
.and()
.authorizeRequests() // ë‹¤ìŒ ë¦¬í€˜ìŠ¤íŠ¸ì— ëŒ€í•œ 사용권한 ì²´í¬
.antMatchers("/*/signin", "/*/signup").permitAll() // 가입 ë° ì¸ì¦ 주소는 누구나 ì ‘ê·¼ê°€ëŠ¥
.antMatchers(HttpMethod.GET, "/exception/**", "helloworld/**").permitAll() // hellowworldë¡œ 시작하는 GETìš”ì² ë¦¬ì†ŒìŠ¤ëŠ” 누구나 ì ‘ê·¼ê°€ëŠ¥
.anyRequest().hasRole("USER") // 그외 나머지 ìš”ì²ì€ ëª¨ë‘ ì¸ì¦ëœ 회ì›ë§Œ ì ‘ê·¼ 가능
.and()
.exceptionHandling().authenticationEntryPoint(new CustomAuthenticationEntryPoint())
.and()
.addFilterBefore(new JwtAuthenticationFilter(jwtTokenProvider), UsernamePasswordAuthenticationFilter.class); // jwt token 필터를 id/password ì¸ì¦ í•„í„° ì „ì— ë„£ì–´ë¼.
}
Swagger Test
3ë²ˆì— ëŒ€í•œ í•´ê²°ì±…
3ë²ˆì€ Jwtí† í°ì€ ì •ìƒì´ë¼ëŠ” ê°€ì •í•˜ì— Jwtí† í°ì´ 가지지 못한 ê¶Œí•œì˜ ë¦¬ì†ŒìŠ¤ë¥¼ ì ‘ê·¼í• ë•Œ ë°œìƒí•˜ëŠ” 오류입니다. ì´ ê²½ìš°ì—는 SpringSecurityì—ì„œ ì œê³µí•˜ëŠ” AccessDeniedHandler를 ìƒì†ë°›ì•„ 커스터 마ì´ì§• 해야 합니다. 예외가 ë°œìƒí• 경우 handlerì—서는 /exception/accessdeniedë¡œ í¬ì›Œë”©ë˜ë„ë¡ í•˜ì˜€ìŠµë‹ˆë‹¤.
CustomAccessDeniedHandler ìƒì„±
package com.rest.api.config.security;
import lombok.extern.slf4j.Slf4j;
import org.springframework.security.access.AccessDeniedException;
import org.springframework.security.web.access.AccessDeniedHandler;
import org.springframework.stereotype.Component;
import javax.servlet.RequestDispatcher;
import javax.servlet.ServletException;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
@Slf4j
@Component
public class CustomAccessDeniedHandler implements AccessDeniedHandler {
@Override
public void handle(HttpServletRequest request, HttpServletResponse response, AccessDeniedException exception) throws IOException,
ServletException {
response.sendRedirect("/exception/accessdenied");
}
}
ExceptionController ìˆ˜ì •
위ì—ì„œ ìƒì„±í•œ ExceptionControllerì— ë‹¤ìŒ ë‚´ìš©ì„ ì¶”ê°€í•©ë‹ˆë‹¤. ì´ë¯¸ 존재하는 Exceptionì´ë¯€ë¡œ 커스텀 Exceptionì€ ë”°ë¡œ 만들지 ì•Šê³ ê¸°ì¡´ AccessDeniedExceptionì„ ë°œìƒì‹œí‚µë‹ˆë‹¤.
@GetMapping(value = "/accessdenied")
public CommonResult accessdeniedException() {
throw new AccessDeniedException("");
}
Message 내용 추가
// exception_ko.yml accessDenied: code: "-1003" msg: "ë³´ìœ í•œ 권한으로 ì ‘ê·¼í• ìˆ˜ 없는 리소스 입니다." // exception_en.yml accessDenied: code: "-1003" msg: "A resource that can not be accessed with the privileges it has."
ExceptionAdvice 내용 추가
@ExceptionHandler(AccessDeniedException.class)
public CommonResult AccessDeniedException(HttpServletRequest request, AccessDeniedException e) {
return responseService.getFailResult(Integer.valueOf(getMessage("accessDenied.code")), getMessage("accessDenied.msg"));
}
SpringSecurityConfigurationì— CustomAccessDeniedHandler ì„¤ì • 추가
테스트를 위해 /users api는 ROLE_ADMIN 권한만 ì ‘ê·¼ 가능하게 처리해 놓습니다.
.antMatchers(“/*/users”).hasRole(“ADMIN”)
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.httpBasic().disable() // rest api ì´ë¯€ë¡œ ê¸°ë³¸ì„¤ì • 사용안함. ê¸°ë³¸ì„¤ì •ì€ ë¹„ì¸ì¦ì‹œ 로그ì¸í¼ 화면으로 리다ì´ë ‰íŠ¸ ëœë‹¤.
.csrf().disable() // rest apiì´ë¯€ë¡œ csrf ë³´ì•ˆì´ í•„ìš”ì—†ìœ¼ë¯€ë¡œ disable처리.
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS) // jwt token으로 ì¸ì¦í• 것ì´ë¯€ë¡œ 세션필요없으므로 ìƒì„±ì•ˆí•¨.
.and()
.authorizeRequests() // ë‹¤ìŒ ë¦¬í€˜ìŠ¤íŠ¸ì— ëŒ€í•œ 사용권한 ì²´í¬
.antMatchers("/*/signin", "/*/signup").permitAll() // 가입 ë° ì¸ì¦ 주소는 누구나 ì ‘ê·¼ê°€ëŠ¥
.antMatchers(HttpMethod.GET, "/exception/**", "helloworld/**").permitAll() // hellowworldë¡œ 시작하는 GETìš”ì² ë¦¬ì†ŒìŠ¤ëŠ” 누구나 ì ‘ê·¼ê°€ëŠ¥
.antMatchers("/*/users").hasRole("ADMIN")
.anyRequest().hasRole("USER") // 그외 나머지 ìš”ì²ì€ ëª¨ë‘ ì¸ì¦ëœ 회ì›ë§Œ ì ‘ê·¼ 가능
.and()
.exceptionHandling().accessDeniedHandler(new CustomAccessDeniedHandler())
.and()
.exceptionHandling().authenticationEntryPoint(new CustomAuthenticationEntryPoint())
.and()
.addFilterBefore(new JwtAuthenticationFilter(jwtTokenProvider), UsernamePasswordAuthenticationFilter.class); // jwt token 필터를 id/password ì¸ì¦ í•„í„° ì „ì— ë„£ì–´ë¼.
}
Swagger Test
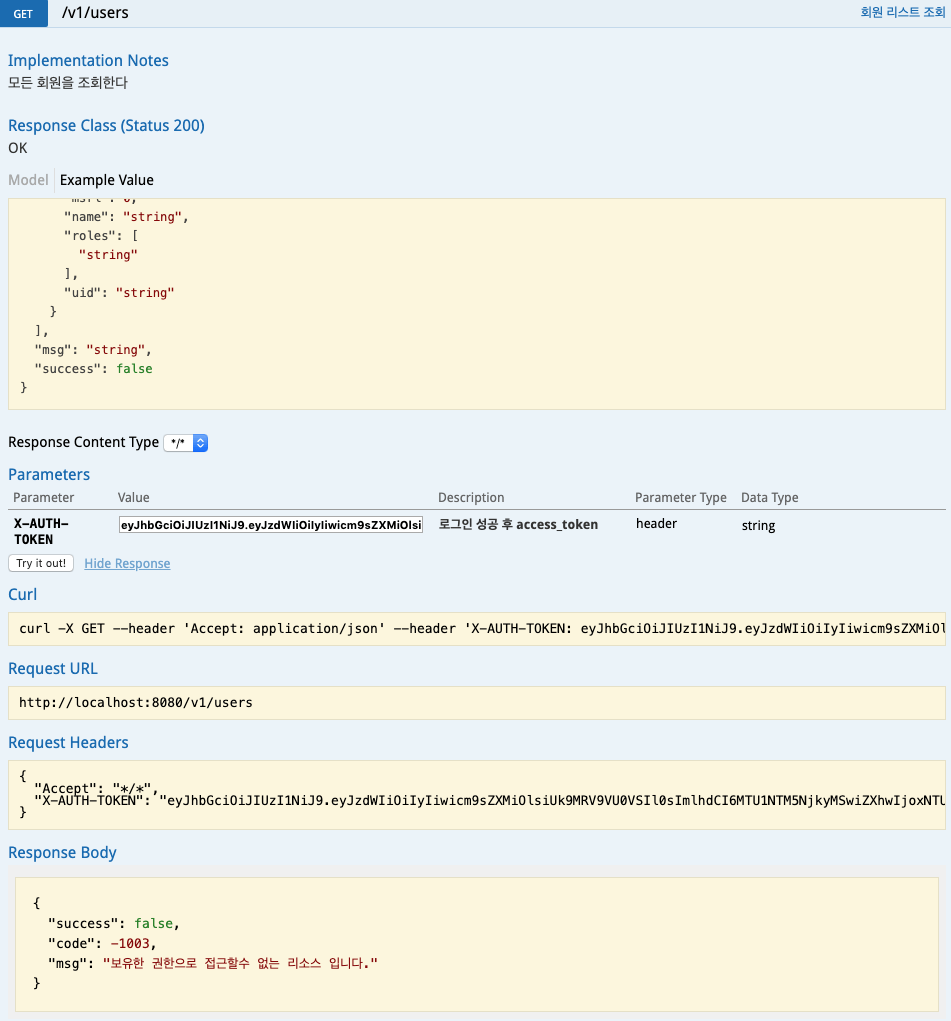
예외 처리 ê³ ë„화까지 잘 ì ìš©ë˜ì—ˆìŒì„ 확ì¸í•˜ì˜€ìŠµë‹ˆë‹¤. ì´ì œ 서버는 ì–´ëŠ ì •ë„ì˜ ë³´ì•ˆì„±ì„ ê°–ì¶”ê²Œ ë˜ì—ˆìŠµë‹ˆë‹¤. SpringSecurity를 ì 용하지 ì•Šê³ ë™ì¼í•œ 프로세스를 처ìŒë¶€í„° ë§Œë“¤ë ¤ê³ í–ˆìœ¼ë©´, ë§Žì€ ê³ ë‚œê³¼ 예외ìƒí™©ì— 대한 대처를 위해 ìˆ˜ë§Žì€ ì‹œê°„ê³¼ ë…¸ë ¥ì´ í•„ìš”í–ˆì„ ê²ƒìž…ë‹ˆë‹¤. ê·¸ë ‡ì§€ë§Œ SpringSecurity를 ì 용하는ë°ë„ ìƒë‹¹í•œ 지ì‹ê³¼ ë…¸ë ¥ì´ í•„ìš”í•©ë‹ˆë‹¤. ë³¸ë¬¸ì— ë‚˜ì˜¨ ë‚´ìš©ì€ Securityì˜ ì¼ë¶€ ë‚´ìš©ì¼ ë¿ìž…니다. ê·¸ë§Œí¼ SpringSecurity ë‚´ìš©ì€ ë°©ëŒ€í•©ë‹ˆë‹¤. ì´ ê¸€ì„ í†µí•´ 서버를 보다 ë” ê²¬ê³ í•˜ê²Œ 만드는 첫걸ìŒì´ ë˜ì—ˆìœ¼ë©´ ì¢‹ê² ìŠµë‹ˆë‹¤.
추가) annotation으로 리소스 ì ‘ê·¼ 권한 ì„¤ì •
실습ì—서는 ë¦¬ì†ŒìŠ¤ì— ëŒ€í•œ ì ‘ê·¼ê¶Œí•œ ì„¤ì •ì‹œ 아래와 ê°™ì´ SecurityConfiguration.javaì˜ configure(HttpSecurity http) 메서드 내부ì—ì„œ authorizeRequests()를 통해 세팅하였습니다. ì´ë ‡ê²Œ 하면 ë¦¬ì†ŒìŠ¤ì˜ ê¶Œí•œì„ ì¤‘ì•™ê´€ë¦¬í•œë‹¤ëŠ” ì ì—ì„œ ì´ì ì´ ìžˆëŠ”ë°ìš”. 추가로 Springì—서는 annotationìœ¼ë¡œë„ ê¶Œí•œ ì„¤ì •ì´ ê°€ëŠ¥í•˜ë„ë¡ ì§€ì›í•˜ê³ 있습니다. ê°ê°ì˜ ë°©ì‹ì€ 장단ì ì´ ìžˆìœ¼ë¯€ë¡œ ìƒí™©ì— ë”°ë¼ ì í•©í•œ ë°©ë²•ì„ ì±„íƒí•´ 사용하면 ë 것 같습니다.
@Override
protected void configure(HttpSecurity http) throws Exception {
http
// ìƒëžµ...
.and()
.authorizeRequests() // ë‹¤ìŒ ë¦¬í€˜ìŠ¤íŠ¸ì— ëŒ€í•œ 사용권한 ì²´í¬
.antMatchers("/*/signin", "/*/signin/**", "/*/signup", "/*/signup/**", "/social/**").permitAll() // 가입 ë° ì¸ì¦ 주소는 누구나 ì ‘ê·¼ê°€ëŠ¥
.antMatchers(HttpMethod.GET, "/exception/**", "/helloworld/**","/actuator/health", "/v1/board/**", "/favicon.ico").permitAll() // 등ë¡ëœ GETìš”ì² ë¦¬ì†ŒìŠ¤ëŠ” 누구나 ì ‘ê·¼ê°€ëŠ¥
.anyRequest().hasRole("USER") // 그외 나머지 ìš”ì²ì€ ëª¨ë‘ ì¸ì¦ëœ 회ì›ë§Œ ì ‘ê·¼ 가능
// ìƒëžµ...
}
@PreAuthorize, @Secured
권한 ì„¤ì •ì´ í•„ìš”í•œ 리소스(실습ì—서는 Controllerì˜ ê° ë©”ì„œë“œì— í•´ë‹¹)ì— @PreAuthorize, @Securedë¡œ ê¶Œí•œì„ ì„¸íŒ…í• ìˆ˜ 있습니다. 둘다 ê°™ì€ ì—í• ì„ í•˜ì§€ë§Œ 아래와 ê°™ì€ ì°¨ì´ê°€ 있습니다.
@PreAuthorize
í‘œí˜„ì‹ ì‚¬ìš© 가능
ex) @PreAuthorize(“hasRole(‘ROLE_USER’) and hasRole(‘ROLE_ADMIN’)”)
@Secured
í‘œí˜„ì‹ ì‚¬ìš© 불가능
ex) @Secured({“ROLE_USER”,”ROLE_ADMIN”})
annotation으로 ê¶Œí•œì„¤ì •ì„ í•˜ë ¤ë©´ GlobalMethodSecurity를 활성화해야 합니다. 아래와 ê°™ì´ SecurityConfiguration ìƒë‹¨ì— @EnableGlobalMethodSecurity(securedEnabled = true, prePostEnabled = true)를 추가합니다. ê·¸ë¦¬ê³ configure 메서드 안ì—ì„œ authorizeRequest() ì„¤ì •ì€ ì£¼ì„ ì²˜ë¦¬í•˜ê±°ë‚˜ ì‚ì œí•©ë‹ˆë‹¤.
@EnableGlobalMethodSecurity(securedEnabled = true, prePostEnabled = true)
@RequiredArgsConstructor
@Configuration
public class SecurityConfiguration extends WebSecurityConfigurerAdapter {
ìƒëžµ...
@Override
protected void configure(HttpSecurity http) throws Exception {
http
.httpBasic().disable() // rest api ì´ë¯€ë¡œ ê¸°ë³¸ì„¤ì • 사용안함. ê¸°ë³¸ì„¤ì •ì€ ë¹„ì¸ì¦ì‹œ 로그ì¸í¼ 화면으로 리다ì´ë ‰íŠ¸ ëœë‹¤.
.csrf().disable() // rest apiì´ë¯€ë¡œ csrf ë³´ì•ˆì´ í•„ìš”ì—†ìœ¼ë¯€ë¡œ disable처리.
.sessionManagement().sessionCreationPolicy(SessionCreationPolicy.STATELESS) // jwt token으로 ì¸ì¦í• 것ì´ë¯€ë¡œ 세션필요없으므로 ìƒì„±ì•ˆí•¨.
// .and()
// .authorizeRequests() // ë‹¤ìŒ ë¦¬í€˜ìŠ¤íŠ¸ì— ëŒ€í•œ 사용권한 ì²´í¬
// .antMatchers("/*/signin", "/*/signin/**", "/*/signup", "/*/signup/**", "/social/**").permitAll() // 가입 ë° ì¸ì¦ 주소는 누구나 ì ‘ê·¼ê°€ëŠ¥
// .antMatchers(HttpMethod.GET, "/exception/**", "/helloworld/**","/actuator/health", "/v1/board/**", "/favicon.ico").permitAll() // 등ë¡ëœ GETìš”ì² ë¦¬ì†ŒìŠ¤ëŠ” 누구나 ì ‘ê·¼ê°€ëŠ¥
// .anyRequest().hasRole("USER") // 그외 나머지 ìš”ì²ì€ ëª¨ë‘ ì¸ì¦ëœ 회ì›ë§Œ ì ‘ê·¼ 가능
.and()
.exceptionHandling().accessDeniedHandler(new CustomAccessDeniedHandler())
.and()
.exceptionHandling().authenticationEntryPoint(new CustomAuthenticationEntryPoint())
.and()
.addFilterBefore(new JwtAuthenticationFilter(jwtTokenProvider), UsernamePasswordAuthenticationFilter.class); // jwt token 필터를 id/password ì¸ì¦ í•„í„° ì „ì— ë„£ì–´ë¼.
}
ìƒëžµ ...
}
Controllerì— ê¶Œí•œì„ ì„¤ì •í•©ë‹ˆë‹¤. 만약 Controller ë‚´ë¶€ì˜ ëª¨ë“ ë¦¬ì†ŒìŠ¤ì— ëŒ€í•˜ì—¬ ì¼ê´„ë¡œ ë™ì¼í•œ ê¶Œí•œì„ ì„¤ì •í• ê²ƒì´ë©´ Controller ìƒë‹¨ì— annotationì„ ì„¸íŒ…í•©ë‹ˆë‹¤.
@PreAuthorize("hasRole('ROLE_USER')") ë˜ëŠ” @Secured("ROLE_USER")
@Api(tags = {"2. User"})
@RequiredArgsConstructor
@RestController
@RequestMapping(value = "/v1")
public class UserController {
ë‚´ìš© ìƒëžµ....
}
만약 ê°ê°ì˜ 리소스마다 ê¶Œí•œì„ ì„¤ì •í•´ì•¼ 하면 해당 메서드 ìœ„ì— annotationì„ ì„¸íŒ…í•˜ë©´ ë©ë‹ˆë‹¤.
@Api(tags = {"2. User"})
@RequiredArgsConstructor
@RestController
@RequestMapping(value = "/v1")
public class UserController {
private final UserJpaRepo userJpaRepo;
private final ResponseService responseService; // 결과를 ì²˜ë¦¬í• Service
@Secured("ROLE_USER")
@ApiImplicitParams({
@ApiImplicitParam(name = "X-AUTH-TOKEN", value = "ë¡œê·¸ì¸ ì„±ê³µ 후 access_token", required = true, dataType = "String", paramType = "header")
})
@ApiOperation(value = "íšŒì› ë¦¬ìŠ¤íŠ¸ 조회", notes = "ëª¨ë“ íšŒì›ì„ 조회한다")
@GetMapping(value = "/users")
public ListResult<User> findAllUser() {
// ê²°ê³¼ë°ì´í„°ê°€ 여러건ì¸ê²½ìš° getListResult를 ì´ìš©í•´ì„œ 결과를 ì¶œë ¥í•œë‹¤.
return responseService.getListResult(userJpaRepo.findAll());
}
@PreAuthorize("hasRole('ROLE_USER')")
@ApiImplicitParams({
@ApiImplicitParam(name = "X-AUTH-TOKEN", value = "ë¡œê·¸ì¸ ì„±ê³µ 후 access_token", required = true, dataType = "String", paramType = "header")
})
@ApiOperation(value = "íšŒì› ë‹¨ê±´ 조회", notes = "회ì›ë²ˆí˜¸(msrl)ë¡œ 회ì›ì„ 조회한다")
@GetMapping(value = "/user")
public SingleResult<User> findUser() {
// SecurityContextì—ì„œ ì¸ì¦ë°›ì€ 회ì›ì˜ ì •ë³´ë¥¼ 얻어온다.
Authentication authentication = SecurityContextHolder.getContext().getAuthentication();
String id = authentication.getName();
// ê²°ê³¼ë°ì´í„°ê°€ 단ì¼ê±´ì¸ê²½ìš° getSingleResult를 ì´ìš©í•´ì„œ 결과를 ì¶œë ¥í•œë‹¤.
return responseService.getSingleResult(userJpaRepo.findByUid(id).orElseThrow(CUserNotFoundException::new));
}
ìƒëžµ...
}
위ì—ì„œ annotation으로 ê¶Œí•œì„ ì„¤ì •í•œ 리소스 외 나머지 ë¦¬ì†ŒìŠ¤ë“¤ì€ ëˆ„êµ¬ë‚˜ ì ‘ê·¼ 가능한 리소스로 ì„¤ì •ë©ë‹ˆë‹¤.
ìµœì‹ ì†ŒìŠ¤ëŠ” GitHub 사ì´íŠ¸ë¥¼ ì°¸ê³ í•´ 주세요.
https://github.com/codej99/SpringRestApi/tree/feature/security
GitHub Repository를 import하여 Intellij 프로ì 트를 구성하는 ë°©ë²•ì€ ë‹¤ìŒ í¬ìŠ¤íŒ…ì„ ì°¸ê³ í•´ì£¼ì„¸ìš”.
Dockerë¡œ 개발 í™˜ê²½ì„ ë¹ ë¥´ê²Œ 구축하는 ê²ƒë„ ê°€ëŠ¥í•©ë‹ˆë‹¤. ë‹¤ìŒ ë¸”ë¡œê·¸ ë‚´ìš©ì„ ì½ì–´ë³´ì„¸ìš”!
ìŠ¤í”„ë§ api 서버를 ì´ìš©í•˜ì—¬ 웹사ì´íŠ¸ë¥¼ ë§Œë“¤ì–´ë³´ê³ ì‹¶ìœ¼ì‹œë©´ 아래 í¬ìŠ¤íŒ…ì„ ì°¸ê³ í•´ 주세요.














